NSE5_FCT-6.2 Online Practice Questions and Answers
Refer to the exhibit.
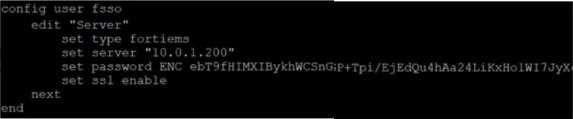
Based on the CLI output from FortiGate. which statement is true?
A. FortiGate is configured to pull user groups from FortiClient EMS
B. FortiGate is configured with local user group
C. FortiGate is configured to pull user groups from FortiAuthenticator
D. FortiGate is configured to pull user groups from AD Server.
Refer to the exhibit.
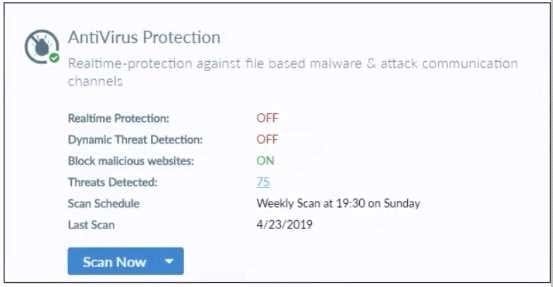
Based on the settings shown in the exhibit what action will FortiClient take when it detects that a user is trying to download an infected file?
A. Blocks the infected files as it is downloading
B. Quarantines the infected files and logs all access attempts
C. Sends the infected file to FortiGuard for analysis
D. Allows the infected file to download without scan
Refer to the exhibit.
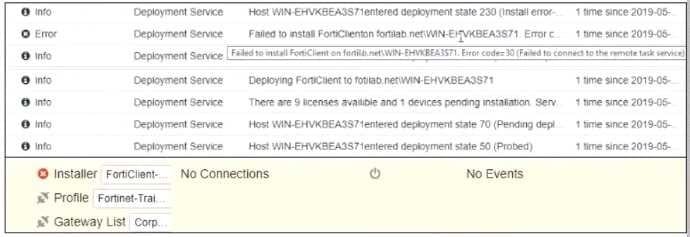
Based on the logs shown in the exhibit, why did FortiClient EMS fail to install FortiClient on the endpoint?
A. Windows firewall is not running
B. Windows installer service is not running
C. Remote registry service is not running
D. Task scheduler service is not running
An administrator deploys a FortiClient installation through the Microsoft AD group policy After installation is
complete all the custom configuration is missing.
What could have caused this problem?
A. The FortiClient exe file is included in the distribution package
B. The FortiClient MST file is missing from the distribution package
C. FortiClient does not have permission to access the distribution package.
D. The FortiClient package is not assigned to the group
Which statement about FortiClient comprehensive endpoint protection is true?
A. It helps to safeguard systems from email spam
B. It helps to safeguard systems from data loss.
C. It helps to safeguard systems from DDoS.
D. lt helps to safeguard systems from advanced security threats, such as malware.
Which two VPN types can a FortiClient endpoint user inmate from the Windows command prompt? (Choose two)
A. L2TP
B. PPTP
C. IPSec
D. SSL VPN
A FortiClient EMS administrator has enabled compliance rule for the sales department Which Fortmet device will enforce compliance with dynamic access control?
A. FortiClient EMS
B. FortiAnalyzer
C. FortiGate
D. FortiClient
Refer to the exhibit.
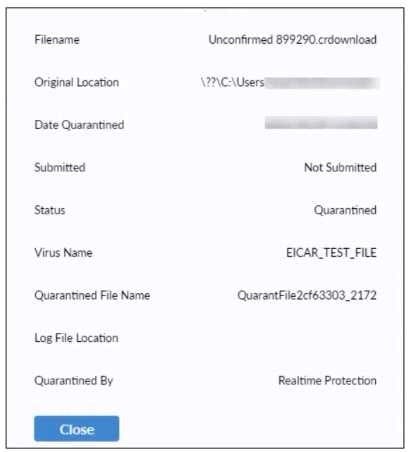
Based on the FortiClient log details shown in the exhibit, which two statements are true? (Choose two)
A. The file status is Quarantined
B. The file location is \??\D: \Users
C. The filename IS Unconfirmed 399290-crdownload.
D. The filename is sent to FortiSandbox for further inspection.
What does FortiClient do as a fabric agent? (Choose two )
A. Provides application inventory
B. Provides IOC verdicts
C. Automates Responses
D. Creates dynamic policies
Refer to the exhibit.
