NSE6_FML-6.2 Online Practice Questions and Answers
Refer to the exhibit.
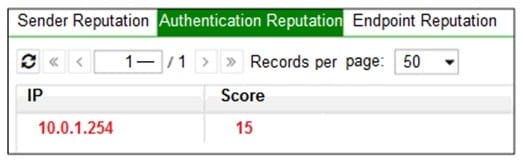
Which configuration change must you make to block an offending IP address temporarily?
A. Add the offending IP address to the system block list
B. Add the offending IP address to the user block list
C. Add the offending IP address to the domain block list
D. Change the authentication reputation setting status to Enable
Refer to the exhibit.
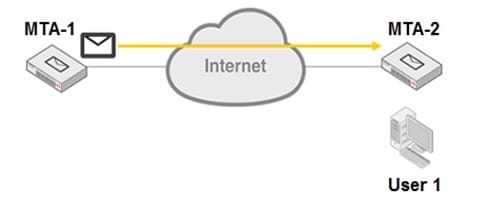
MTA-1 is delivering an email intended for User 1 to MTA-2.
Which two statements about protocol usage between the devices are true? (Choose two.)
A. User 1 will use IMAP to download the email message from MTA-2
B. MTA-2 will use IMAP to receive the email message from MTA-1
C. MTA-1 will use POP3 to deliver the email message to User 1 directly
D. MTA-1 will use SMTP to deliver the email message to MTA-2
An administrator sees that an excessive amount of storage space on a FortiMail device is being used up by quarantine accounts for invalid users. The FortiMail is operating in transparent mode.
Which two FortiMail features can the administrator configure to tackle this issue? (Choose two.)
A. Automatic removal of quarantine accounts
B. Recipient address verification
C. Bounce address tag verification
D. Sender address rate control
FortiMail is configured with the protected domain example.com.
Which two envelope addresses will require an access receive rule, to relay for unauthenticated senders? (Choose two.)
A. MAIL FROM: [email protected] RCPT TO: [email protected]
B. MAIL FROM: [email protected] RCPT TO: [email protected]
C. MAIL FROM: [email protected] RCPT TO: [email protected]
D. MAIL FROM: [email protected] RCPT TO: [email protected]
Refer to the exhibit.
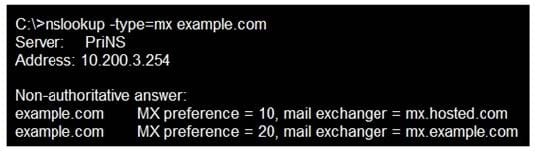
Which two statements about the MTAs of the domain example.com are true? (Choose two.)
A. The external MTAs will send email to mx.example.com only if mx.hosted.com is unreachable
B. The PriNS server should receive all email for the example.com domain
C. The primary MTA for the example.com domain is mx.hosted.com
D. The higher preference value is used to load balance more email to the mx.example.com MTA
Refer to the exhibit.
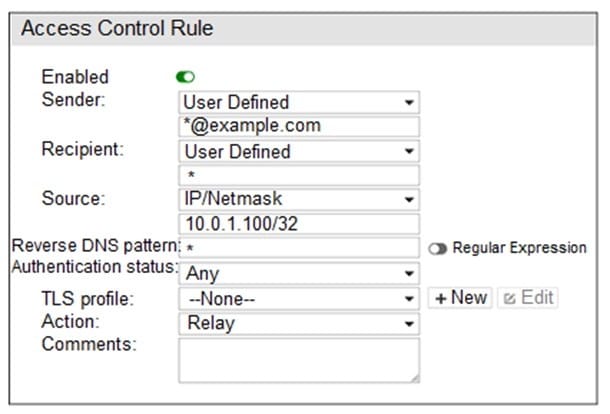
Which two statements about the access receive rule are true? (Choose two.)
A. Email matching this rule will be relayed
B. Email must originate from an example.com email address to match this rule
C. Senders must be authenticated to match this rule
D. Email from any host in the 10.0.1.0/24 subnet can match this rule
If you are using the built-in MTA to process email in transparent mode, which two statements about FortiMail behavior are true? (Choose two.)
A. MUAs need to be configured to connect to the built-in MTA to send email
B. If you disable the built-in MTA, FortiMail will use its transparent proxies to deliver email
C. FortiMail can queue undeliverable messages and generate DSNs
D. FortiMail ignores the destination set by the sender, and uses its own MX record lookup to deliver email
Refer to the exhibit.
