H12-831 Online Practice Questions and Answers
What characteristics must a high-risk operation plan have?
A. with verification
B. Strong operability
C. accurate
D. can return
As shown in the figure, SF is enabled on all interfaces of the router, the cost value of the link is marked in the figure, and the Loopback0 interface of R2 is advertised in area 1, then the cost value of R1 reaching 10.0.2.2/32 is?
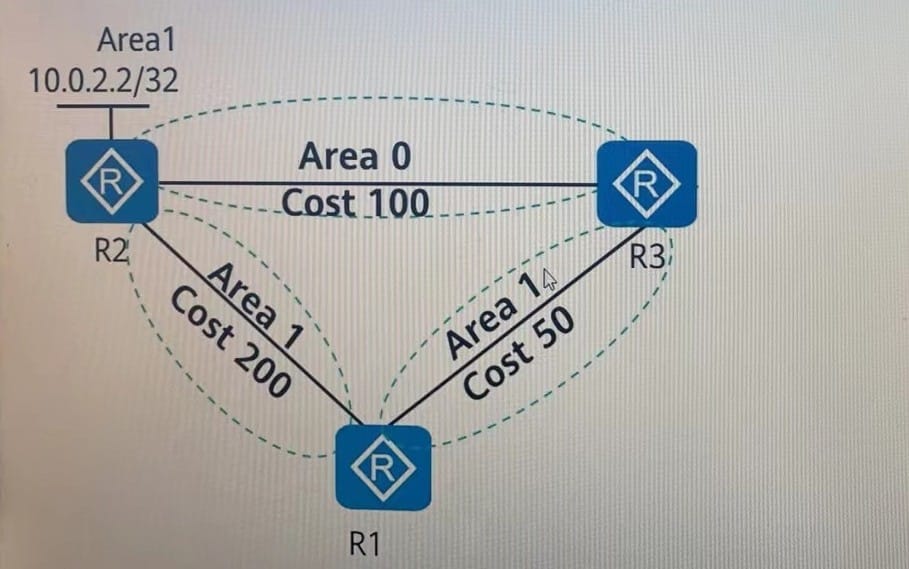
A. 100
B. 150
C. 50
D. 200
For the same MA, C address, manually configured MA, C entries have higher priority than automatically generated entries.
A. True
B. False
Which of the following statements about LDP Label Retention - Free Way is true:
A. Requires more memory and tab space
B. Keep all labels distributed by neighbors
C. Only keep labels from next-hop neighbors and discard all labels from next-hop neighbors
D. Save memory and label space
As shown in the figure, configure a backhaul summary route 10.0.0.0/24 on the border route RT1. next hop to RT2. At the same time, the default route to the external network is configured. At this point, a routing black hole will appear. The following is about routing.
Is the black hole statement correct? (multiple choice)

A. Configuring black hole routing can solve the routing black hole problem
B. Routing black hole has no impact on the network and can be ignored
C. Precise routing $ can always avoid routing black holes
D. If the terminal in the network sends data packets to the network segment that does not appear on the internal network, a loop will occur
Which of the following regular expressions can match only BGP routes that pass through AS200 and then through AS300 eyes?
A. 200$|300$
B. A200|A300
C. _(200 300)_
D. _[200 300]
As shown in the figure, private network routing information is exchanged between PE1 and PE2 and their respective CEs through OSPF, and the same DomainlD is set on both PE1 and PE2. When routes are imported from BGP to OSPF on
PE2, it is possible that.
Which of the following types of SAs are passed to CE2?
