NCM-MCI Online Practice Questions and Answers
An administrator has a VM that consumes large amounts of storage and has the following characteristics:
1.
Create large / sequential writes
2.
Data must be kept for years
3.
Data is normally only accessed at the end of the year to run report The administrator decides to use Erasure Coding to save space. Which feature should the administrator utilize to save space for this VM?
A. Inline Compression
B. Flash Mode
C. Cache Dedup
D. Post-Process Compression
An administrator needs to make sure an RF3 cluster can survive a failure of two complete racks without negatively affecting performance. The current cluster configuration consists of the following:
1.
30 All Flash Nodes: distributed 10 nodes per rack across three 42U racks
2.
Each node is configured with 20TB usable storage all flash (Cluster Total 600TB Usable)
3.
Current cluster utilization is 500TB storage
4.
Storage containers have Erasure Coding enabled
Which configuration changes should be made to make sure the cluster meets the requirements?
A. Expand the cluster to 50 nodes distributed evenly across 5 racks
B. Expand the cluster to 48 nodes distributed evenly across 6 racks
C. Expand the cluster to 60 nodes distributed evenly across 6 racks
D. Expand the cluster to 40 nodes distributed evenly across 5 racks
An administrator needs to maximize storage potential in a six-node cluster. The container is configured with the following:
1.
Post-process compression
2.
Capacity deduplication
What should the administrator configure to increase space savings?
A. Erasure coding
B. Inline compression
C. Reserve capacity
D. Cache dedupe
An administrator learns that some security settings in a cluster have been changed. The environment is out of compliance with required policies. Which function should be used to revert any settings that have changed from the defaults and prevent further violations?
A. Cluster Lockdown with strong password enforcement
B. Advanced Intrusion Detection Environment (AIDE)
C. Security Configuration Management Automation (SCMA)
D. Defense Information Systems Agency STIG enforcement
Refer to the exhibit.
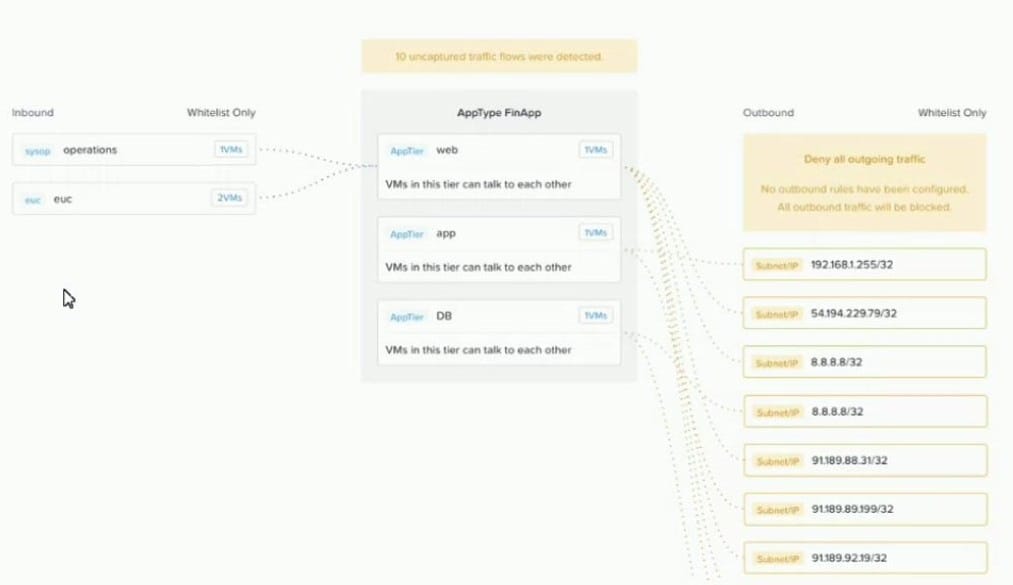
An administrator creates a security policy that isolates their financial application from accessing the Internet When viewing the policy in Prism Central, several connections from the application are outbound to the Internet. What is causing this issue with the policy?
A. The 0.0.0.0 address was not specified in the outbound rule.
B. The blocked connections are illustrated for information only.
C. The Activate box was not checked in the rule, so it is not enforcing.
D. The policy has been left in monitor mode instead of enforcing mode.
A Nutanix cluster is deployed with the following configuration:
1.
Three four-node blocks (A, B, and C)
2.
All Flash Redundancy Factor 2
What is the effect of simultaneous disk failures on two nodes located in block A?
A. VMs are migrated off of the nodes with disk failures.
B. Each node with a failed disk is marked as degraded.
C. VM read and write operations continue normally.
D. VMs on the nodes with failed disks are unable to write data
An administrator configure Active Directory (AD) authentication for their Nutanix environment. When login in using an AD user account, the login process takes more than one minute to complete. No delay occurs when logging a local account. What should the administrator confirm to resolve this issue?