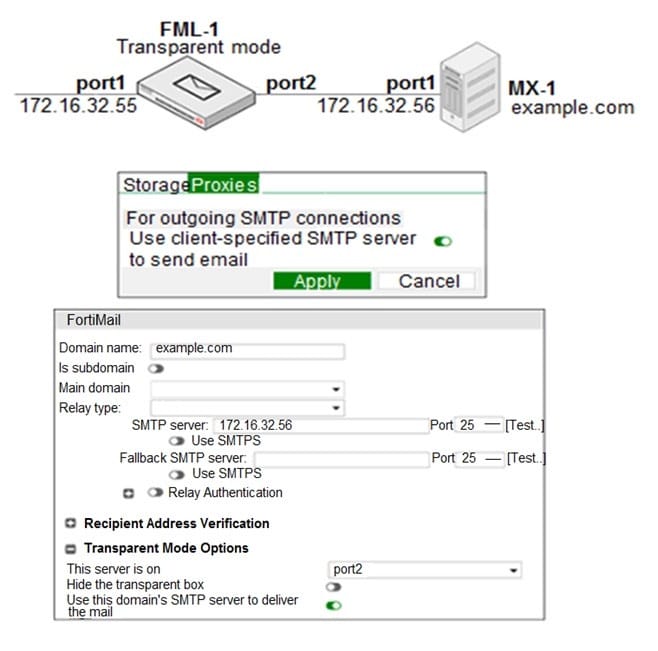
Which two statements about how the transparent mode FortiMail device routes email for the example.com domain are true? (Choose two.)
A. If incoming email messages are undeliverable, FML-1 can queue them to retry later
B. If outgoing email messages are undeliverable, FM-1 can queue them to retry later
C. FML-1 will use the built-in MTA for outgoing sessions
D. FML-1 will use the transparent proxy for incoming sessions
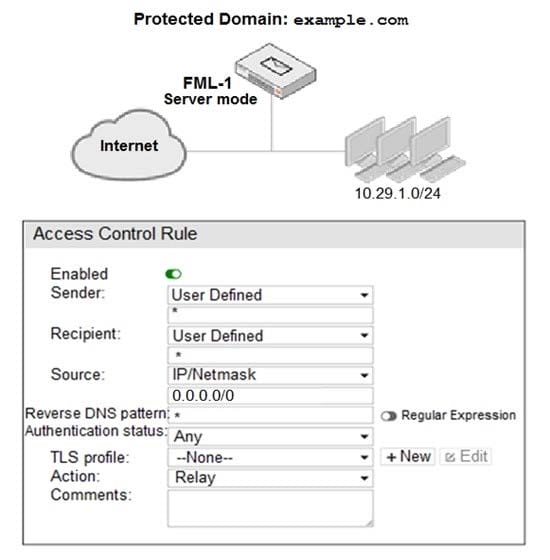
Refer to the exhibit.
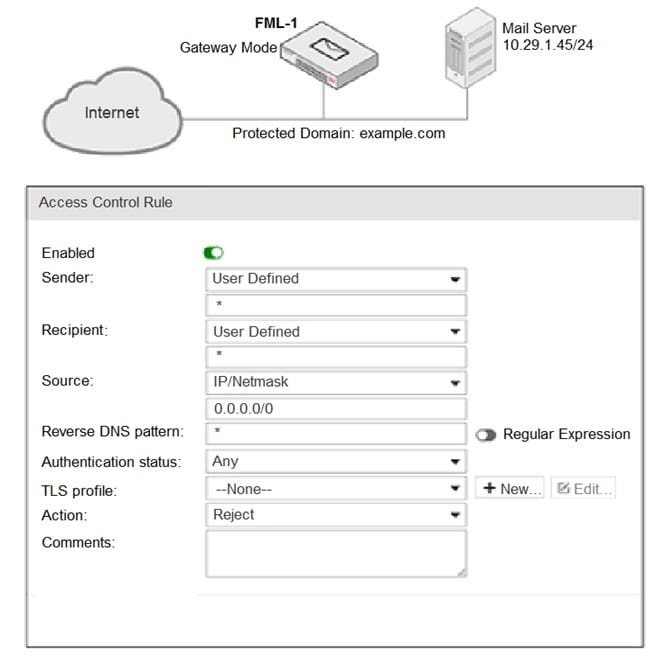
It is recommended that you configure which three access receive settings to allow outbound email from the example.com domain on FML-1? (Choose three.)
