EPM-DEF Online Practice Questions and Answers
What EPM component is responsible for communicating password changes in credential rotation?
A. EPM Agent
B. EPM Server
C. EPM API
D. EPM Discovery
An application has been identified by the LSASS Credentials Harvesting Module.
What is the recommended approach to excluding the application?
A. In Agent Configurations, add the application to the Threat Protection Exclusions
B. Add the application to the Files to be Ignored Always in Agent Configurations.
C. Exclude the application within the LSASS Credentials Harvesting module.
D. Add the application to an Advanced Policy or Application Group with an Elevate policy action.
What are the predefined application groups?
A. Developer group, Administrator group
B. Run as Administrator, Run as Developer, Block
C. Elevate, Allow, Block, Developer Applications
D. Block Only
How does CyberArk EPM's Ransomware Protection feature monitor for Ransomware Attacks?
A. It compares known ransomware signatures retrieved from virus databases.
B. It sandboxes the suspected ransomware and applies heuristics.
C. It monitors for any unauthorized access to specified files.
D. It performs a lookup of file signatures against VirusTotal's database.
What type of user can be created from the Threat Deception LSASS Credential Lures feature?
A. It does not create any users
B. A standard user
C. A local administrator user
D. A domain admin user
How does EPM help streamline security compliance and reporting?
A. Use of automated distribution of reports to the security team
B. Provides reports in standard formats such as PDF, Word and Excel
C. Print reports
D. Create custom reports
Can the EPM Set Administrator configure Audit Dialog Pop-ups for the Record Audit Video option?
A. Yes, when Audit Video recording started, when Audit Video recording stopped, and when Audit Recording video reached size limit.
B. Yes, when Audit Video recording started, when not enough disk space to start the video recording, and when video recording is initializing.
C. Yes, when Audit Video recording started, when Audit Video recording is uploaded to the EPM server, and when audit recording cannot be initialized.
D. No, Audit Video is only available without the possibility of having End-User dialog pop- ups.
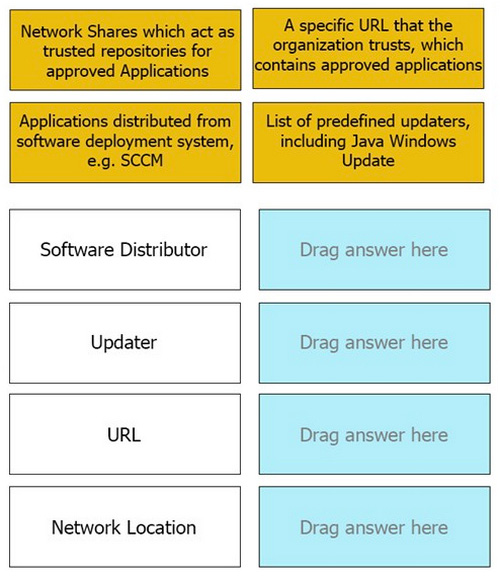
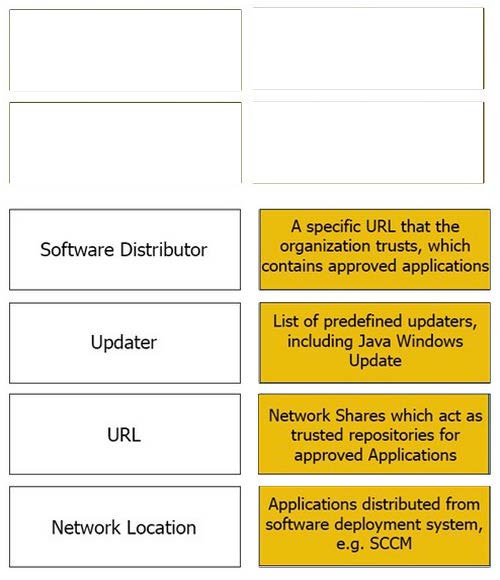
DRAG DROP
Match the Trusted Source to its correct definition:
Select and Place: