HPE6-A15 Online Practice Questions and Answers
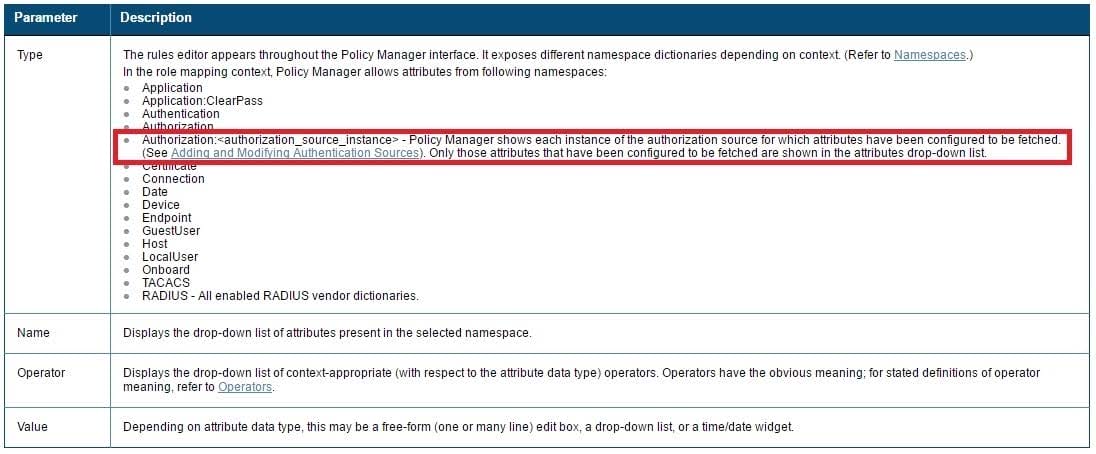
Which components can use Active Directory authorization attributes for the decision-making process? (Select two.)
A. Profiling policy
B. Certificate validation policy
C. Role Mapping policy
D. Enforcement policy
E. Posture policy
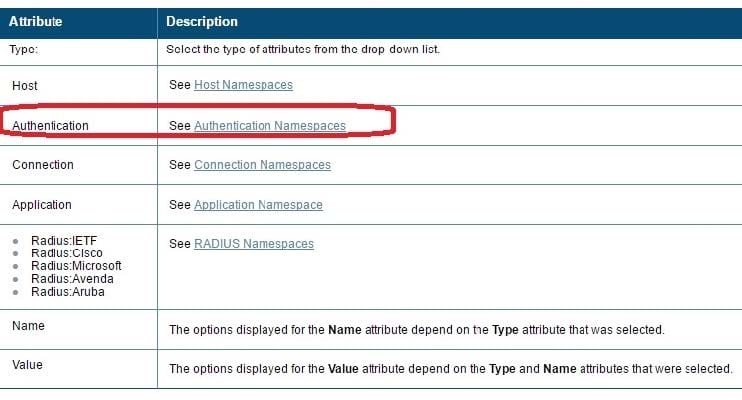
Refer to the exhibit.
Based on the Authentication sources configuration shown, which statement accurately describes the outcome if the user is not found?
A. If the user is not found in the remotelab AD but is present in the local user repository, a reject message is sent back to the NAD.
B. If the user is not found in the local user repository but is present in the remotelab AD, a reject message is sent back to the NAD.
C. If the user is not found in the local user repository a reject message is sent back to the NAD.
D. If the user is not found in the local user repository and remotelab AD, a reject message is sent back to the NAD.
E. If the user is not found in the local user repository a timeout message is sent back to the NAD.
Which CLI command is used to upgrade the image of a ClearPass server?
A. Image update
B. System upgrade
C. Upgrade image
D. Reboot
E. Upgrade software
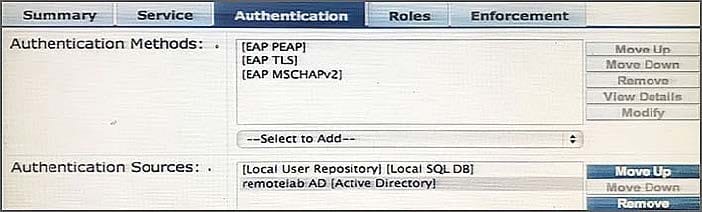
Refer to the exhibit.
