NSE7_SDW-7.0 Online Practice Questions and Answers
Which components make up the secure SD-WAN solution?
A. Application, antivirus, and URL, and SSL inspection
B. Datacenter, branch offices, and public cloud
C. FortiGate, FortiManager, FortiAnalyzer, and FortiDeploy
D. Telephone, ISDN, and telecom network.
Refer to the exhibit.
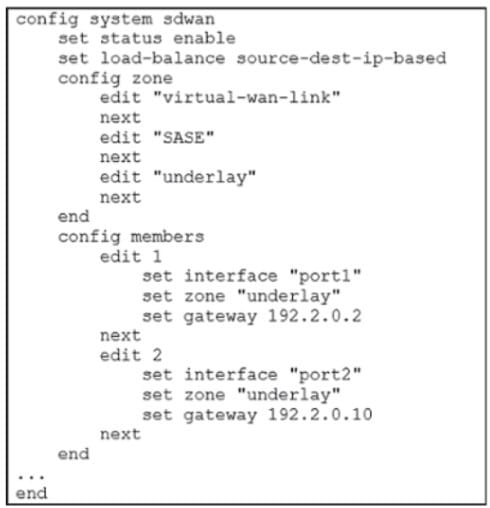
Which algorithm does SD-WAN use to distribute traffic that does not match any of the SD- WAN rules?
A. All traffic from a source IP to a destination IP is sent to the same interface.
B. All traffic from a source IP is sent to the same interface.
C. All traffic from a source IP is sent to the most used interface.
D. All traffic from a source IP to a destination IP is sent to the least used interface.
Refer to the exhibit.
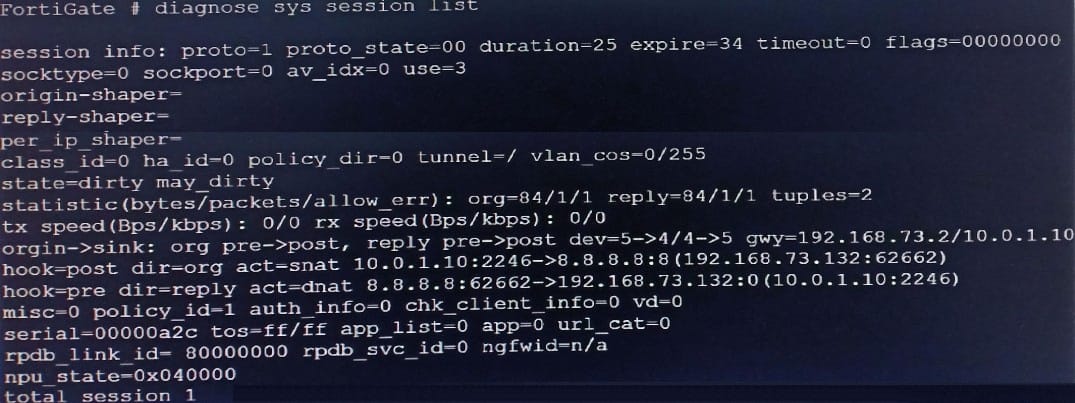
Based on the exhibit, which statement about FortiGate re-evaluating traffic is true?
A. The type of traffic defined and allowed on firewall policy ID 1 is UDP.
B. FortiGate has terminated the session after a change on policy ID 1.
C. Changes have been made on firewall policy ID 1 on FortiGate.
D. Firewall policy ID 1 has source NAT disabled.
Refer to the exhibit.
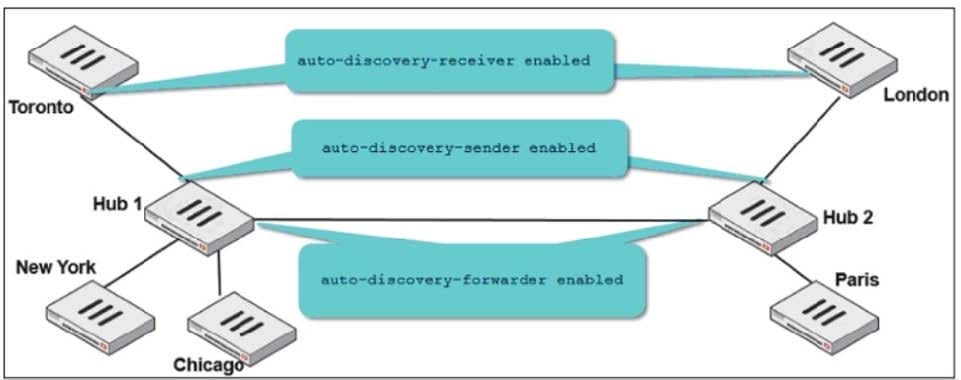
Two hub-and-spoke groups are connected through a site-to-site IPsec VPN between Hub 1 and Hub 2. The administrator configured ADVPN on both hub-and-spoke groups.