A. The user search base for the group is configured correctly
B. The domain controller being used is configured as a global catalog server.
C. Active directory lookups are configured to use Non-Recursive mode.
D. The service Account Username is correct for the domain.
An administrator needs to replace an aging SAN and move to a hyper-converged infrastructure. The existing environment consists of the following hosts that are connected to the SAN:
1.
5xAIX hosts
2.
3x Hyper-V hosts
3.
9xESXi hosts
4.
2x physical SQL Clusters (Windows Server 2012R2 hosts)
After deploying a Nutanix AHV cluster, which two actions should the administrator take to meet the requirements? (Choose two.)
A. Deploy Volumes to support the AIX and SQL workloads.
B. Migrate the ESXI workloads to AHV using Move.
C. Deploy Files to support the AIX hosts.
D. Migrate the ESXi and Hyper-V workloads using Move.
A customer has a primary datacenter with 12 Nutanix blocks distributed across three racks. The customer wants to achieve the most resiliency possible. They also have a datacenter in a branch office that is 400 kilometers away from the primary datacenter.
Which two solutions should be used? (Choose two.)
A. Time Stream to a remote site
B. Async DR to a remote site
C. Rack awareness
D. Block awareness
An administrator wants to utilize Network Visualization to monitor the physical and logical network on the Nutanix cluster. The first-hop switch has LLDP enabled. The network switch information is still not being displayed. What is causing this problem?
A. The ISL between switches is not configured.
B. SNMP is not configured properly.
C. br0 and br1 are not defined.
D. The cluster is using RDMA-enabled NICs.
An administrator has a custom backup application that requires a 2TB disk and runs in Windows. Throughput is considerably lower than expected. The application was installed on a VM with the following configuration:
1.
Four vCPUs with one core/vCPU
2.
4GB of Memory
3.
One 50GB vDisk for the Windows installation
4.
One 2TB vDisk for the application
What is the recommended configuration change to improve throughput?
A. Increase the number of cores per vCPU
B. Increase the vCPUs assigned to the VM
C. Span the 2TB disk across four vDisks
D. Add 4GB of memory to the VM
Refer to the exhibit.
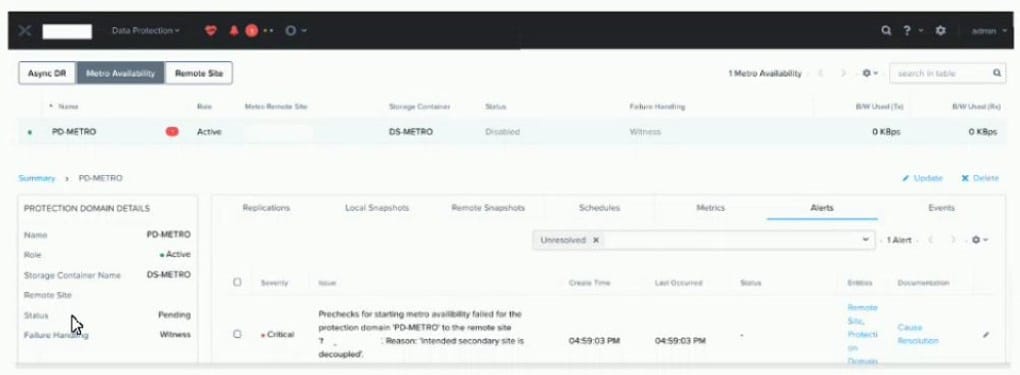
An administrator notices a critical alert on the Metro Availability Protection Domain What is causing this alert?
A. Metro Availability Protection domain is active on the remote site.
B. VMware Site Recovery Manager is handling a failover event
C. Metro Availability did not fail over and caused an outage.
D. vSphere moved VMs to the remote container, and the VMs must be moved back.
A VDI environment based on AHV Cluster is not performing well. The current environment is using only one bridge (Bridge0). The administrator needs to verify if nodes are using all network cards associated to Bridge0. Which two menus should be used to check the current configuration? (Choose two.)
A. Network Configuration item in Settings menu
B. Host view in Network menu
C. Host NICs tab in Hardware menu
D. I/O Metrics tab in VM menu
An administrator receives reports about a Nutanix environment. The investigation finds the following;
1.
VMs are experiencing very high latency
2.
Each node is equipped with a single SSD, utilized at 95%
3.
Each node is equipped with three HDDs, utilized at 40% Why are the guest VMs experiencing high latency?
A. CVMs are overwhelmed by disk balancing operations.
B. All VM write operations are going to HDD.
C. All VM read operations are coming from HDD.
D. VMs are unable to perform write operations.
A customer has Metro Availability configured in Automatic Resume Mode between Site A and Site B What happens to VMs if Primary Site A has full network failure?
A. Automatic protection domain promotion in Site B. VMs automatically restart in Site B
B. VMs continue to run on Site A following an automatic disable of protection domains.
C. An administrator must unwitness in Site B and promote protection domains in Site B for VMs to restart
D. An administrator must promote protection domains in Site B for VMs to restart.