Based on the network topology diagram shown, how many clusters are needed for this deployment?
A. 1
B. 2
C. 3
D. 4
E. 8
Refer to the exhibit.
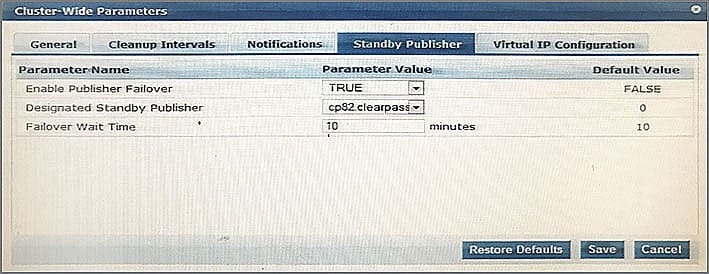
Which statements accurately describe the cp82 ClearPass node? (Select two.)
A. It becomes the Publisher when the primary Publisher fails.
B. It operated as a Publisher in the same cluster as the primary Publisher when the primary is active.
C. It operated as a Publisher in a separate cluster when the Publisher is active.
D. It operates as a Subscriber when the Publisher is active.
E. It stays as a Subscriber when the Publisher fails.
ClearPass and a wired switch are configured for 802.1x authentication with RADIUS CoA (RFC 3576) on UDP port 3799. This port has been blocked by a firewall between the wired switch and ClearPass. What will be the outcome of this state?
A. RADIUS Authentications will fail because the wired switch will not be able to reach the ClearPass server.
B. During RADIUS Authentication, certificate exchange between the wired switch and ClearPass will fail.
C. RADIUS Authentications will timeout because the wired switch will not be able to reach the ClearPass server.
D. RADIUS Authentication will succeed, but Post-Authentication Disconnect-Requests from ClearPass to the wired switch will not be delivered.
E. RADIUS Authentication will succeed, but RADIUS Access-Accept messages from ClearPass to the wired switch for Change of Role will not be delivered.
A customer would like to deploy ClearPass with these requirements: every day, 100 employees need to authenticate with their corporate laptops using EAP-TLS every Friday, a meeting with business partners takes place and an additional 50 devices need to authenticate using Web Login Guest Authentication
What should the customer do regarding licenses? (Select two.)
A. When counting policy manager licenses, include the additional 50 business partner devices.
B. When counting policy manager licenses, exclude the additional 50 business partner devices.
C. Purchase Onboard licenses.
D. Purchase guest licenses.
E. Purchase Onguard licenses.
What is the certificate format PKCS #7, or .p7b, used for?
A. Certificate Signing Request
B. Binary encoded X.509 certificate
C. Binary encoded X.509 certificate with public key
D. Certificate with an encrypted private key
E. Certificate chain
Refer to the exhibit.
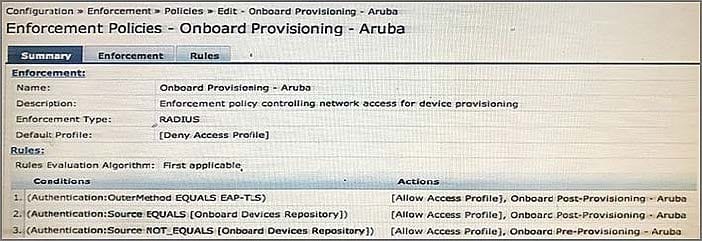
An employee connects a corporate laptop to the network and authenticates for the first time using EAP-TLS. Based on the Enforcement Policy configuration shown, which Enforcement Profile will be sent?
A. Onboard Post-Provisioning ?Aruba
B. Onboard Pre-Provisioning ?Aruba
C. Deny Access Profile
D. Onboard Device Repository
Refer to the exhibit.
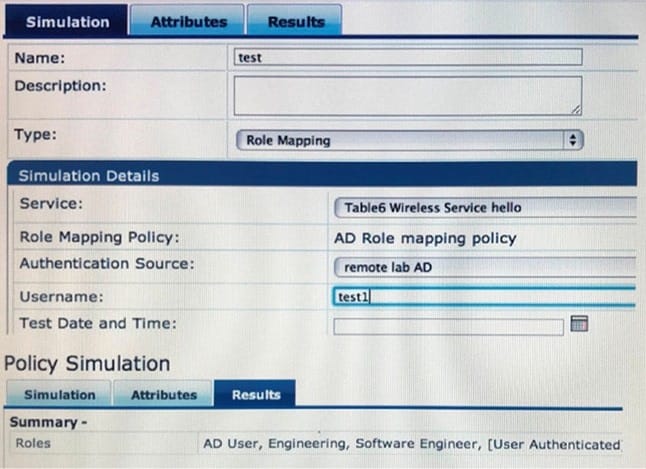
Which statement accurately reflects the status of the Policy Simulation test figure shown?
