HP0-Y51 Online Practice Questions and Answers
An administrator sets up an OpenFlow instance on an HP Provision switch in passive mode. What does this mean?
A. The switch first attempts to switch or route traffic using its own MAC forwarding and routing tables. If it does not know how to treat the traffic, it uses the OpenFlow table.
B. The switch does not associate this OpenFlow instance with a specific VLAN Instead VLANs that are not assigned to another OpenFlow instance are associated with this instance.
C. The switch matches all traffic in the instance against an OpenFlow table, but, if it finds no match, it forwards the traffic normally
D. The switch does not forward any traffic in the instance locally. Instead, it encapsulates all traffic in OpenFlow Packeket_Out messages to the controller.
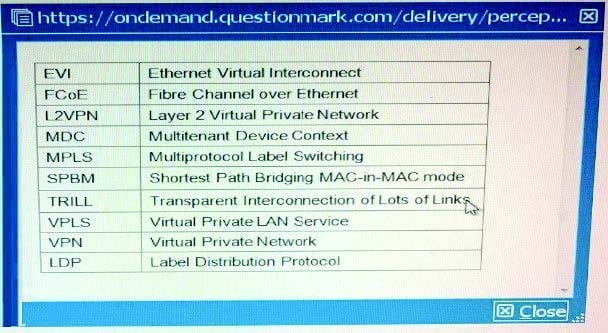
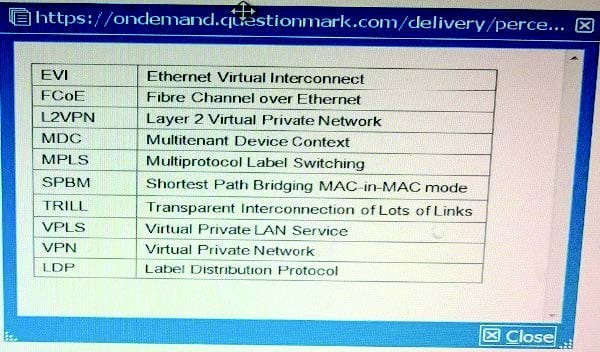
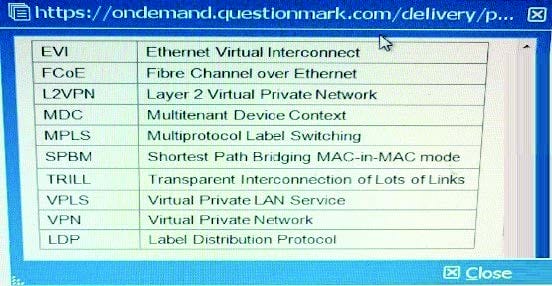
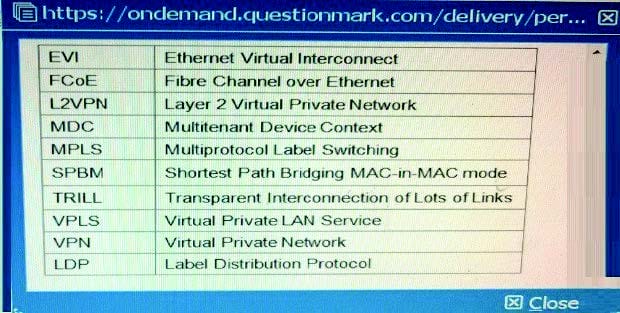
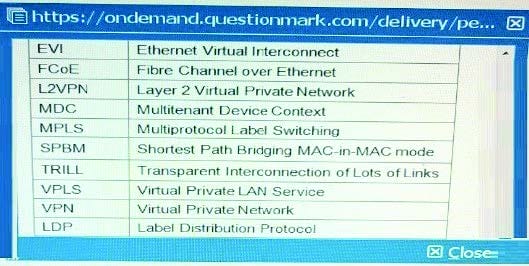
Table of Acronyms
An HP Comware switch is configured with the MDC feature. It has three MDCs, which use the same CPU and are assigned these CPU weights:
MDC 1 = 10
MDC 2 = 4
DC 3 = 2
Currently:
MDC 1 needs to use 25 percent of the CPU resources.
