HP2-Z32 Online Practice Questions and Answers
Refer to the exhibit.

A network administrator enables 802.1X authentication on a VSC. The HP MSM Controller implements the RADIUS server settings shown in the exhibit. Which devices require certificates?
Hot Area:

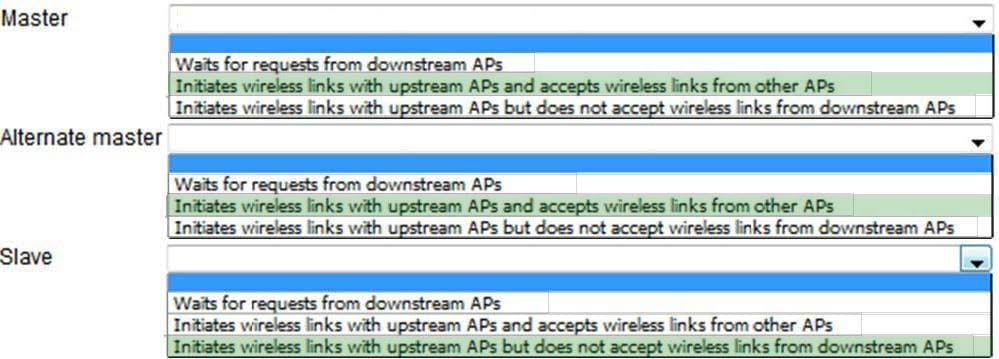
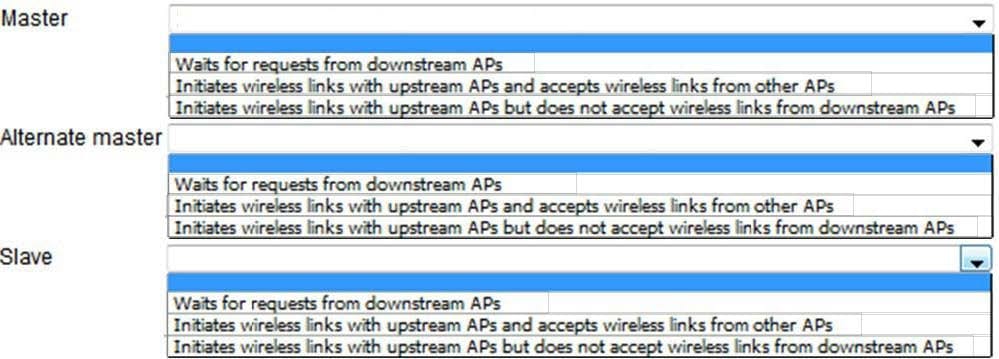
When configuring a wireless mesh, an AP is assigned one of three roles. Match the description to each role.
Hot Area:
When Centralized Access Control is configured as Automatic, when is a user data tunnel created?
A. when more than one controller is on the network that has the same access control configuration
B. when tunnels are manually configured and available
C. when IPSec is set up between two controllers
D. when a synchronized AP and its controller are on different subnets
An MSM administrator creates an access-controlled VSC, which is not the default VSC, on a standalone MSM Controller The controller should implement DHCP relay on this VSC; clients will receive IP addresses from an external DHCP server The DHCP scope for the clients uses 192.168.1.0/24 and sets the default gateway to 192.168.1.1. The 192.168.1.0/24 subnet is reserved for the wireless clients and does not exist in the LAN.
Which requirement applies to this scenario?
A. The guests must log into a web page hosted on an external server to authenticate on this VSC.
B. The 192.168.1.0/24 subnet must be configured on the controllers LAN port.
C. The DHCP server, or its default gateway, needs a route to 192.168.1.0/24 through the MSM Controller.
D. The APs that support this VSC must receive IP addresses from the same DHCP server as the clients.
A company has an HP MSM solution that consists of an HP MSM760 Access Controller and controlled HP MSM APs. The solution includes a VSC that enforces local Web-Auth (HTML- based user login) using web pages and guest accounts configured on the controller The company wants to prevent guests from logging in after normal business hours. Which action describes the correct setting to meet these requirements?
A. Create a subscription plan that specifies the valid login times, and apply the plan to the guest accounts.
B. Configure the valid login times in a RADIUS server policy, which then apply to the site or to individual user accounts.
C. Set the valid login times in the Virtual Service Community (VSC) used by guests.
D. Set the valid login times in the global access control settings of the controller (Controller? Public access > Access control).
What is the primary difference between AES-CCMP and TKIP?
A. With AES-CCMP, each station generates its PMK as part of the 802.1X authentication process.
B. With TKIP, the station uses the same key to secure data and the MIC.
C. AES-CCMP uses a 254-bit key stream, while TKIP uses a 128-bit key stream.
D. AES-CCMP uses a stronger encryption algorithm than that provided by TKIP.
Two HP MSM Controllers have established a team. The team manager fails. Which statements correctly describe the failover behavior? (Select two.)
A. APs managed by the team manager no longer appear in the team's web browser interface, but the APs continue to support non-access-controlled APs.
B. Clients connected to non-access controlled VSCs do not experience any loss of connectivity.
C. Administrators can continue to configure settings on the team by using the interim manager.
D. Clients connected to access-controlled VSCs do not experience any loss of connectivity.
E. Administrators can contact the team IP address and monitor controlled APs in the web browser interface.
Which standard supports channel bonding?