Which two outcomes are expected if a user in Toronto sends traffic to London? (Choose two.)
A. London generates an IKE information message that contains the Toronto public IP address.
B. Traffic from Toronto to London triggers the dynamic negotiation of a direct site-to-site VPN.
C. Toronto needs to establish a site-to-site tunnel with Hub 2 to bypass Hub 1.
D. The first packets from Toronto to London are routed through Hub 1 then to Hub 2.
What are the two minimum configuration requirements for an outgoing interface to be selected once the SD-WAN logical interface is enabled? (Choose two )
A. Specify outgoing interface routing cost.
B. Configure SD-WAN rules interface preference.
C. Select SD-WAN balancing strategy.
D. Specify incoming interfaces in SD-WAN rules.
Refer to exhibits.
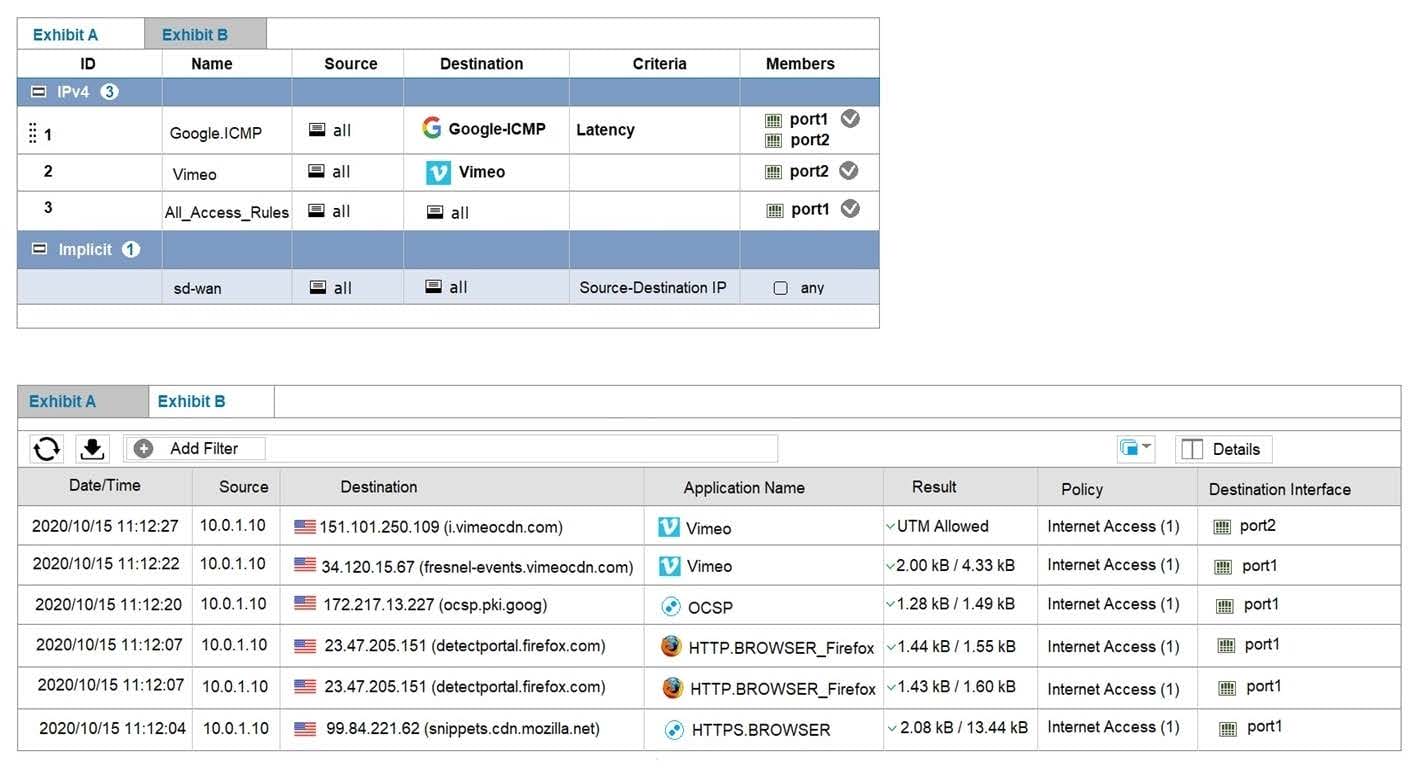
Exhibit A shows the SD-WAN rules and exhibit B shows the traffic logs. The SD-WAN traffic logs reflect how FortiGate processed traffic. Which two statements about how the configured SD-WAN rules are processing traffic are true? (Choose two.)
