DEA-3TT2 Online Practice Questions and Answers
DRAG DROP
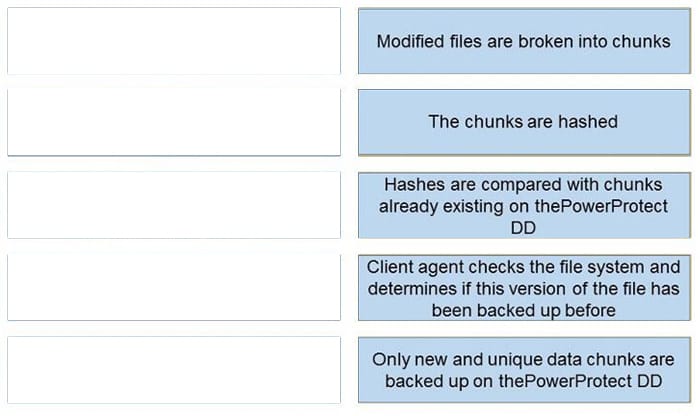
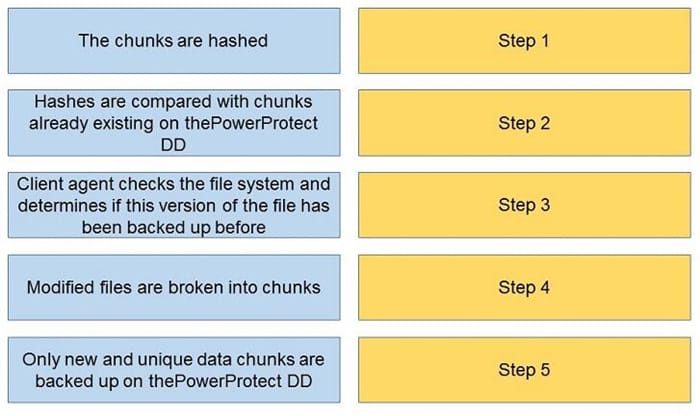
What is the correct sequence of actions during a DDBoost backup?
Select and Place:
DRAG DROP
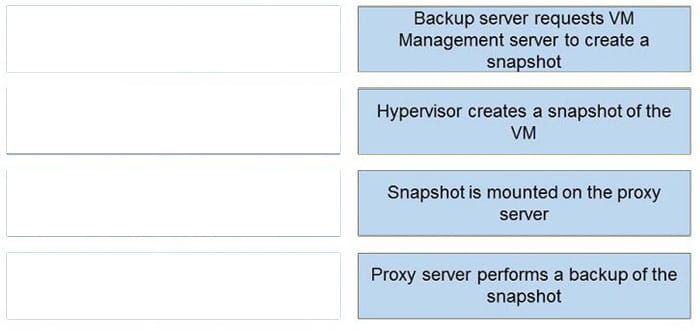
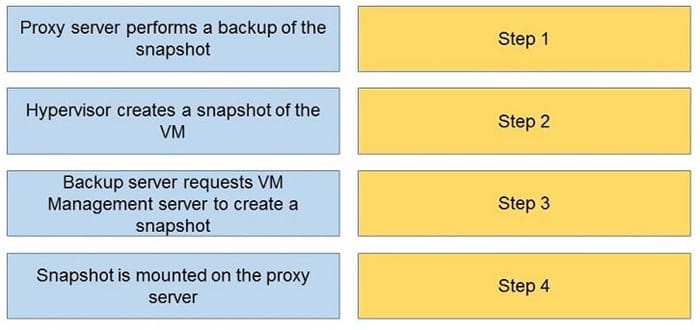
What is the correct sequence of steps during an image-based backup?
Select and Place:
Which Dell EMC Storage product family does SRDF support?
A. Unity
B. PowerMax
C. PowerScale
D. PowerStore
Which type of virtual machine clone is created from a snapshot of a parent VM?
A. Mirrored Clone
B. Full Clone
C. Linked Clone
D. Snap Clone
Refer to the exhibit.
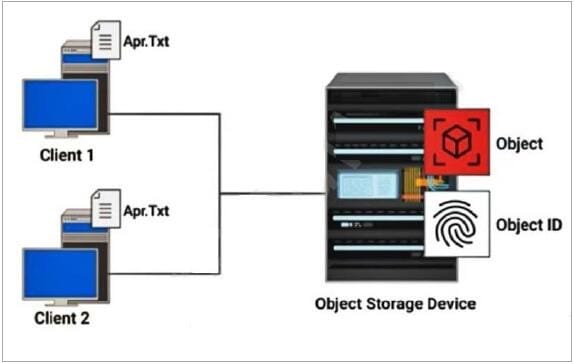
How is a hash created on file Apr.Txt in an object-level deduplication?
A. from content with variable-length
B. from the metadata of the file
C. from the content of the file
D. from content with fixed-length
A computer has an MTBF of 7000 hours and an MTTR of 18 hours? What is the availability of the data?
A. 90.7%
B. 99.1%
C. 99.7%
D. 99.8%
A customer has created a change management window to perform scheduled system maintenance. During the scheduled downtime window, information will be transferred to another system to ensure continuous availability. What is this process an example of?
A. Data governance
B. Data migration
C. Automated failback
D. Disaster recovery
What is a characteristic of data archiving?
A. Secondary copy of data
B. Primary copy of data
C. Short-term retention
D. Used for operational recovery
What is a hot backup?
A. application is up-and-running with users accessing their data during the backup process
B. backup is indexed from last full backup
C. a full backup is synthesized
D. requires the application to be shut down during the backup process
Which plane of SDDC is used to perform administrative operations such as configuring a system and changing policies?
A. Management Plane
B. Service Plane
C. Control Pane
D. Data Plane
Which data migration involves migrating data at the file level using intermediary compute systems?
A. Host-based migration
B. NAS-based migration
C. SAN-based migration
D. Application migration
What makes services visible and accessible to the users?
A. Service Catalog
B. Operational Database
C. Cloud native application
D. Unified storage system
Which type of file system can be mounted on multiple compute systems running a hypervisor to access the same file system simultaneously?
A. Memory state file system
B. Clustered file system
C. Configuration file system
D. Virtual disk file system
What are the considerations when designing a disaster recovery plan based on RTO and RPO?
A. Lower RTO and RPO have no effect on cost
B. Lower RTO and RPO simplify the solution
C. Lower RTO and RPO decrease the cost
D. Lower RTO and RPO increase the cost
What determines if a user, device, application, or process is allowed to access a service or a resource?
A. auditing
B. authorization
C. authentication
D. accountability