NSE6_FML-6.0 Online Practice Questions and Answers
Examine the FortiMail recipient-based policy shown in the exhibit; then answer the question below.
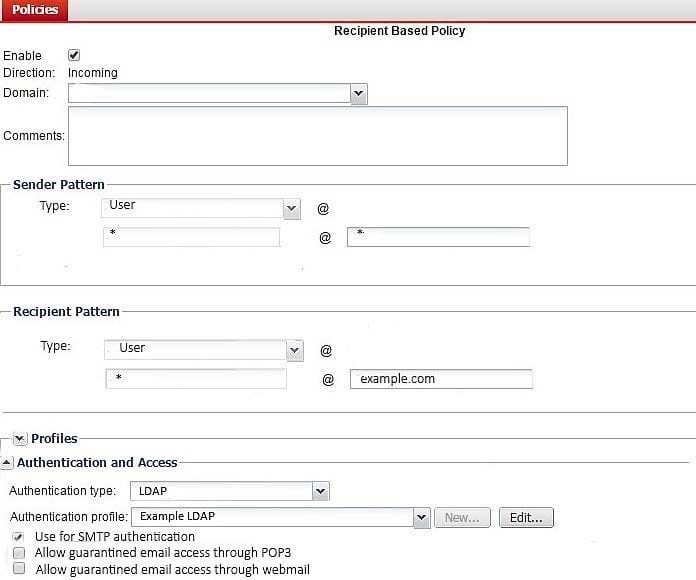
After creating the policy, an administrator discovered that clients are able to send unauthenticated email using SMTP. What must be done to ensure clients cannot send unauthenticated email?
A. Configure a matching IP policy with SMTP authentication and exclusive flag enabled
B. Move the recipient policy to the top of the list
C. Configure an access receive rule to verify authentication status
D. Configure an access delivery rule to enforce authentication
Examine the nslookup output shown in the exhibit; then answer the question below.

Identify which of the following statements is true regarding the example.com domain's MTAs. (Choose two.)
A. External MTAs will send email to mx.example.com only if mx.hosted.com is unreachable
B. The primary MTA for the example.com domain is mx.hosted.com
C. The PriNS server should receive all email for the example.com domain
D. The higher preference value is used to load balance more email to the mx.example.com MTA
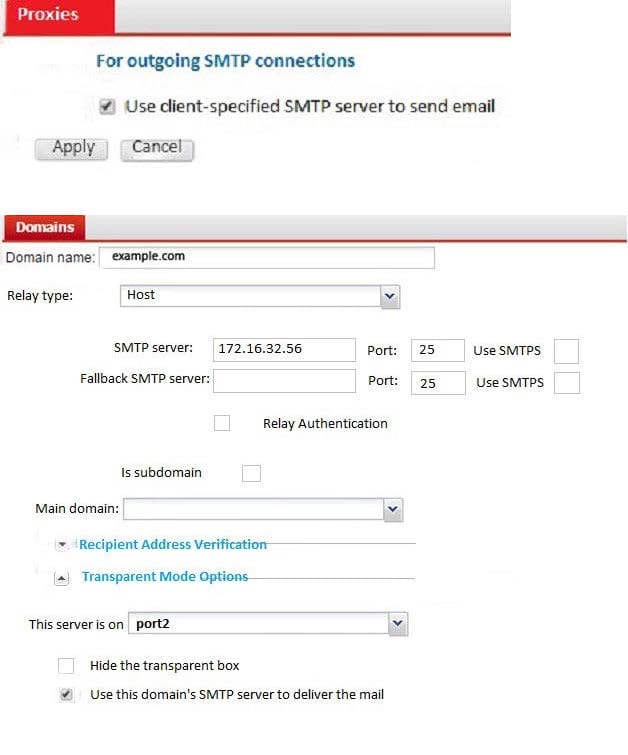
Examine the FortMail mail server settings shown in the exhibit; then answer the question below.
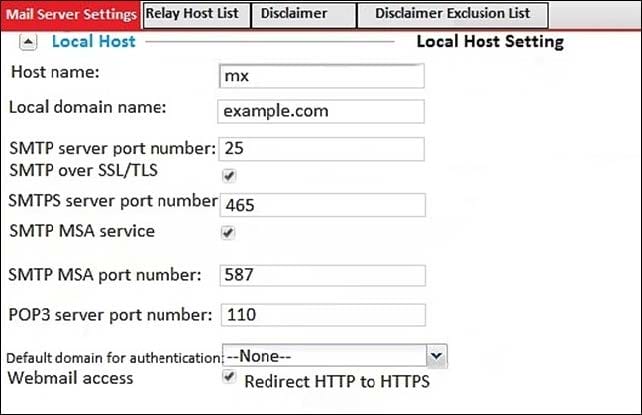
Which of the following statements are true? (Choose two.)
A. mx.example.com will enforce SMTPS on all outbound sessions
B. mx.example.com will display STARTTLS as one of the supported commands in SMTP sessions
C. mx.example.com will accept SMTPS connections
D. mx.example.com will drop any inbound plaintext SMTP connection
Which of the following CLI commands, if executed, will erase all data on the log disk partition? (Choose two.)
