CAS-005 Online Practice Questions and Answers
SIMULATION
An organization is planning for disaster recovery and continuity of operations, and has noted the following relevant findings:
1.
A natural disaster may disrupt operations at Site A, which would then cause an evacuation. Users are unable to log into the domain from-their workstations after relocating to Site B.
2.
A natural disaster may disrupt operations at Site A, which would then cause the pump room at Site B to become inoperable.
3.
A natural disaster may disrupt operations at Site A, which would then cause unreliable internet connectivity at Site B due to route flapping.
INSTRUCTIONS
Match each relevant finding to the affected host by clicking on the host name and selecting the appropriate number.
For findings 1 and 2, select the items that should be replicated to Site B. For finding 3, select the item requiring configuration changes, then select the appropriate corrective action from the drop-down menu.
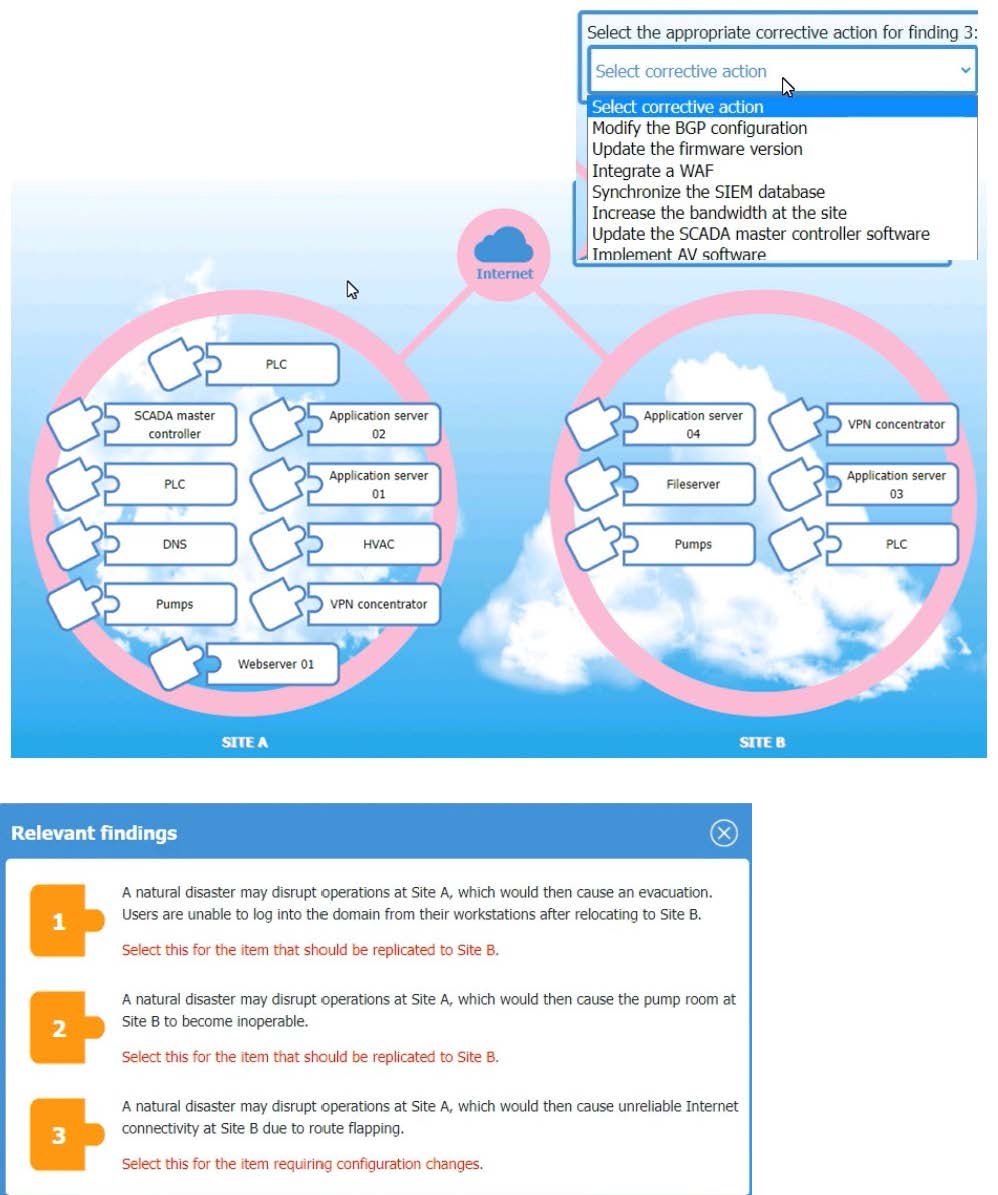
A. See the complete solution below in Explanation.
B. PlaceHolder
C. PlaceHolder
D. PlaceHolder
SIMULATION
Compliance with company policy requires a quarterly review of firewall rules. A new administrator is asked to conduct this review on the internal firewall sitting between several internal networks. The intent of this firewall is to make traffic more
restrictive. Given the following information answer the questions below:
User Subnet: 192.168.1.0/24 Server Subnet: 192.168.2.0/24 Finance Subnet:192.168.3.0/24
Instructions: To perform the necessary tasks, please modify the DST port, Protocol, Action, and/or Rule Order columns. Firewall ACLs are read from the top down
Task 1) An administrator added a rule to allow their machine terminal server access to the server subnet. This rule is not working. Identify the rule and correct this issue.
Task 2) All web servers have been changed to communicate solely over SSL. Modify the appropriate rule to allow communications.
Task 3) An administrator added a rule to block access to the SQL server from anywhere on the network. This rule is not working. Identify and correct this issue.
Task 4) Other than allowing all hosts to do network time and SSL, modify a rule to ensure that no other traffic is allowed.
Check the solution below.