A. The implicit rule overrides all other rules because parameters widely cover sources and destinations.
B. SD-WAN rules are evaluated in the same way as firewall policies: from top to bottom.
C. The All_Access_Rules rule load balances Vimeo application traffic among SD-WAN member interfaces.
D. The initial session of an application goes through a learning phase in order to apply the correct rule.
Refer to the exhibit.
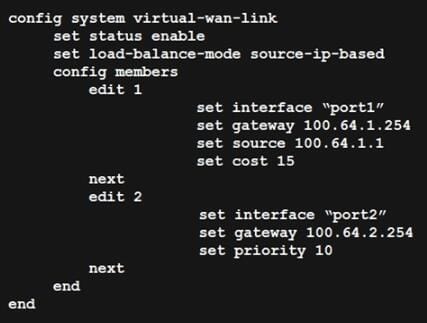
Based on the output shown in the exhibit, which two criteria on the SD-WAN member configuration can be used to select an outgoing interface in an SD-WAN rule? (Choose two.)
A. Set priority 10.
B. Set cost 15.
C. Set load-balance-mode source-ip-ip-based.
D. Set source 100.64.1.1.
Refer to the exhibit.
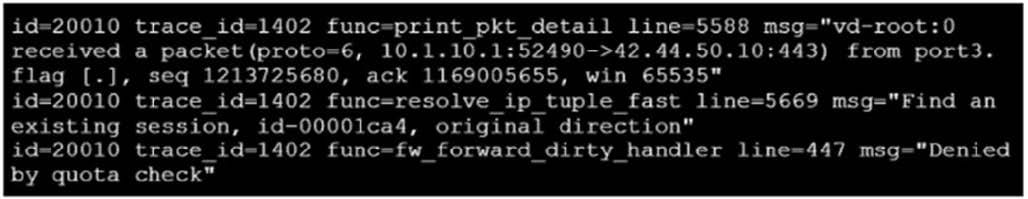
Which conclusion about the packet debug flow output is correct?
A. The number of concurrent sessions for 10.1.10.1 exceeded the maximum number of concurrent sessions configured in the traffic shaper, and the packet was dropped.
B. The number of concurrent sessions for 10.1.10.1 exceeded the maximum number of concurrent sessions configured in the firewall policy, and the packet was dropped.
C. The packet size exceeded the outgoing interface MTU.
D. The total number of daily sessions for 10.1.10.1 exceeded the maximum number of concurrent sessions configured in the traffic shaper, and the packet was dropped.
Refer to the exhibit.
Multiple IPsec VPNs are formed between two hub-and-spokes groups, and site-to-site between Hub 1 and Hub 2 The administrator configured ADVPN on the dual regions topology
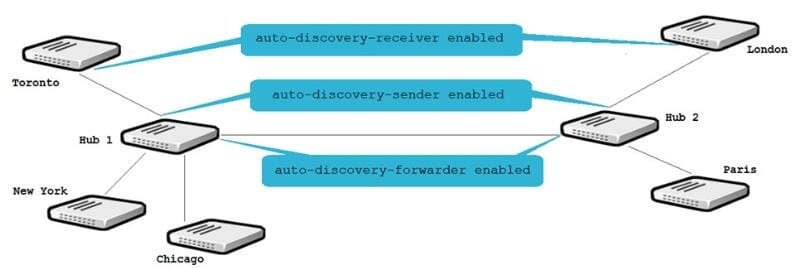
Which two statements are correct if a user in Toronto sends traffic to London? (Choose two )
