NSE7_ADA-6.3 Online Practice Questions and Answers
Which two statements about the maximum device limit on FortiSIEM are true? (Choose two.)
A. The device limit is defined per customer and every customer is assigned a fixed number of device limit by the service provider.
B. The device limit is only applicable to enterprise edition.
C. The device limit is based on the license type that was purchased from Fortinet.
D. The device limit is defined for the whole system and is shared by every customer on a service provider edition.
Refer to the exhibit.
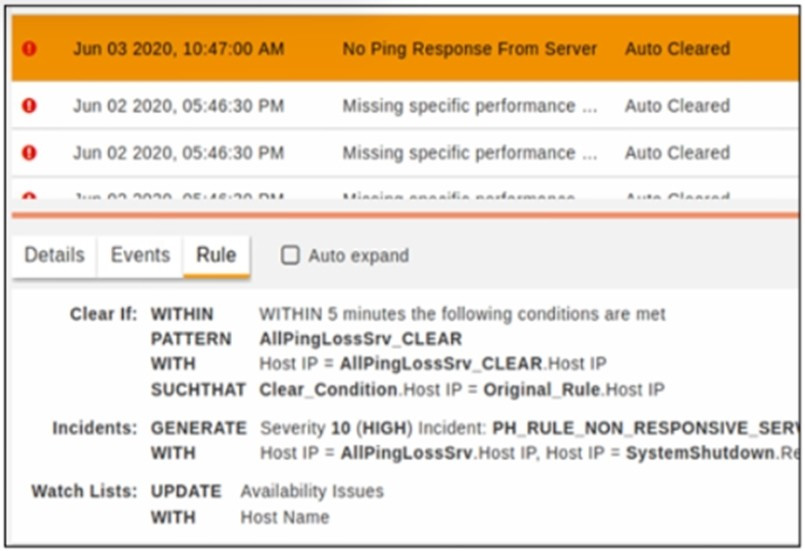
Why was this incident auto cleared?
A. Within five minutes the packet loss percentage dropped to a level where the reporting IP is the same as the host IP
B. The original rule did not trigger within five minutes
C. Within five minutes, the packet loss percentage dropped to a level where the reporting IP is same as the source IP
D. Within five minutes, the packet loss percentage dropped to a level where the host IP of the original rule matches the host IP of the clear condition pattern
Which three statements about collector communication with the FortiSIEM cluster are true? (Choose three.)
A. The only communication between the collector and the supervisor is during the registration process.
B. Collectors communicate periodically with the supervisor node.
C. The supervisor periodically checks the health of the collector.
D. The supervisor does not initiate any connections to the collector node.
E. Collectors upload event data to any node in the worker upload list, but report their health directly to the supervisor node.
Refer to the exhibit.
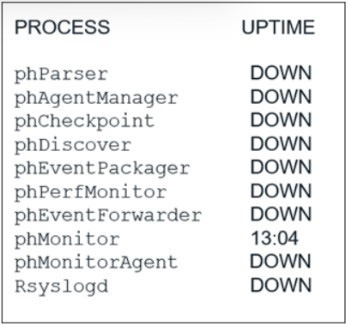
An administrator deploys a new collector for the first time, and notices that all the processes except the phMonitor are down. How can the administrator bring the processes up?
A. The administrator needs to run the command phtools --start all on the collector.
B. Rebooting the collector will bring up the processes.
C. The processes will come up after the collector is registered to the supervisor.
D. The collector was not deployed properly and must be redeployed.
What happens to UEBA events when a user is off-net?
A. The agent will upload the events to the Worker if it cannot upload them to a FortiSIEM collector
B. The agent will cache events locally if it cannot upload them to a FortiSIEM collector
C. The agent will upload the events to the Supervisor if it cannot upload them to a FortiSIEM collector
D. The agent will drop the events if it cannot upload them to a FortiSIEM collector
Which syntax will register a collector to the supervisor?
A. phProvisionCollector --add
B. phProvisionCollector --add
C. phProvisionCollector --add
D. phProvisionCollector --add
Refer to the exhibit. Click on the calculator button.
