NSE7_ATP-2.5 Online Practice Questions and Answers
Which samples can FortiClient submit to FortiSandbox for analysis? (Choose two.)
A. Downloads from emails
B. URLs from web requests
C. Command and control traffic D. Files from removable storage
Examine the System Information widget shown in the exhibit, then answer the following question:

Which of the following inspections will FortiSandbox perform on samples submitted for sandboxing? (Choose two.)
A. URL rating on FQDN seen in DNS requests
B. IP reputation check on callback connections
C. Antivirus inspection on downloaded files
D. URL rating on HTTP GET requests
Which advanced threat protection integration solution should you use to protect against out-of-band attack vectors, such as USB drives, used during the delivery stage of the kill chain?
A. FortiGate and FortiSandbox
B. FortiMail and FortiSandbox
C. FortiWeb and FortiSandbox
D. FortiClient and FortiSandbox
Which of the following advanced threat protection are capable of preventing patient-zero infections? (Choose two.)
A. FortiWeb and FortiSandbox
B. FortiClient and FortiSandbox
C. FortiMail and FortiSandbox
D. FortiGate and FortiSandbox
Which of the following scan job report sections are generated by static analysis? (Choose two.)
A. Office Behaviors
B. Launched Processes
C. Registry Changes
D. Virtual Simulator
Examine the FortiClient configuration shown in the exhibit. then answer the following question:
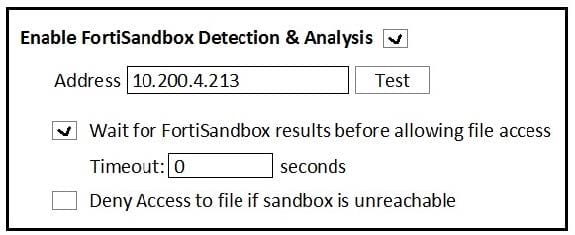
What is the general rule you should follow when configuring the Timeout value for files submitted to FortiSandbox?
A. It should be long enough for FortiSandbox to complete an antivirus scan of files.
B. It should be long enough for FortiSandbox to complete a cloud query of file hashes.
C. It should be long enough for FortiSandbox to complete sandbox analysis of files.
D. It should be long enough for FortiSandbox to complete a static analysis of files.
Which FortiSandbox interfaces can you use for sniffer mode? (Choose two.)
A. port2
B. port3
C. port1
D. port4
Which threats can FortiSandbox inspect when it is deployed in sniffer mode? (Choose three.)
A. Spam emails
B. Known malware
C. Encrypted files
D. Malicious URLs
E. Botnet connections
Examine the CLI configuration, than answer the following question:
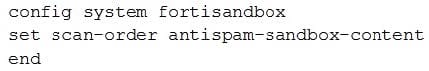
Which of the following statements is true regarding this FortiMail's inspection behavior?
A. Malicious URLs will be removed by antispam and replaced with a message.
B. Suspicious files not detected by antivirus will be inspected by FortiSandbox.
C. Known malicious URLs will be inspected by FortiSandbox.
D. Files are skipped by content profile will be inspected by FortiSandbox.
What advantage does sandboxing provide over traditional virus detection methods?
A. Heuristics detection that can detect new variants of existing viruses.
B. Pattern-based detection that can catch multiple variants of a virus.
C. Full code execution in an isolated and protected environment.
D. Code emulation as packets are handled in real-time.
Examine the FortiGate antivirus log detail shown in the exhibit, then answer the following question:
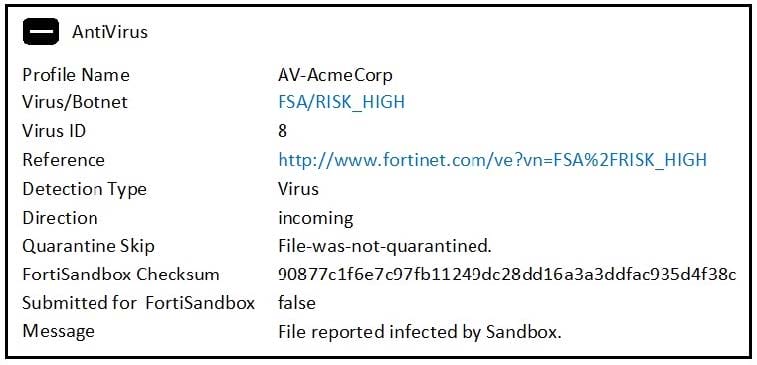
Which of the following statements is true?