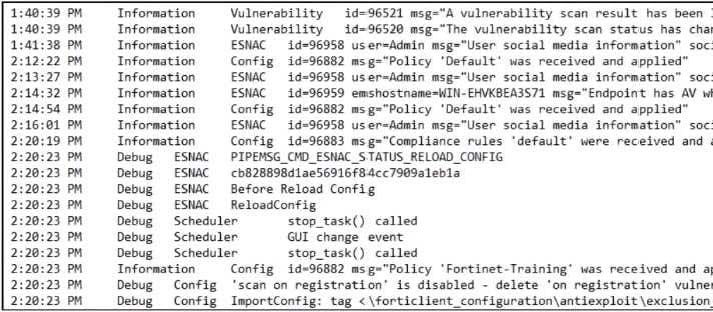
Based on the FortiClient logs shown in the exhibit which endpoint profile policy is currently applied to the FortiClient endpoint from the EMS server?
A. WIK-EKVK3EA3S71
B. Fortinet-Training
C. Default
D. Default configuration policy
An administrator is required to maintain a software inventory on the endpoints. without showing the feature on the FortiClient dashboard What must the administrator do to achieve this requirement?
A. The administrator must use default endpoint profile
B. The administrator must not select the vulnerability scan feature in the deployment package.
C. The administrator must select the vulnerability scan feature in the deployment package, but disable the feature on the endpoint profile
D. The administrator must click the hide icon on the vulnerability scan tab
Refer to the exhibit.
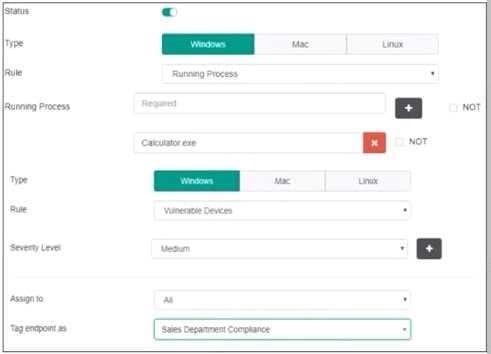
Based on the settings shown in the exhibit, which two actions must the administrator take to make the endpoint compliant? (Choose two)
A. Integrate FortiSandbox for infected file analysis.
B. Enable the webfilter profile
C. Patch applications that have vulnerability rated as high or above.
D. Run Calculator application on the endpoint.
Refer to the exhibit.
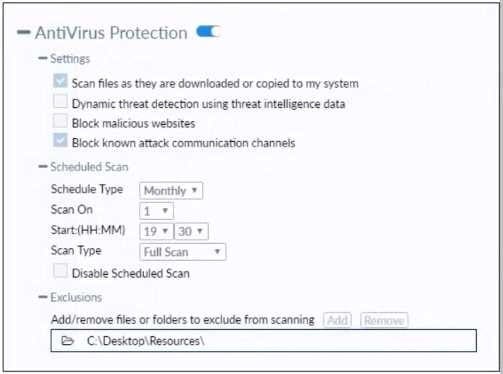
Based on the settings shown in the exhibit which statement about FortiClient behavior is true?
A. FortiClient quarantines infected files and reviews later, after scanning them.
B. FortiClient blocks and deletes infected files after scanning them.
C. FortiClient scans infected files when the user copies files to the Resources folder
D. FortiClient copies infected files to the Resources folder without scanning them.
An administrator installs FortiClient on Windows Server. What is the default behavior of real-time protection control?
A. Real-time protection must update AV signature database
B. Real-time protection sends malicious files to FortiSandbox when the file is not detected locally
C. Real-time protection is disabled
D. Real-time protection must update the signature database from FortiSandbox
Which network component sends a notification after identifying a connected endpoint in the quarantine automation process?
A. FortiGate
B. FortiClient
C. FortiClient EMS
D. FortiAnalyzer