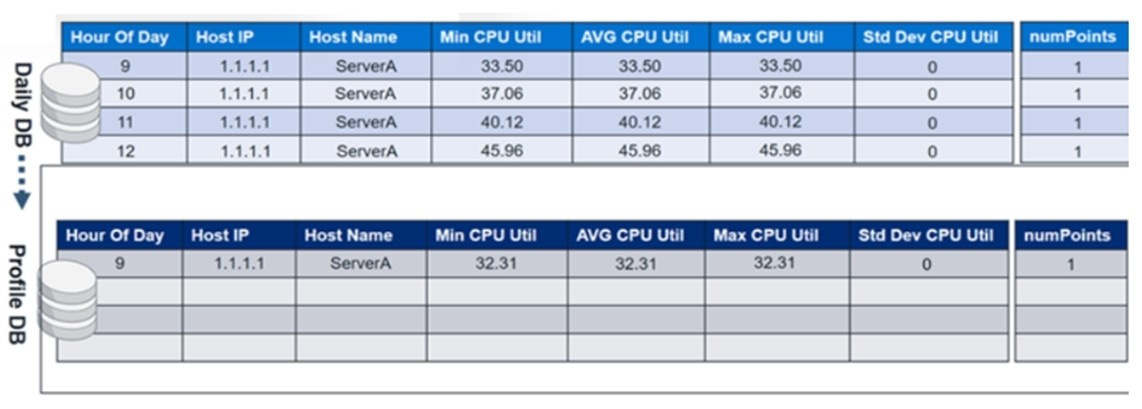
The profile database contains CPU utilization values from day one. At midnight on the second day, the CPU utilization values from the daily database will be merged with the profile database.
In the profile database, in the Hour of Day column where 9 is the value, what will be the updated minimum, maximum, and average CPU utilization values?
A. Min CPU Util=32.31, Max CPU Ucil=33.50 and AVG CPU Util=33.50
B. Min CPU Util=32.31, Max CPU Ucil=33.50 and AVG CPU Util=32.67
C. Min CPU Util=32.31, Max CPU Ucil=32.31 and AVG CPU Util=32.31
D. Min CPU Util=33.50, Max CPU Ucil=33.50 and AVG CPU Util=33.50
Which of the following are two Tactics in the MITRE ATTandCK framework? (Choose two.)
A. Root kit
B. Reconnaissance
C. Discovery
D. BITS Jobs
E. Phishing
What is Tactic in the MITRE ATTandCK framework?
A. Tactic is how an attacker plans to execute the attack
B. Tactic is what an attacker hopes to achieve
C. Tactic is the tool that the attacker uses to compromise a system
D. Tactic is a specific implementation of the technique
How can you empower SOC by deploying FortiSOAR? (Choose three.)
A. Aggregate logs from distributed systems
B. Collaborative knowledge sharing
C. Baseline user and traffic behavior
D. Reduce human error
E. Address analyst skills gap
From where does the rule engine load the baseline data values?
A. The profile report
B. The daily database
C. The profile database
D. The memory
Identify the processes associated with Machine Learning/Al on FortiSIEM. (Choose two.)
A. phFortiInsightAI
B. phReportMaster
C. phRuleMaster
D. phAnomaly
E. phRuleWorker
Refer to the exhibit.
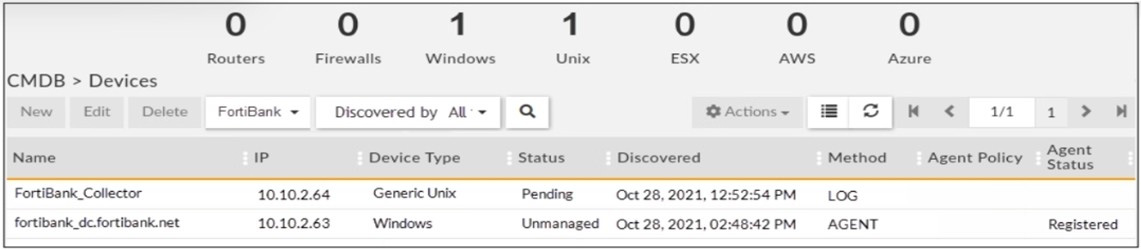
Is the Windows agent delivering event logs correctly?
A. The logs are buffered by the agent and will be sent once the status changes to managed.
B. The agent is registered and it is sending logs correctly.
C. The agent is not sending logs because it did not receive a monitoring template.
D. Because the agent is unmanaged. the logs are dropped silently by the supervisor.
Refer to the exhibit.