A. The test verifies that a client with username test1 can authenticate using EAP-PEAP.
B. Role mapping simulation verifies if the remote lab AD has the ClearPass server certificate.
C. Role mapping simulation verifies that the client certificate is valid during EAP-TLS authentication.
D. The simulation test result shows the firewall roles assigned to the client by the Aruba Controller.
E. The roles assigned in the results tab are based on rules matched in the AD Role Mapping Policy.
Refer to the exhibit.
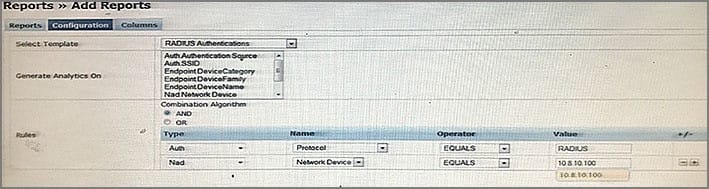
Which types of records will the report shown display?
A. all RADIUS authentications from the 10.8.10.100 NAD to ClearPass
B. all failed RADIUS authentications through ClearPass
C. only Windows devices that have authenticated through the 10.8.10.100 NAD
D. all successful RADIUS authentications through ClearPass
E. all successful RADIUS authentications from the 10.8.10.100 NAD to ClearPass
A guest self-registered through a Publisher's Register page.
Which statement accurately describes how the guest's account will be stored?
A. It will be stored in the Publisher's guest user repository and the Subscriber's Onboard user repository.
B. It will be stored in the Publisher's local user repository and the Subscriber's guest user repository.
C. It will be stored in the Publisher's guest user repository permanently, but only for 14 days in the Subscriber's guest user repository,
D. It will be stored in both the Publisher's guest user repository and the Subscriber's guest user repository.
E. It will be stored in the Publisher's guest user repository, but not the Subscriber's.
The "Alerts" tab in an access tracker entry shows the error message: "Access denied by policy."
What is a possible cause of authentication failure?
A. Failure to find an appropriate service to process the authentication request
B. Configuration of the Enforcement Policy
C. An error in the role mapping policy
D. Implementation of a firewall policy on ClearPass
E. Failure to select an appropriate authentication method for the authentication request
When is the RADIUS server certificate used? (Select two.)
A. During dual SSID onboarding, when the client connects to the Guest network
B. During EAP-PEAP authentication in single SSID onboarding
C. During post-Onboard EAP-TLS authentication, when the client verifies the server certificate
D. During Onboard Web Login Pre-Auth, when the client loads the Onboarding web page
E. During post-Onboard EAP-TLS authentication, when the server verifies the client certificate
Refer to the exhibit.
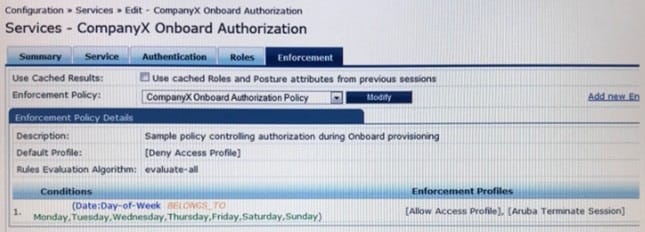
Based on the configuration of the Enforcement Profiles in the Onboard Authorization service shown, which Onboarding action will occur?
A. The device will be disconnected from the network after Onboarding so that an EAP-TLS authentication is not performed.
B. The device will be disconnected from and reconnected to the network after Onboarding is completed.
C. The device's onboard authorization request will be denied.
D. The device will be disconnected after post-Onboarding EAP-TLS authentication, so a second EAP-TLS authentication is performed.
E. After logging in on the Onboard web login page, the device will be disconnected form and reconnected to the network before Onboard begins.