A. execute formatmaildisk
B. execute formatmaildisk_backup
C. execute formatlogdisk
D. execute partitionlogdisk 40
Examine the FortiMail IBE users shown in the exhibit; then answer the question below Which one of the following statements describes the Pre-registered status of the IBE user [email protected]?
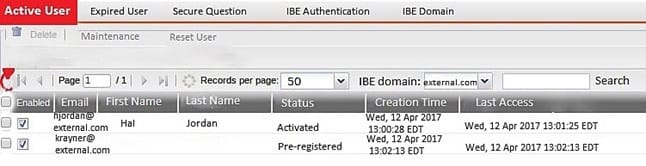
A. The user was registered by an administrator in anticipation of IBE participation
B. The user has completed the IBE registration process but has not yet accessed their IBE email
C. The user has received an IBE notification email, but has not accessed the HTTPS URL or attachment yet
D. The user account has been de-activated, and the user must register again the next time they receive an IBE email
Examine the access receive rule shown in the exhibit; then answer the question below.
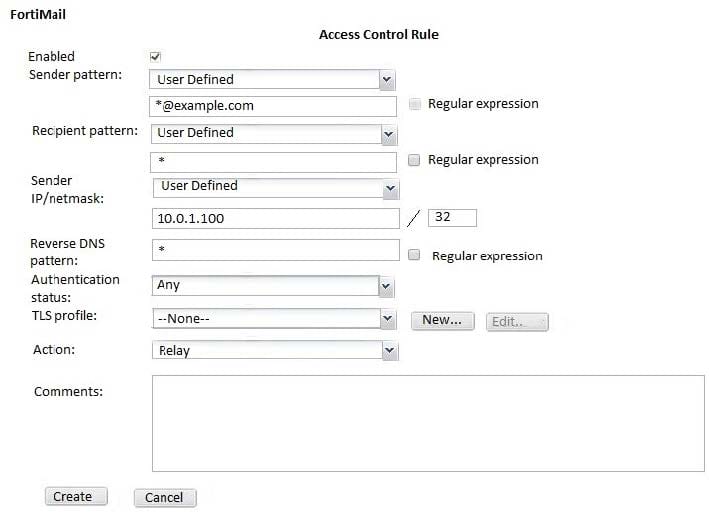
Which of the following statements are true? (Choose two.)
A. Email from any host in the 10.0.1.0/24 subnet can match this rule
B. Senders must be authenticated to match this rule
C. Email matching this rule will be relayed
D. Email must originate from an example.com email address to match this rule
Which of the following statements are true regarding FortiMail's behavior when using the built-in MTA to process email in transparent mode? (Choose two.)
A. FortiMail can queue undeliverable messages and generate DSNs
B. If you disable the built-in MTA, FortiMail will use its transparent proxies to deliver email
C. FortiMail ignores the destination set by the sender and uses its own MX record lookup to deliver email
D. MUAs need to be configured to connect to the built-in MTA to send email
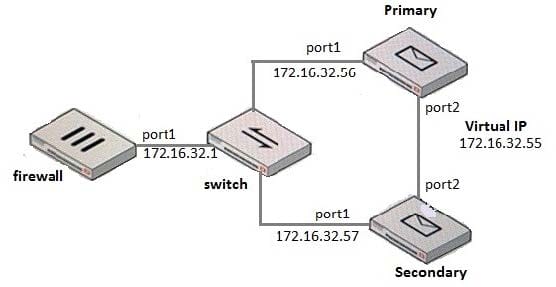
What IP address should the DNS MX record for this deployment resolve to?
A. 172.16.32.1
B. 172.16.32.57
C. 172.16.32.55
D. 172.16.32.56
Examine the FortiMail user webmail interface shown in the exhibit; then answer the question below.
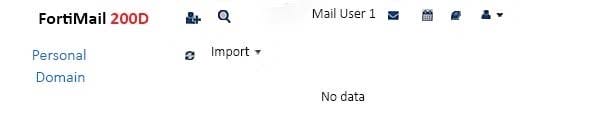
Which one of the following statements is true regarding this server mode FortiMail's configuration?
A. The protected domain-level service settings have been modified to allow access to the domain address book
B. This user's account has a customized access profile applied that allows access to the personal address book
C. The administrator has not made any changes to the default address book access privileges
D. The administrator has configured an inbound recipient policy with a customized resource profile
Examine the exhibit; then answer the question below.
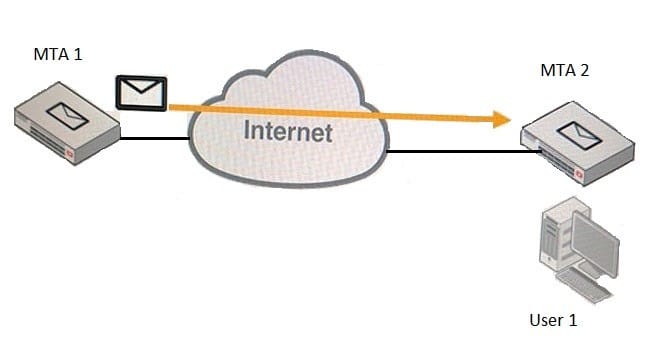
MTA 1 is delivering an email intended for User 1 to MTA 2. Which of the following statements about protocol usage between the devices are true? (Choose two.)