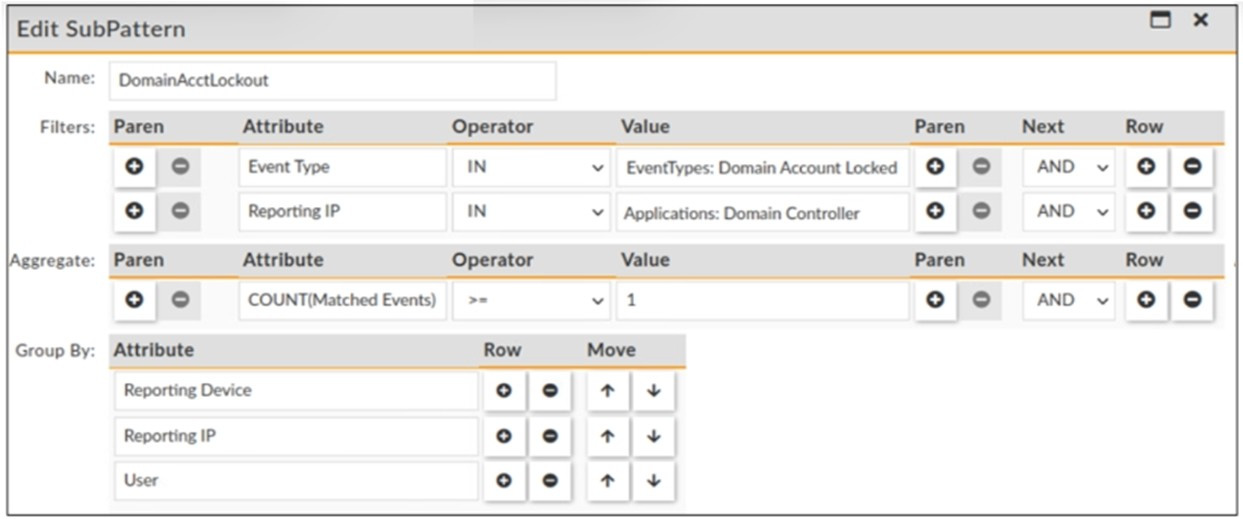
Which statement about the rule filters events shown in the exhibit is true?
A. The rule filters events with an event type that belong to the Domain Account Locked CMDB group or a reporting IP that belong to the Domain Controller applications group.
B. The rule filters events with an event type that belong to the Domain Account Locked CMDB group and a reporting |P that belong to the Domain Controller applications group.
C. The rule filters events with an event type that belong to the Domain Account Locked CMDB group and a user that belongs to the Domain Controller applications group.
D. The rule filters events with an event type that equals Domain Account Locked and a reporting IP that equals Domain Controller applications.
Refer to the exhibit.
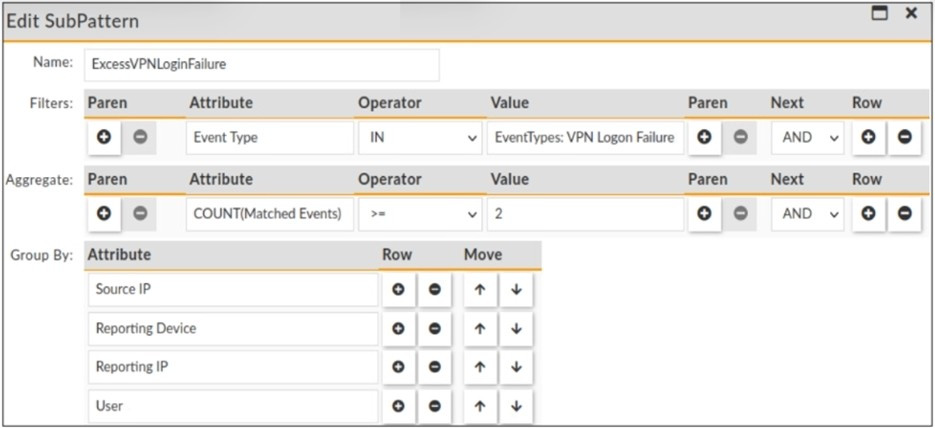
The rule evaluates multiple VPN logon failures within a ten-minute window. Consider the following VPN failure events received within a ten-minute window:
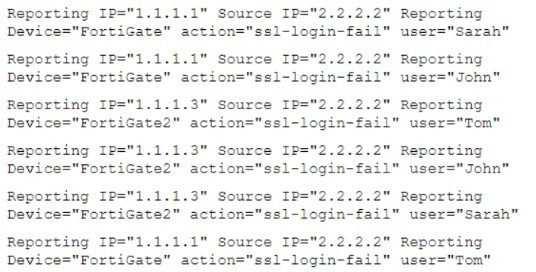
How many incidents are generated?
A. 1
B. 2
C. 0
D. 3