A. The Sender pattern should be set to *@example.com
B. The Action should be set to Relay
C. The Recipient pattern should be set to 10.29.1.45/24
D. The Enable check box should be cleared
E. The Sender IP/netmask should be set to 10.29.1.45/32
Refer to the exhibit.
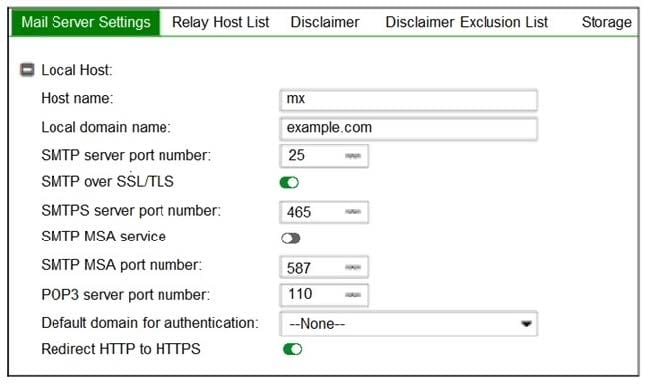
Which two statements about the mail server settings are true? (Choose two.)
A. FortiMail will support the STARTTLS extension
B. FortiMail will accept SMTPS connections
C. FortiMail will drop any inbound plaintext SMTP connection
D. FortiMail will enforce SMTPS on all outbound sessions
A FortiMail administrator is investigating a sudden increase in DSNs being delivered to the protected domain for undeliverable email messages. After searching the logs, the administrator identifies that the DSNs were not generated as a result of any outbound email sent from the protected domain.
Which FortiMail antispam technique can the administrator use to prevent this scenario?
A. Spam outbreak protection
B. Bounce address tag validation
C. Spoofed header detection
D. FortiGuard IP Reputation
Refer to the exhibit.

Which two message types will trigger this DLP scan rule? (Choose two.)
A. An email message with a subject that contains the term "credit card" will trigger this scan rule
B. An email that contains credit card numbers in the body, attachment, and subject will trigger this scan rule
C. An email message that contains credit card numbers in the body will trigger this scan rule
D. An email sent from [email protected] will trigger this scan rule, even without matching any conditions
Refer to the exhibit.
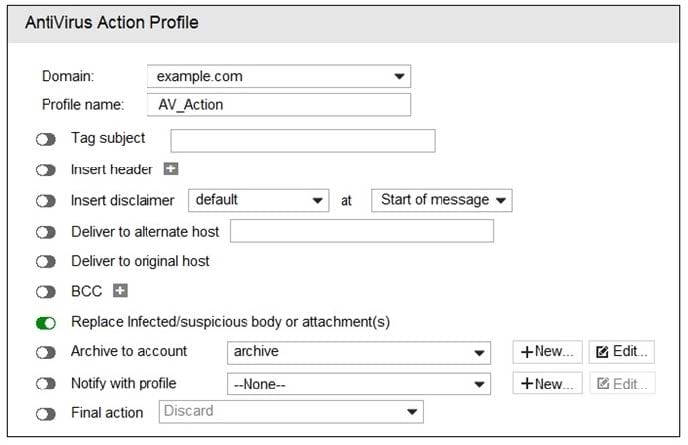
What are two expected outcomes if FortiMail applies this antivirus action profile to an email? (Choose two.)
A. Virus content will be removed from the email
B. A replacement message will be added to the email
C. The sanitized email will be sent to the recipient's personal quarantine
D. The administrator will be notified of the virus detection
An organization has different groups of users with different needs in email functionality, such as address book access, mobile device access, email retention periods, and disk quotas.
Which FortiMail feature specific to server mode can be used to accomplish this?
A. Resource profiles
B. Domain-level service settings
C. Access profiles
D. Address book management options
Refer to the exhibit.
An administrator must enforce authentication on FML-1 for all outbound email from the example.com domain.
Which two settings should be used to configure the access receive rule? (Choose two.)
A. The Recipient pattern should be set to *@example.com
B. The Authentication status should be set to Authenticated
C. The Sender IP/netmask should be set to 10.29.1.0/24
D. The Action should be set to Reject