A. Toronto needs to establish a site-to-site tunnel with Hub 2 to bypass Hub 1.
B. The first packets from Toronto to London are routed through Hub 1 then to Hub 2.
C. London generates an IKE information message that contains the Toronto public IP address.
D. Traffic from Toronto to London triggers the dynamic negotiation of a direct site-to-site VPN.
When attempting to establish an IPsec tunnel to FortiGate, all remote users match the FIRST_VPN IPsec VPN. This includes remote users that want to connect to the SECOND_VPN IPsec VPN. Which two configuration changes must you make on both IPsec VPNs so that remote users can connect to their intended IPsec VPN? (Choose two.)
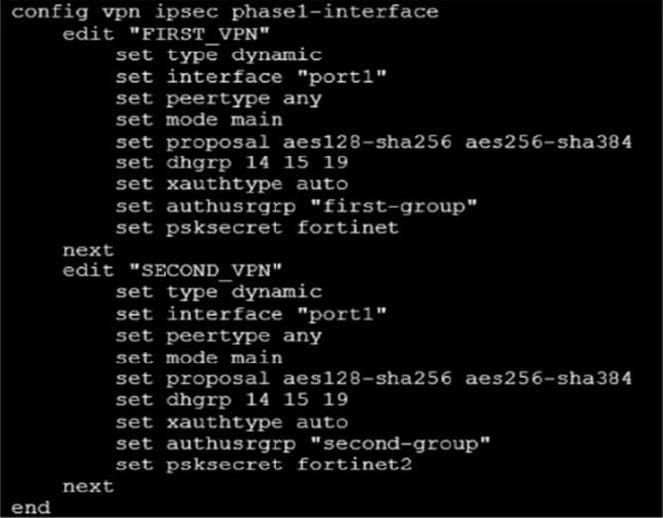
A. Configure different proposals.
B. Configure a unique peer ID.
C. Change the IKE mode to aggressive.
D. Configure different Diffie Hellman groups.
Which action FortiGate performs on traffic that is subject to a per-IP traffic shaper of 10 Mbps?
A. FortiGate shares 10 Mbps of bandwidth equally among all source IP addresses.
B. FortiGate applies traffic shaping to the original traffic direction only.
C. FortiGate limits each source IP address to a maximum bandwidth of 10 Mbps.
D. FortiGate guarantees a minimum of 10 Mbps of bandwidth to each source IP address.
In which two ways does FortiGate learn the FortiManager IP address or FQDN for zero-touch provisioning? (Choose two.)
A. From a FortiGuard definitions update
B. From the central management configuration configured in FortiDeploy
C. From a DHCP server configured with options 240 or 241
D. From another FortiGate device in the same local network
Refer to exhibits. Exhibit A.
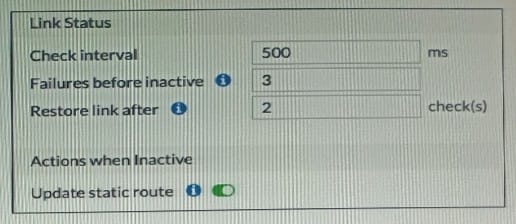
Exhibit B.
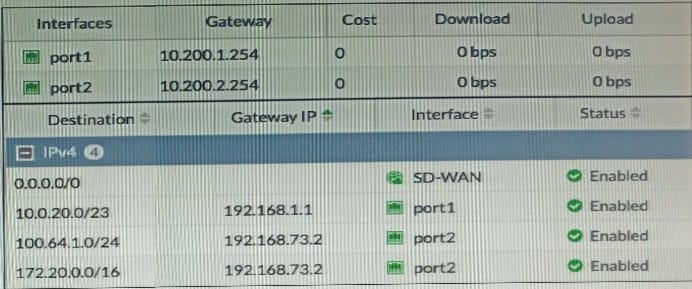
Exhibit A shows the SD-WAN performance SLA and exhibit B shows the SO-WAN interface and the static routes configuration. Port1 and port2 are member interfaces of the SD-WAN, and port2 becomes a dead member after reaching the failure thresholds Which statement about the dead member is correct?