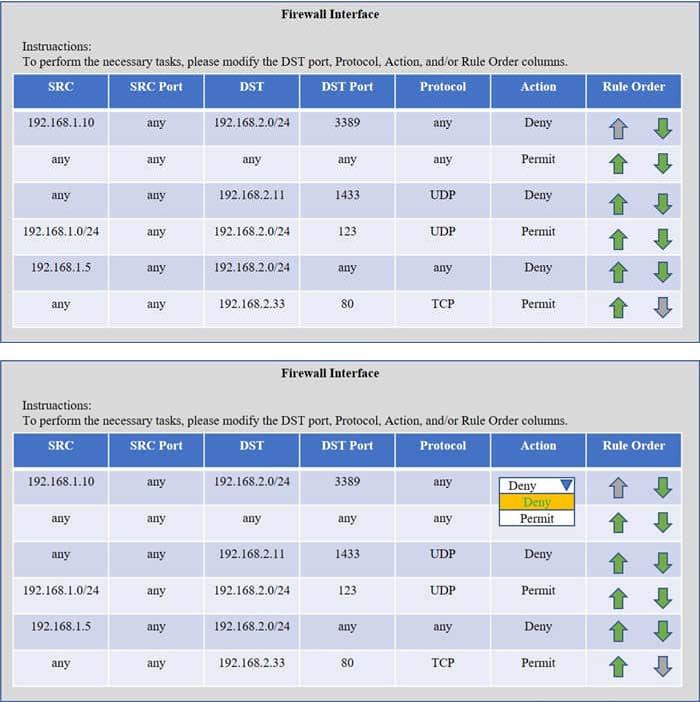
A. See the complete solution below in Explanation.
B. PlaceHoder
C. PlaceHoder
D. PlaceHoder
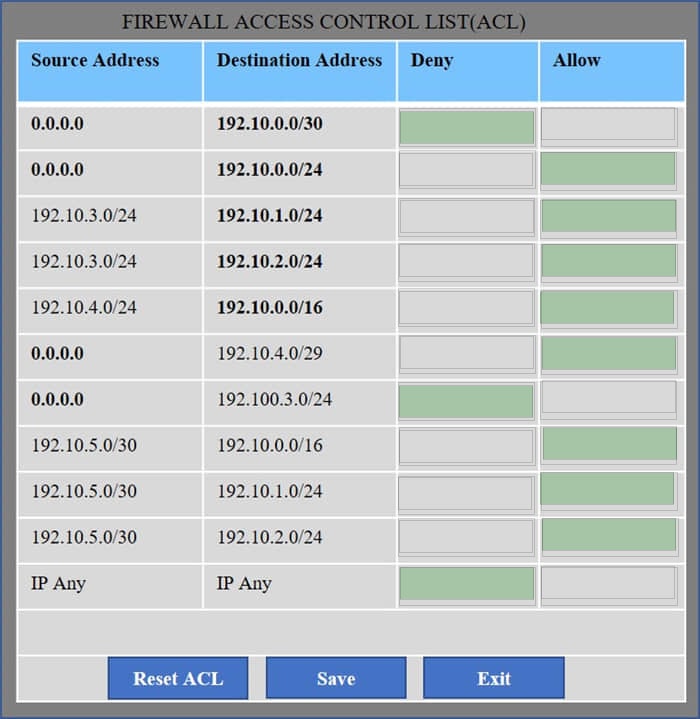
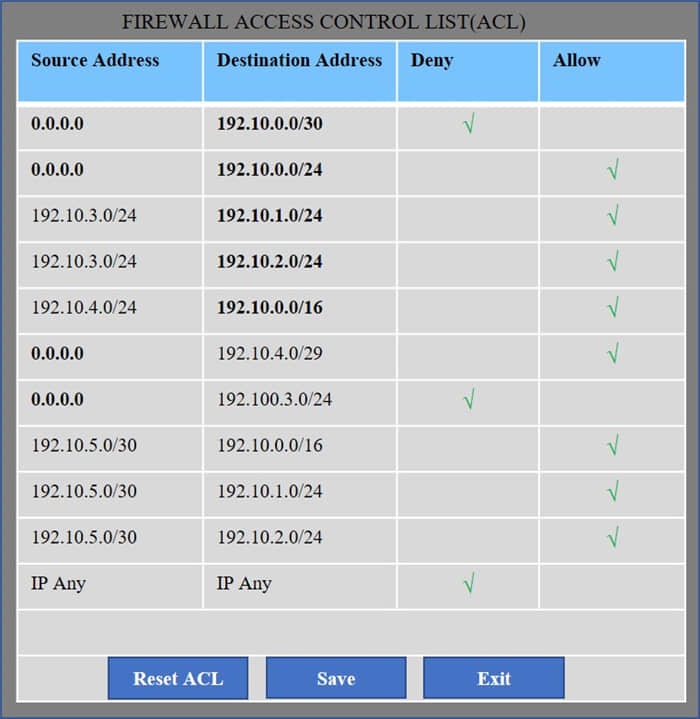
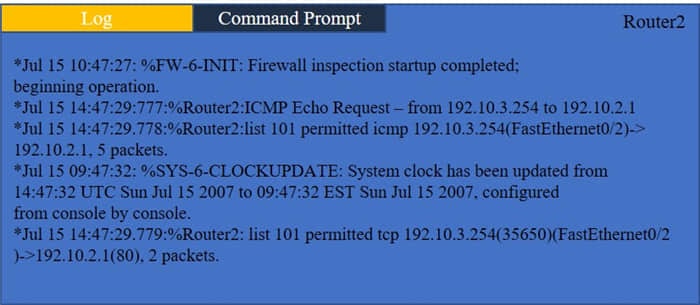
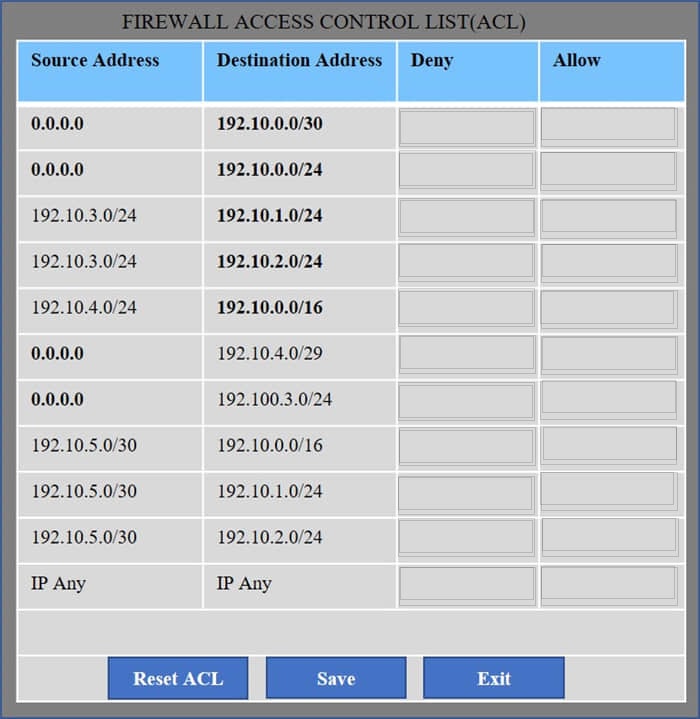
HOTSPOT
Company A has noticed abnormal behavior targeting their SQL server on the network from a rogue IP address. The company uses the following internal IP address ranges: 192.10.1.0/24 for the corporate site and 192.10.2.0/24 for the remote
site. The Telco router interface uses the 192.10.5.0/30 IP range.
Instructions: Click on the simulation button to refer to the Network Diagram for Company A.
Click on Router 1, Router 2, and the Firewall to evaluate and configure each device.
Task 1: Display and examine the logs and status of Router 1, Router 2, and Firewall interfaces.
Task 2: Reconfigure the appropriate devices to prevent the attacks from continuing to target the SQL server and other servers on the corporate network.
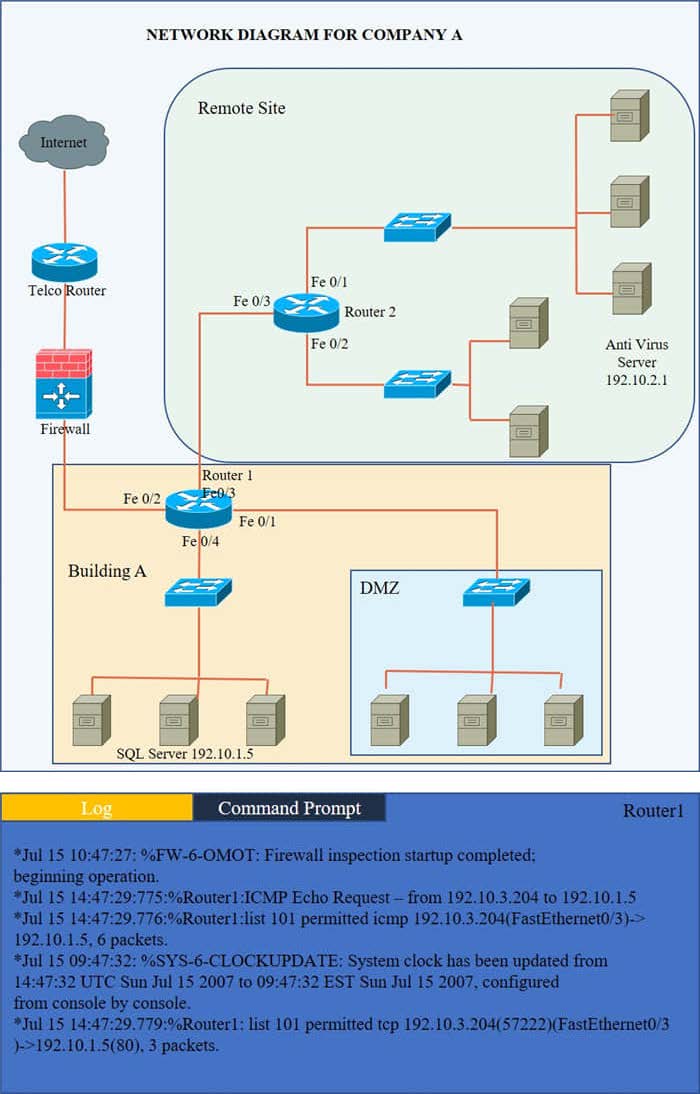
Hot Area:
A company wants to install a three-tier approach to separate the web. database, and application servers A security administrator must harden the environment which of the following is the best solution?