MDC 2 needs to use 60 percent of the CPU resources.
MDC 3 needs to use 60 percent of the CPU resources.
Approximately what percentage of the CPU does each MDC receive while at the current CPU request rates?
A. MDC 1 = 25 percent, MDC 2 = 50 percent, and MDC 3 = 25 percent
B. MDC 1 = 63 percent, MDC 2 = 25 percent, and MDC 3 = 12 percent
C. MDC 1 = 10 percent. MDC 2 = 4 percent, and MDC 3 = 2 percent
D. MDC 1 = 25 percent. MDC 2 = 25 percent, and MDC 3 = 12 percent
Table of Acronyms
An administrator has configured an HP Comware switch to support FCoE in Fibre Channel Forwarder (FCF) mode. A switch interface, ten1/0/1, connects to a sewer FC host bus adapter (HBA), The HBA should send storage traffic in VSAN 2, which is associated with VLAN 20.
How should the administrator assign FC traffic for this HBA to VSAN 2?
A. By binding a VFC interface to ten1/0/1 and specifying VSAN 2 as the VFC interface trunk VSAN
B. By accessing the VLAN 20 configuration view and specifying ten1/0/1 as a member port of the VLAN
C. By configuring ten1/0/1 as an F-mode FC port and specifying VSAN2 as the port access VSAN
D. By accessing the VSAN 2 configuration view and adding ten1/0/1 as a trunk port
A company has an HP BYOD solution. The administrator is setting up synchronization of user accounts from Active Directory (AD). The administrator wants User Access Manager (UAM) to organize the user accounts in groups in the same way that AD does.
How does the administrator configure this to accomplish the goal?
A. Establish the LDAP synchronization policy, and then create a user group policy to synchronize the groups and sort the user accounts
B. In the LDAP Server policy, set the User Group setting to Synchronize by OU, which allows AD to create the groups automatically
C. Install the UAM agent on the AD server, otherwise, UAM can only synchronize the highest- level group of domain users.
D. Create every group before setting up the LDAP synchronization policy
A company has an HP BYOD solution to let guests connect to a Guest SSID and log in through a registration page. The company needs an Employee SSID which enforces Wi-Fi Protected Access 2 (WPA2) with 802.1X. Employees must authenticate with certificates. Before authenticating with a device for the first time, the employees should be able to connect to the Guest SSID, access the guest registration page, and download valid certificates.
How does the administrator configure User Access Manager (UAM) to allow employees to download certificates from the registration page?
A. The User Endpoint Settings, create an Endpoint Configuration Distribution Policy that permits the employee groups.
B. In the Guest Manager settings for the employee manager, enable auto-registration in certificate mode.
C. In the Guest access policy, make sure that a policy binds the Employee SSID to an access rule with the onboarding VLAN ID.
D. In the Employee access service, make sure that a policy binds the Employee SSID to an access rule with the onboarding VLAN ID.
Table of Acronyms
An administrator is setting up an EVI solution on four HP Comware switches. The switches reach each other on these IP address:
Switch1 = 10.1.1.1
Switch2 = 10 2.2 2
Switch3 = 10.3.3.3
Switch4 = 10.4.4.4
The administrator wants to make Switch1 and Switch2 potential EVI Network Discovery Protocol (ENDP) servers. What is the proper configuration on the Switch1 EVI tunnel interface?
A. evi neighbor-discovery server enable evi neighbor-discovery client enable 10.1.1.1
B. evi neighbor-discovery server enable evi neighbor-discovery client enable 10.2.2.2
C. evi neighbor-discovery client enable 10.3.3.3 evi neighbor-discovery client enable 10.4.4.4
D. evi neighbor-discovery client enable 10.3.3.3 evi neighbor-discovery client enable 10.4.4.4
Refer to the exhibit.
