NSE4_FGT-6.4 Online Practice Questions and Answers
Examine this PAC file configuration.

Which of the following statements are true? (Choose two.)
A. Browsers can be configured to retrieve this PAC file from the FortiGate.
B. Any web request to the 172.25.120.0/24 subnet is allowed to bypass the proxy.
C. All requests not made to Fortinet.com or the 172.25.120.0/24 subnet, have to go through altproxy.corp.com: 8060.
D. Any web request fortinet.com is allowed to bypass the proxy.
What is the limitation of using a URL list and application control on the same firewall policy, in NGFW policy-based mode?
A. It limits the scope of application control to the browser-based technology category only.
B. It limits the scope of application control to scan application traffic based on application category only.
C. It limits the scope of application control to scan application traffic using parent signatures only
D. It limits the scope of application control to scan application traffic on DNS protocol only.
Which two statements are correct regarding FortiGate FSSO agentless polling mode? (Choose two.)
A. FortiGate points the collector agent to use a remote LDAP server.
B. FortiGate uses the AD server as the collector agent.
C. FortiGate uses the SMB protocol to read the event viewer logs from the DCs.
D. FortiGate queries AD by using the LDAP to retrieve user group information.
Which type of logs on FortiGate record information about traffic directly to and from the FortiGate management IP addresses?
A. System event logs
B. Forward traffic logs
C. Local traffic logs
D. Security logs
How do you format the FortiGate flash disk?
A. Load a debug FortiOS image.
B. Load the hardware test (HQIP) image.
C. Execute the CLI command execute formatlogdisk.
D. Select the format boot device option from the BIOS menu.
Which three statements about security associations (SA) in IPsec are correct? (Choose three.)
A. Phase 2 SAs are used for encrypting and decrypting the data exchanged through the tunnel.
B. An SA never expires.
C. A phase 1 SA is bidirectional, while a phase 2 SA is directional.
D. Phase 2 SA expiration can be time-based, volume-based, or both.
E. Both the phase 1 SA and phase 2 SA are bidirectional.
Which statement about the IP authentication header (AH) used by IPsec is true?
A. AH does not provide any data integrity or encryption.
B. AH does not support perfect forward secrecy.
C. AH provides data integrity bur no encryption.
D. AH provides strong data integrity but weak encryption.
Examine the network diagram shown in the exhibit, then answer the following question:
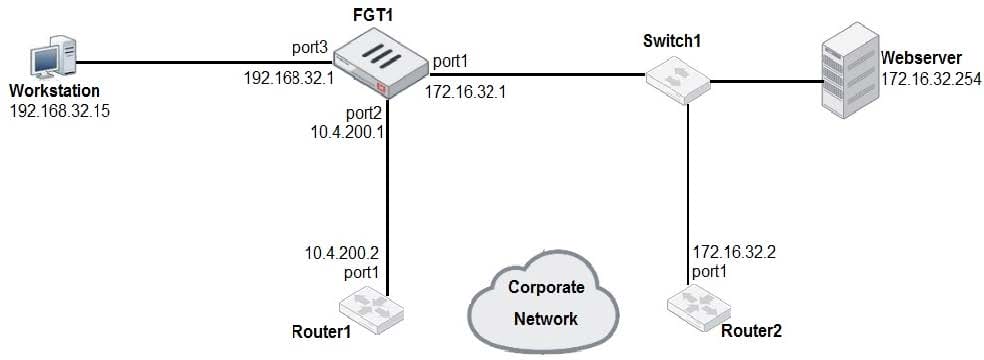
Which one of the following routes is the best candidate route for FGT1 to route traffic from the Workstation to the Web server?
A. 172.16.0.0/16 [50/0] via 10.4.200.2, port2 [5/0]
B. 0.0.0.0/0 [20/0] via 10.4.200.2, port2
C. 10.4.200.0/30 is directly connected, port2
D. 172.16.32.0/24 is directly connected, port1