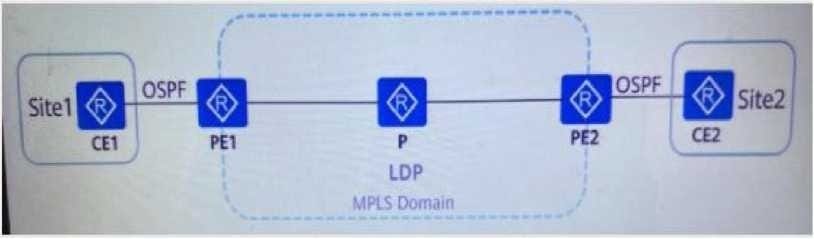
A. Typel LSA
B. Type3 LSA
C. Type7 LSA
D. Type5 LSA
As shown in the figure, Sitel and Site2 need to achieve mutual access through the operator's BGP/MPLS IPVPN. A known The public network tunnel between PE1 and PE2 has been established (the label information is shown in the figure), and PF1 has The 192.168.1.0/24 network segment route is advertised to PE2 through the MP.JIBGP neighbor relationship, and the route learning is normal. When grabbing between P and PE1, when Site2 accesses the 192.168.1.0/24 data of Sitel, the
outermost label What should the sign be?

FEC In/Out label 1.1.1.1/32 6662/3
A. 6661
B.
C. 6662
D. 8888
Regarding the description of the encapsulation format of labels in MPLS, the correct one is
A. MPLSThe total length of a single label is4bytes(32bits)
B. For Ethernet,PPPpacket, the tag stack is like 'shim*--between the L2 header and the data: yesVLAN tagTime,MPLShead on the ether head withVLAN tagbetween
C. in the labelSfield:lbit,Used to identify whether the label is the bottom label of the stack, the value is1is indicated as the penultimate layer label
D. in the labelTTLfields andIPgroupedTTL( Time To Live.,time-to-live) is similar in meaning and also has the effect of preventing loops
Which of the following is not part of the preparatory work for the cutover plan?
A. field defense
B. Cutover target
C. Root description of the current network
D. risk assessment
Does the role of Link-LSA in OSPFv3 not include?
A. To the other road on the link Tiandikou noon-
B. Advertise this router's interface to other routers on the linkID
C. Advertise the link-local address of this interface to other routers on the link
D. Advertise to other routers on the link the originatingNetwork-LSAOptions set in
A network engineer entered the following information when troubleshooting OSPF faults. Based on this, you can judge what causes the adjacency relationship to fail to be established normally?
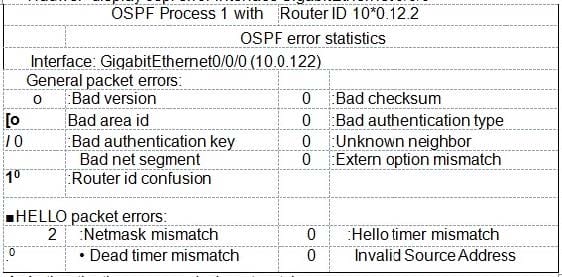
A. Authentication passwords do not match
B. Inconsistent area type
C. Hell. Inconsistent message sending interval
D. interfaceIPInconsistent address masks
To prevent hackers from attacking user devices or networks through MA, C addresses, you can configure the MA, C addresses of untrusted users as black hole MA, C addresses to filter out illegal MA, C addresses.
A. True
B. False
(Drag and drop question) The configuration shown in the figure is performed on R2 to filter all incoming routes. Suppose there is an entry on R1 AS_Path attribute is [100 200 300 400] BGP routes need to be sent to R2, please help network administrators in Adjust the AS order in the AS_Path attribute of the route on R1 to ensure that the route entry will not be routed by R2 route^policy AS-PATH permit node 10 if-match as-path-filter BGP route-policy AS-PATH deny node 20 ip as-path-filter BGP permit A[A2]00 400 100_
route-policy AS-PATH permit node 10 if-match ip-prefix BGP apply as-pathoverwrite ip ip-prefix BGP permit 10.0.0.0 24
A. 300--A 400--C 100--B 200--D
B. 300--A 400--B100--C 200--D
C. 300--B 400--A 100--C 200--D
D. 300--C 400--A 100--B 200--D
Link LSAs of OSPFv3 are propagated throughout the area.
A. right
B. wrong
