CV0-004 Online Practice Questions and Answers
SIMULATION
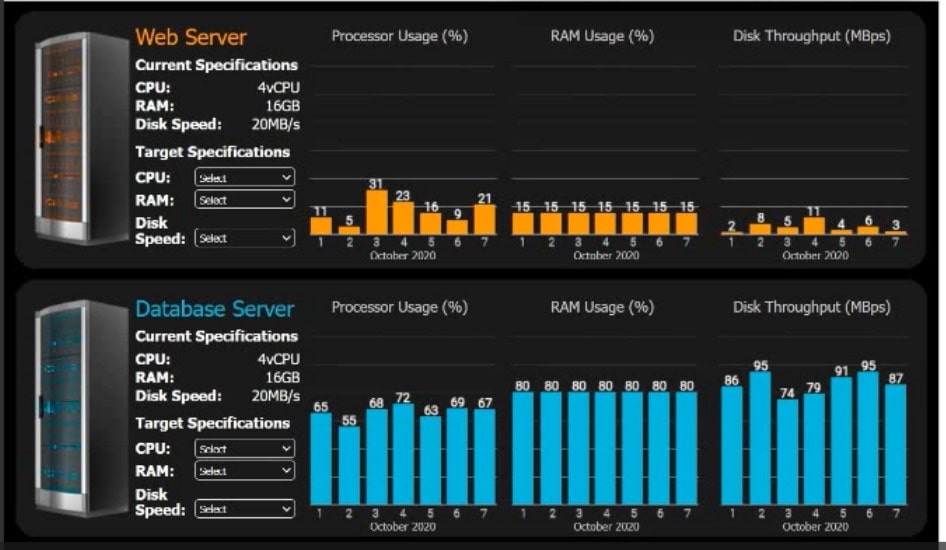
An e-commerce company is migrating from an on-premises private cloud environment to a public cloud IaaS environment. You are tasked with right-sizing the environment to save costs after the migration. The company's requirements are to provide a 20% overhead above the average resource consumption, rounded up.
INSTRUCTIONS
Review the specifications and graphs showing resource usage for the web and database servers. Determine the average resource usage and select the correct specifications from the available drop-down options.
A. Check the for the complete Solution.
B. PlaceHolder
C. PlaceHolder
D. PlaceHolder
A customer's facility is located in an area where natural disasters happen frequently. The customer requires the following:
1.
Data resiliency due to exposure to frequent natural disasters
2.
Data localization because of privacy regulations in the country
3.
High availability
Which of the following cloud resources should be provisioned to meet these requirements?
A. Storage in a separate data center located in same region
B. An on-premises private cloud carrying duplicate data
C. Storage in an availability zone outside the region
D. Storage in the same availability zone as the primary data
A cloud developer needs to update a REST API endpoint to resolve a defect. When too many users attempt to call the API simultaneously, the following message is displayed:
Error: Request Timeout - Please Try Again Later
Which of the following concepts should the developer consider to resolve this error?
A. Server patch
B. TLS encryption
C. Rate limiting
D. Permission issues
A network administrator is budding a site-to-site VPN tunnel from the company's headquarters office 10 the company's public cloud development network. The network administrator confirms the following:
The VPN tunnel is established on the headquarter office firewall.
While inside the office, developers report that they cannot connect to the development network resources.
While outside the office on a client VPN, developers report that they can connect to the development network resources.
The office and the client VPN have different IP subnet ranges.
The firewall flow logs show VPN traffic is reaching the development network from the office.
Which of the following is the next step the next network administrator should take to troubleshoot the VPN tunnel?
A. Review the development network routing table.
B. Change the ciphers on the site-to-site VPN.
C. Restart the site-to-site VPN tunnel.
D. Check the ACLS on the development workloads
A group of cloud administrators frequently uses the same deployment template to recreate a cloud-based development environment. The administrators are unable to go back and review the history of changes they have made to the template.
Which of the following cloud resource deployment concepts should the administrator start using?
A. Drift detection
B. Repeatability
C. Documentation
D. Versioning
Which of the following describes the main difference between public and private container repositories?
A. Private container repository access requires authorization, while public repository access does not require authorization.
B. Private container repositories are hidden by default and containers must be directly referenced, while public container repositories allow browsing of container images.
C. Private container repositories must use proprietary licenses, while public container repositories must have open-source licenses.
D. Private container repositories are used to obfuscate the content of the Dockerfile, while public container repositories allow for Dockerfile inspection.
Which of the following refers to the idea that data should stay within certain borders or territories?
A. Data classification
B. Data retention
C. Data sovereignty
D. Data ownership
A web-application company recently released some new marketing promotions without notifying the IT staff. The systems administrator has since been noticing twice the normal traffic consumption every two hours for the last three hours in the container environment.
Which of the following should the company implement to accommodate the new traffic?
A. A firewall
B. Switches
C. Ballooning
D. Autoscaling