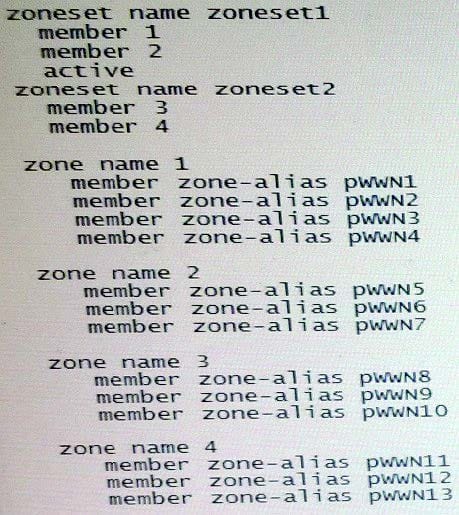
The exhibit shows the Fibre Channel (FQ zones that are members of zonesets on an HP Comware switch. How does this zoning affect the FC fabric operation?
A. Host bus adapter (HBA) pWWNs in zoneset 1 belong to VSAN 1, which is currently active. HBA pWWNs in zoneset 2 belong to VSAN 2, which is inactive
B. Server pWvVNs in zone 1 can discover targets pWWNs in zone 2. Server pWWNs in zone 3 can discover target pWWNs in zone 4.
C. A sender pWWN in zone 1 can discover target pWWNs in zone 1. A server pWWN in zone 2 can discover target pWWNs in zone 2.
D. The switch matches a host bus adapter (HBA) pWWN to entries in zone 1 to determine whether an HBA can connect to a port. If it does not find a match, it checks zone 2.
Refer to the exhibit.
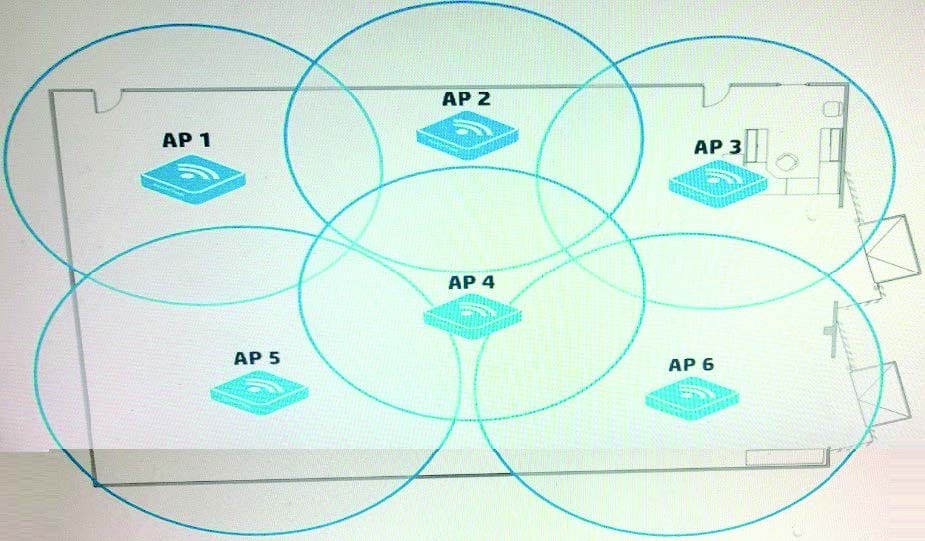
A company has many dual-radio APs that are deployed relatively closely together. They are controlled by an HP Unified Wired-Wireless controller. The administrator wants to implement load balancing among the radios on different APs.
How should the administrator implement load balancing?