A. Subnets 100 .64.1.0/23 and 172 . 20 . 0. 0/16 are reachable only through port1
B. SD-WAN interface becomes disabled and port1 becomes the WAN interface
C. Dead members require manual administrator access to bring them back alive
D. Port2 might become alive when a single response is received from an SLA server
Which two benefits from using forward error correction (FEC) in IPsec VPNs are true? (Choose two.)
A. FEC transmits the original payload in full to recover the error in transmission.
B. FEC reduces the stress on the remote device buffer to reconstruct packet loss.
C. FEC transmits additional packets as redundant data to the remote device.
D. FEC improves reliability, which overcomes adverse WAN conditions such as noisy links.
Refer to exhibits.
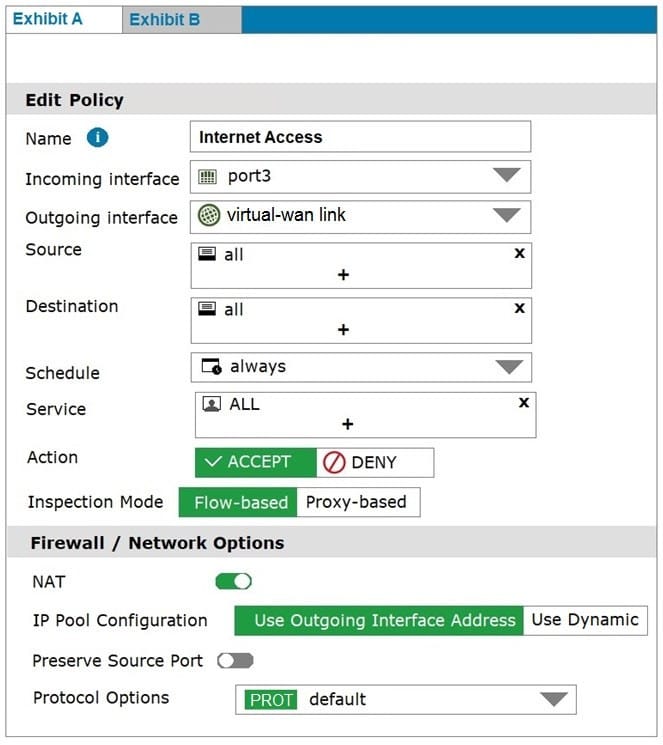
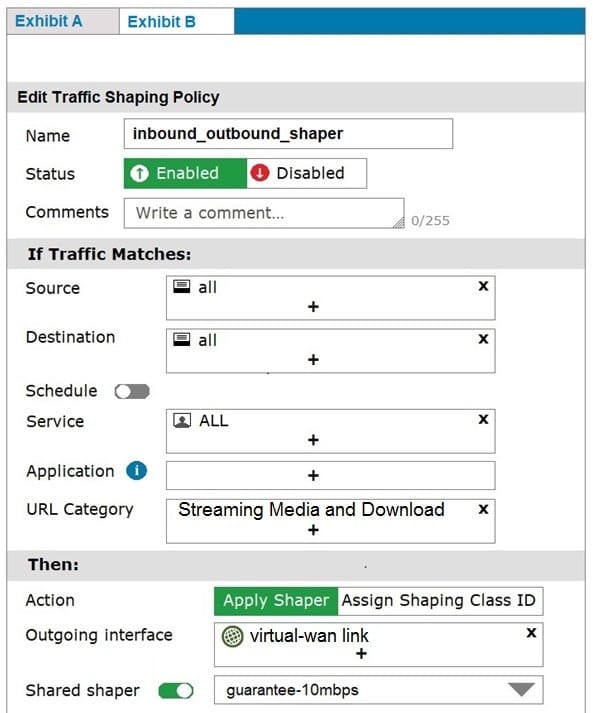
Exhibit A shows the firewall policy and exhibit B shows the traffic shaping policy.
The traffic shaping policy is being applied to all outbound traffic; however, inbound traffic is not being evaluated by the shaping policy.
Based on the exhibits, what configuration change must be made in which policy so that traffic shaping can be applied to inbound traffic?
A. Create a new firewall policy, and the select the SD-WAN zone as Incoming Interface.
B. In the traffic shaping policy, select Assign Shaping Class ID as Action.
C. In the firewall policy, select Proxy-based as Inspection Mode.
D. In the traffic shaping policy, enable Reverse shaper, and then select the traffic shaper to use.