A. FortiGate quarantined the file as a malware.
B. The file matched a FortiSandbox-generated malware signature.
C. The file was downloaded from www.fortinet.com.
D. The FSA/RISK_HIGH verdict was generated by FortiSandbox.
Examine the virtual Simulator section of the scan job report shown in the exhibit, then answer the following question:
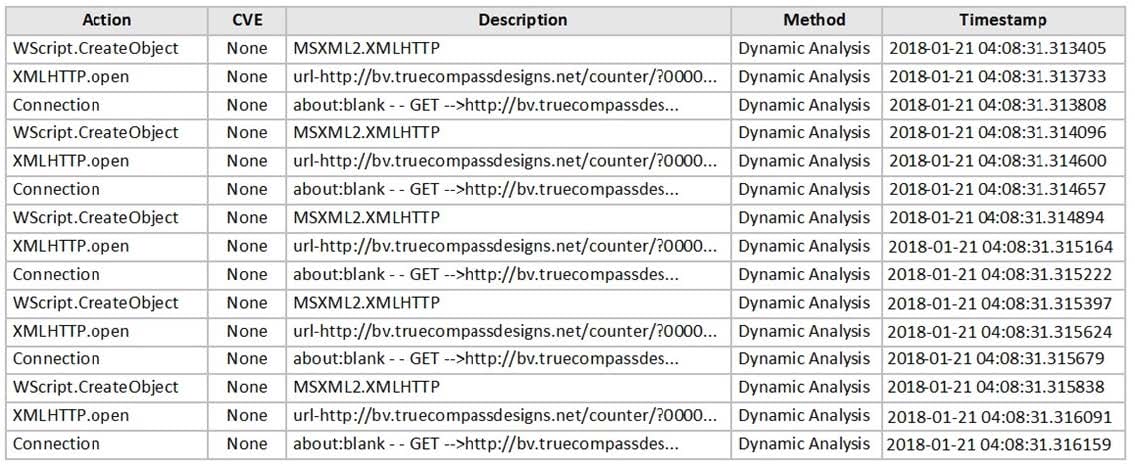
Based on the behavior observed by the virtual simulator, which of the following statements is the most likely scenario?
A. The file contained a malicious image file.
B. The file contained malicious JavaScript.
C. The file contained a malicious macro.
D. The file contained a malicious URL.
Examine the scan job report shown in the exhibit, then answer the following question: Which of the following statements are true regarding this verdict? (Choose two.)
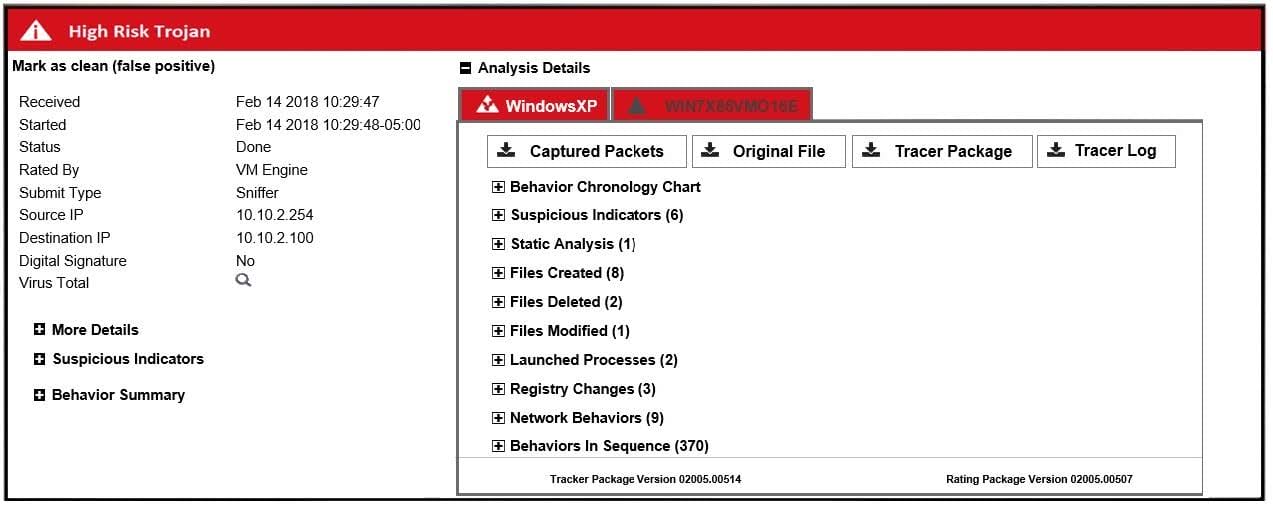
A. The file contained malicious JavaScipt.
B. The file contained a malicious macro.
C. The file was sandboxed in two-guest VMs.
D. The file was extracted using sniffer-mode inspection.
Examine the FortiSandbox configuration on FortiMail shown in the exhibit, then answer the following question:
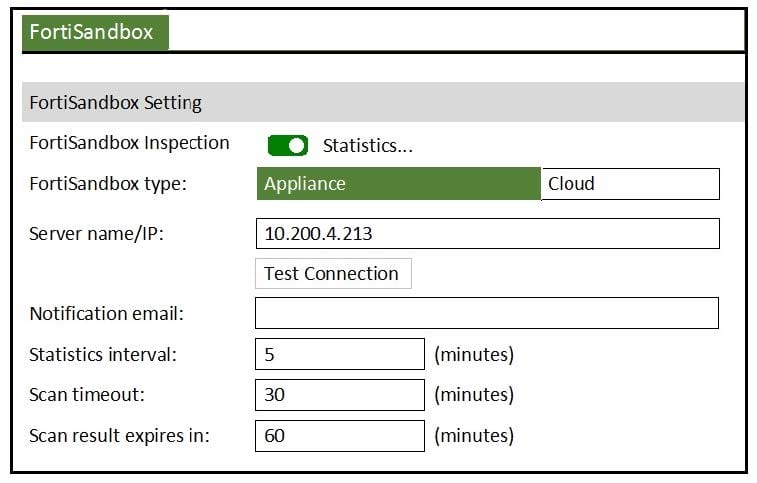
What does the Scan result expires in value specify?
A. How often the local scam results cache will expire on FortiMail.
B. How long FortiMail will wait to send a file or URI to FortiSandbox.
C. How long FortiMail will wait for a scan result from FortiSandbox.
D. How long FortiMail will query FortiSandbox for a scan result.
Which of the following are FortiWeb's roles when integrated with FortiSandbox? (Choose two.)
A. Share threat information
B. Prevent outbreaks
C. Generate a verdict
D. Block known threats