A. Implement group-based load balancing by adding radios on different APs to the group.
B. Implement radio-based load balancing by adding APs to the radio templates.
C. Implement AP-based load balancing on the individual APs.
D. Implement AP-based load balancing on the radios of the individual APs.
A company has an HP BYOD solution with these requirements:
Employees can connect their own devices to an Employees SSID, which enforces Wi-Fi Protected Access 2 (WPA2) with 802.1X.
User Access Manager (UAM) is the RADIUS server for 802.1X authentication, and it enforces EAP-TLS.
The employees will first connect to an open SSID, access a portal page, and download the proper certificates for completing 802.1X authentication.
To meet these requirements, an administrator needs to deploy the correct certificate templates on UAM. What determine deploy?
A. Whether the company uses Active Directory (AD) or Open LDAP
B. Type of endpoint devices and the device operating systems (OS)
C. Government regulations with which the company must comply
D. Level of security that the company requires
Table of Acronyms
A company is using Multi-CE (MCE) to create a multi-tenant data center solution. Administrators want to isolate all functions in a VPN instance "Management".
Each switch has an IP address in 10.0.2.0/24 on its Management Ethernet port, and HP IMC manages the switch on these IP addresses. Administrators assign
the Management Ethernet interfaces to the "Management" VPN instance. IMC begins losing data from the switches. How should administrators fix the problem on each switch?
A. Set VPN instance "Management" as the default VPN instance.
B. Specify VPN instance "Management" for settings such as the SNMP trap destination
C. Create a static route to 10.0.2.0/24 through next hop "vpn-instance Management".
D. Enable route leaking globally and on VPN instance "Management".
A Company has APs that are deployed relatively close together. These APs are controlled by an HP Unified Wired-Wireless controller. Which setting helps to prevent the APs from interfering with each other while also letting the APs extend their coverage area if one of the AP fails?
A. Channel reuse
B. Dynamic frequency selection (DFS)
C. Transmit power control (TPC)
D. Fair scheduling
A company has an HP Unified Wired-Wireless controller that controls HP MultiService Mobility (MSM) APs. The network administrator wants to implement protection against rogue APs in the company's campus environment. Only APs that have approved MAC addresses should be allowed to operate and support clients. Controlled APs should send disassociation frames to prevent clients from connecting to rogue APs.
The administrator sets up APs to monitor the area and creates a permitted MAC address list with the approved AP MAC addresses. The administrator has not configured any other Intrusion Detection System (IDS) settings. Which additional step must the administrator complete?
A. Enable a dynamic blacklist.
B. Configure the permitted vendor and permitted SSID lists.
C. Enable countermeasures.
D. Deploy the permitted MAC address list as a static attack list to each controlled AP
Table of Acronyms
Refer to the exhibit.
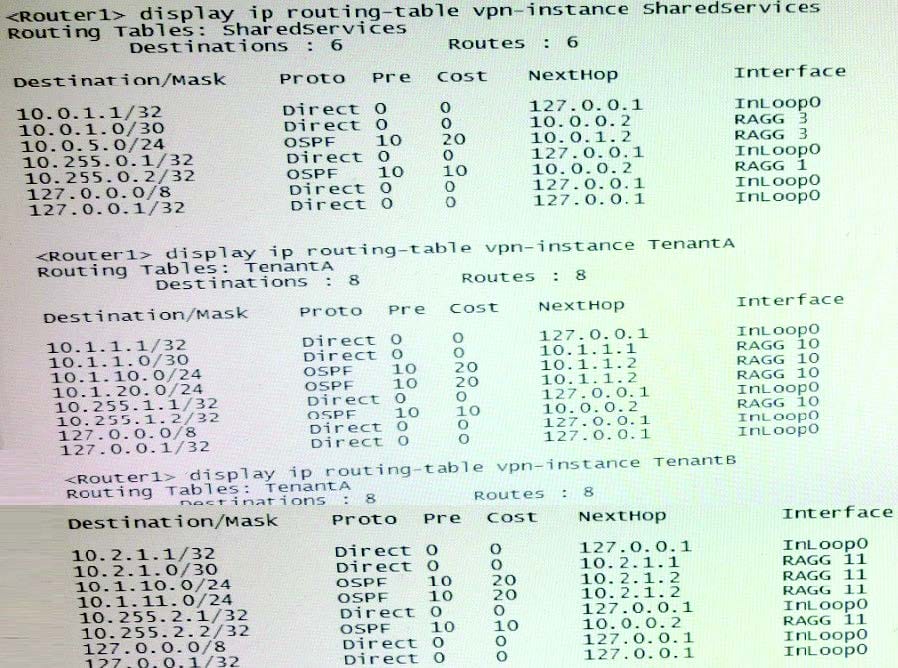
An administrator wants to route all external traffic from VPN instances "TenantA" and "TenantB" to a firewall at 10.0.5.5 instance "SharedServices". In addition to setting up the routes between the instances, what is another requirement for this scenario?