A. MTA 2 will use IMAP to receive the email message from MTA 1
B. MTA 1 will use SMTP to deliver the email message to MTA 2
C. User 1 will use IMAP to download the email message from MTA 2
D. MTA 1 will use POP3 to deliver the email message to User 1 directly
Examine the FortiMail DLP scan rule shown in the exhibit; then answer the question below.
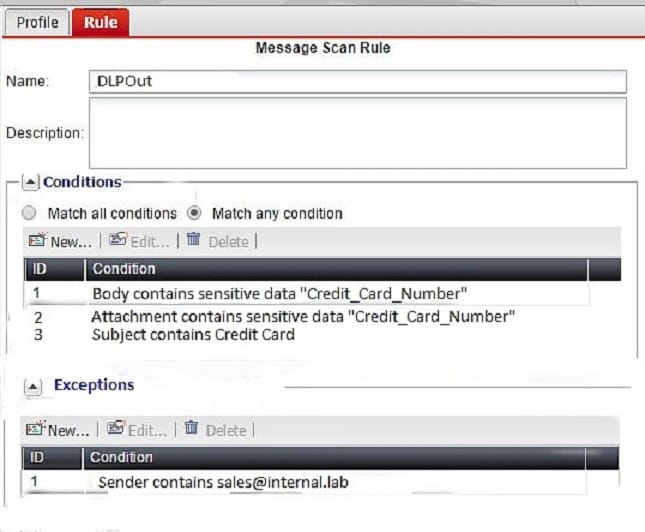
Which of the following statements is true regarding this configuration? (Choose two.)
A. An email message containing the words "Credit Card" in the subject will trigger this scan rule
B. If an email is sent from [email protected] the action will be applied without matching any conditions
C. An email message containing credit card numbers in the body will trigger this scan rule
D. An email must contain credit card numbers in the body, attachment, and subject to trigger this scan rule
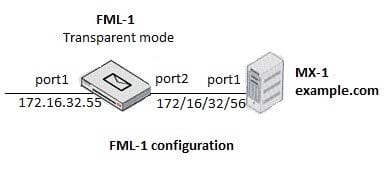
Which of the following statements are true regarding the transparent mode FortiMail's email routing for the example.com domain? (Choose two.)
A. FML-1 will use the built-in MTA for outgoing sessions
B. FML-1 will use the transparent proxy for incoming sessions
C. If incoming email are undeliverable, FML-1 can queue them to retry again later
D. If outgoing email messages are undeliverable, FML-1 can queue them to retry later
A FortiMail is configured with the protected domain "example.com". For this FortiMail, which of the following envelope addresses are considered incoming? (Choose two.)
A. MAIL FROM: [email protected] RCPT TO: [email protected]
B. MAIL FROM: [email protected] PCPT TO: [email protected]
C. MAIL FROM: [email protected] RCPT TO: [email protected]
D. MAIL FROM: [email protected] RCPT TO: [email protected]
Examine the FortiMail topology and IP-based policy shown in the exhibit; then answer the question below.
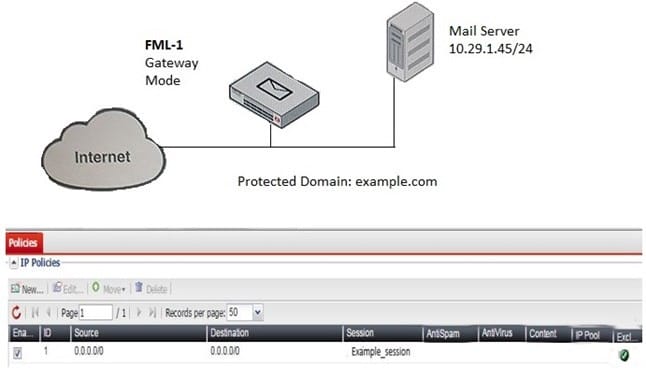
An administrator has enabled the sender reputation feature in the Example_Session profile on FML-1. After a few hours, the deferred queue on the Mail Server started filing up with undeliverable email. What changes should the administrator make to fix this issue? (Choose two.)
A. Clear the sender reputation database using the CLI
B. Create an outbound recipient policy to bypass outbound email from session profile inspections
C. Disable the exclusive flag in IP policy ID 1
D. Apply a session profile with sender reputation disabled on a separate IP policy for outbound sessions
An organization has different groups of users with different needs in email functionality, such as address book access, mobile device access, email retention periods, and disk quotas. Which FortiMail feature specific to server mode can be used to accomplish this?
A. Resource profiles
B. Address book management options
C. Access profiles
D. Domain-level service settings