A. 802.11g
B. 802.11n
C. 802.11a
D. 802.11b
A company wants to use MSM765 zl Controllers in a team solution that supports 750 MSM APs. What must the company purchase for this solution?
A. Six MSM765 zJ Controllers
B. Five MSM765 zl Controllers and an additional Premium license for each one
C. Four MSM765 zl Controllers and an additional Premium license for each one
D. Four MSU765 zl Controllers
The HP MSM Controller features a free access option.
When a user clicks the Free Access button, the controller creates a user account for the guest. What is one feature of that account?
A. The account is copied to Guest Management Software (GMS) if the MSM Controller is synchronized with that application.
B. The username and password are derived from entries that the user types into the login page.
C. The account has an expiry time that is derived from the session timeout value in the default AC profile.
D. The account has an expiry time that is derived from the free access validity duration.
Which cell plan is designed property to minimize interference and enable seamless roaming?
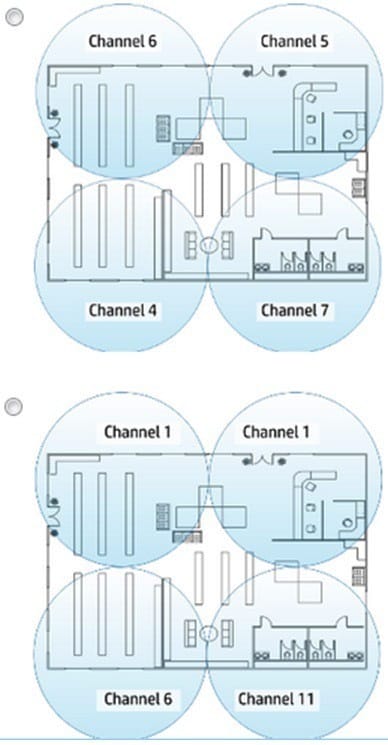
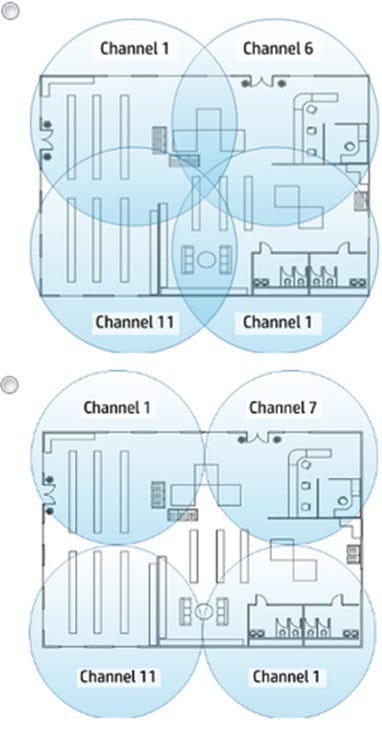
A. Exhibit A
B. Exhibit B
C. Exhibit C
D. Exhibit D
Why is WPA2-PSK less secure than 802.1X with WPA2-PSK?
A. Multiple users share the same password on WPA2-PSK.
B. 802.1X with WPA2-PSK uses a 2048-bit key rather than a 1024-bit key
C. WPA2-PSK sends the initial key in clear text.
D. 802.1X with WPA2-PSK uses a more secure method for exchanging keys
A company needs a WLAN for its employees Network administrators are planning a non-access- controlled VSC that enforces WPA2 and 802.1x. The network administrators want to assign wireless clients to VLAN 10 in building 1 and to VLAN 20 in building 2.
What is the proper design?
A. Two VSCs each or which specifies a different egress VLAN
B. One VSC that specifies two egress VLANs
C. Two VSCs each of which specifies a different ingress VLAN
D. One VSC that is bound to two AP groups using different egress VLANs
What distinguishes HP MSM APs that implement a dynamic mesh link from HP MSM APs that implement a static link?
A. The APs using the dynamic link can automatically negotiate the VLAN for egressing user traffic.
B. The APs using the dynamic link can establish new links between each other if one of the APs fails.
C. The APs using the dynamic link can authenticate each other with 802.1X and receive the key for encrypting traffic sent on the link in that way.
D. The APs using the dynamic link can negotiate type of encryption that they will use dynamically.
Refer to the exhibit.
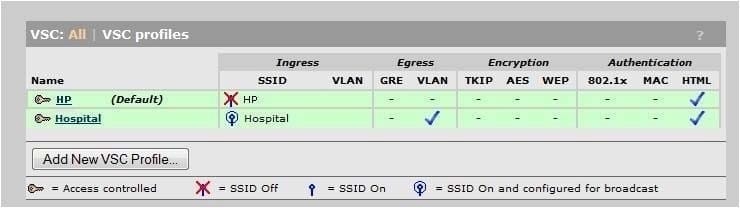
A hospital has an HP MSM solution that provides guest access, including Web-Auth to the local login pages of the controller. The exhibit shows the Hospital VSC used by guests. The network administrators have created an isolated guest VLAN, VLAN 100. The HP MSM Controller should provide the same guest services to wired clients connected to this VLAN. The network administrator has configured a network profile and the required settings. How should the controller apply the profile in the VSC?
A. As the egress VLAN for unauthenticated users
B. As the egress VLAN for authenticated users
C. As the ingress VLAN
D. As the egress VLAN for intercepted users