PCCET Online Practice Questions and Answers
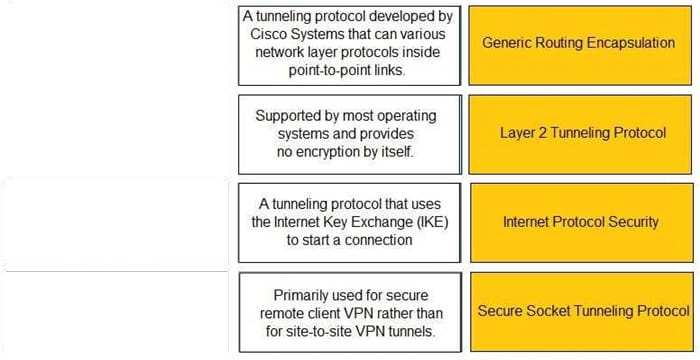
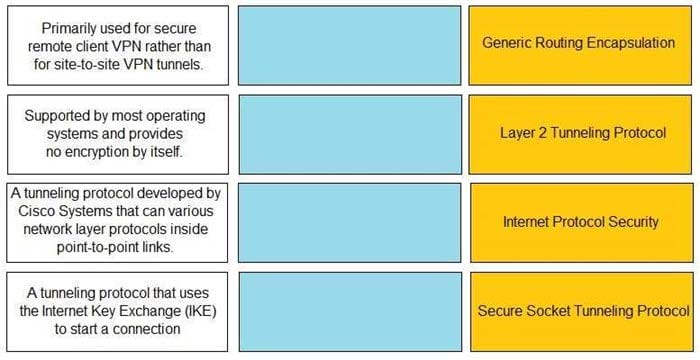
DRAG DROP
Match the description with the VPN technology.
Select and Place:
Which Palo Alto Networks tools enable a proactive, prevention-based approach to network automation that accelerates security analysis?
A. MineMeld
B. AutoFocus
C. WildFire
D. Cortex XDR
In addition to local analysis, what can send unknown files to WildFire for discovery and deeper analysis to rapidly detect potentially unknown malware?
A. Cortex XDR
B. AutoFocus
C. MineMild
D. Cortex XSOAR
Which aspect of a SaaS application requires compliance with local organizational security policies?
A. Types of physical storage media used
B. Data-at-rest encryption standards
C. Acceptable use of the SaaS application
D. Vulnerability scanning and management
What is the key to "taking down" a botnet?
A. prevent bots from communicating with the C2
B. install openvas software on endpoints
C. use LDAP as a directory service
D. block Docker engine software on endpoints
Which key component is used to configure a static route?
A. router ID
B. enable setting
C. routing protocol
D. next hop IP address
Which pillar of Prisma Cloud application security addresses ensuring that your cloud resources and SaaS applications are correctly configured?
A. visibility, governance, and compliance
B. network protection
C. dynamic computing
D. compute security
Which item accurately describes a security weakness that is caused by implementing a "ports first" data security solution in a traditional data center?
A. You may have to use port numbers greater than 1024 for your business-critical applications.
B. You may have to open up multiple ports and these ports could also be used to gain unauthorized entry into your datacenter.
C. You may not be able to assign the correct port to your business-critical applications.
D. You may not be able to open up enough ports for your business-critical applications which will increase the attack surface area.
Which characteristic of serverless computing enables developers to quickly deploy application code?
A. Uploading cloud service autoscaling services to deploy more virtual machines to run their application code based on user demand
B. Uploading the application code itself, without having to provision a full container image or any OS virtual machine components
C. Using cloud service spot pricing to reduce the cost of using virtual machines to run their application code
D. Using Container as a Service (CaaS) to deploy application containers to run their code.
Which not-for-profit organization maintains the common vulnerability exposure catalog that is available through their public website?
A. Department of Homeland Security
B. MITRE
C. Office of Cyber Security and Information Assurance
D. Cybersecurity Vulnerability Research Center
Which of the following is a service that allows you to control permissions assigned to users in order for them to access and utilize cloud resources?
A. User-ID
B. Lightweight Directory Access Protocol (LDAP)
C. User and Entity Behavior Analytics (UEBA)
D. Identity and Access Management (IAM)
Routing Information Protocol (RIP), uses what metric to determine how network traffic should flow?
A. Shortest Path
B. Hop Count
C. Split Horizon
D. Path Vector
What is the primary security focus after consolidating data center hypervisor hosts within trust levels?
A. control and protect inter-host traffic using routers configured to use the Border Gateway Protocol (BGP) dynamic routing protocol
B. control and protect inter-host traffic by exporting all your traffic logs to a sysvol log server using the User Datagram Protocol (UDP)
C. control and protect inter-host traffic by using IPv4 addressing
D. control and protect inter-host traffic using physical network security appliances
Which tool supercharges security operations center (SOC) efficiency with the world's most comprehensive operating platform for enterprise security?
A. Prisma SAAS
B. WildFire
C. Cortex XDR
D. Cortex XSOAR
Which option describes the "selective network security virtualization" phase of incrementally transforming data centers?
A. during the selective network security virtualization phase, all intra-host communication paths are strictly controlled
B. during the selective network security virtualization phase, all intra-host traffic is forwarded to a Web proxy server
C. during the selective network security virtualization phase, all intra-host traffic is encapsulated and encrypted using the IPSEC protocol
D. during the selective network security virtualization phase, all intra-host traffic is load balanced