A. A router must implement Network Address Translation (NAT) to translate overlapping tenant network addresses.
B. Route leaking must be enabled globally on Router1, as well as on each of the VPN instances.
C. The RAGG 3 interface must be added to VPN instances "TenantA" and "TenantB".
D. Route leaking must be enabled globally on Router1.
An administrator is customizing an HP BYOD self-registration page. The administrator does not want guests to see the identity number field. Instead the User Access Manager (UAM) server should automatically choose a valid identity number for a guest account when the guest registers.
What are the correct settings for the identity number field in the customized page? (Select three)
A. Required
B. Fixed
C. Not required
D. Invisible
E. Random
F. Visible
Table of Acronyms
Refer to the exhibit.
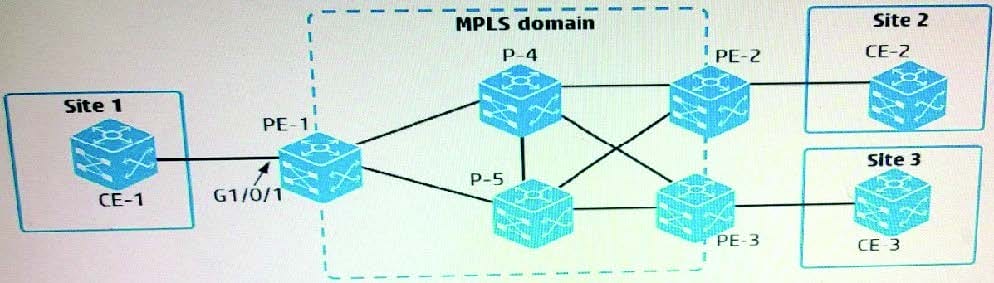
An administrator is setting up MPLS Layer 2 VPN connections between several customer sites:
Connection 1 = Customer site 1 to customer site 2
Connection 2 = Customer site 1 to customer site 3
On PE-1, interface GigabitEthernet1/0/1 connects to CE-1 at site 1. Which setup establishes the desired connections?
A. CE-1 connects to CE-2 in one VLAN, which it assigns to VPN instance 1. It connects to CE-3 in a different VLAN, which it assigns to VPN instance 2. PE-1 instant places G1/0/1 in both VPN instances 1 and 2 and associates each VPN instance with a PW for one of the connections.
B. CE-1 connects to CE-2 in one VLAN and to CE-3 in a different VLAN. PE-1 has two services instances on G1/D/1. One instance encapsulates one VLAN ID and has PW to PE-2, and the other instance encapsulates the other VLAN and has a PW to PE-3
C. PE-1 has two policy-based routing (PBR) policies, each of which selects traffic destined to Site 2 or Site 3. The appropriate policy is applied to the PW for each connection
D. CE-1 implements MPLS. It establishes two PWs with PE-1, one for its connection to CE-2 and one for its connection to CE-3. PE-1 maps the out label for the first PW to the in label for a PW to PE-2. It maps the labels similarly for a PW to PE-3.