A. Deploying a VPN to prevent remote locations from accessing server VLANs
B. Configuring a SASb solution to restrict users to server communication
C. Implementing microsegmentation on the server VLANs
D. installing a firewall and making it the network core
A company isolated its OT systems from other areas of the corporate network These systems are required to report usage information over the internet to the vendor
Which oi the following b*st reduces the risk of compromise or sabotage? (Select two).
A. Implementing allow lists
B. Monitoring network behavior
C. Encrypting data at rest
D. Performing boot Integrity checks
E. Executing daily health checks
F. Implementing a site-to-site IPSec VPN
Which of the following best explains the importance of determining organization risk appetite when operating with a constrained budget?
A. Risk appetite directly impacts acceptance of high-impact low-likelihood events.
B. Organizational risk appetite varies from organization to organization
C. Budgetary pressure drives risk mitigation planning in all companies
D. Risk appetite directly influences which breaches are disclosed publicly
An organization is required to
1.
Respond to internal and external inquiries in a timely manner
2.
Provide transparency.
3.
Comply with regulatory requirements
The organization has not experienced any reportable breaches but wants to be prepared if a breach occurs in the future.
Which of the following is the best way for the organization to prepare?
A. Outsourcing the handling of necessary regulatory filing to an external consultant
B. Integrating automated response mechanisms into the data subject access request process
C. Developing communication templates that have been vetted by internal and external counsel
D. Conducting lessons-learned activities and integrating observations into the crisis management plan
A company's SICM Is continuously reporting false positives and false negatives The security operations team has Implemented configuration changes to troubleshoot possible reporting errors
Which of the following sources of information best supports the required analysts process? (Select two).
A. Third-party reports and logs
B. Trends
C. Dashboards
D. Alert failures
E. Network traffic summaries
F. Manual review processes
A systems administrator wants to introduce a newly released feature for an internal application. The administrate docs not want to test the feature in the production environment.
Which of the following locations is the best place to test the new feature?
A. Staging environment
B. Testing environment
C. CI/CO pipeline
D. Development environment
A company that uses containers to run its applications is required to identify vulnerabilities on every container image in a private repository The security team needs to be able to quickly evaluate whether to respond to a given vulnerability.
Which of the following, will allow the security team to achieve the objective with the last effort?
A. SAST scan reports
B. Centralized SBoM
C. CIS benchmark compliance reports
D. Credentialed vulnerability scan
The following messages are displayed when a VPN client is attempting to connect to an OpenVPN server:
OpenSSL: error: 140760FC:SSL routines: SSL23_GET_CLIENT_HELLO: unknown protocol' TLS_ERROR: BIO read tls_read_plaintext error' TLS_ERROR: TLS object->incoming plaintext read error'
TLS_ERROR: TLS handshake failed'
SIGUSR1 [soft, tls_error] received, client_instance restarting'
Which of the following best explains the cause of these messages?
A. The client is attempting to establish an unencrypted connection with the server.
B. The server is unreachable to the client and a connection cannot be established.
C. The client is using LibreSSL libraries while the server is using OpenSSL libraries.
D. A TLS version mismatch exists between the client and the server.
Following a Log4j outbreak, several network appliances were not managed and remained undetected despite an application inventory system being in place. Which of the following solutions should the security director recommend to best understand the composition of applications on unmanaged devices?
A. Protocol analyzer
B. Package monitoring
C. Software bill of materials
D. Fuzz testing
A security engineer has learned that terminated employees' accounts are not being disabled. The termination dates are updated automatically in the human resources information system software by the appropriate human resources staff. Which of the following would best reduce risks to the organization?
A. Exporting reports from the system on a weekly basis to disable terminated employees' accounts
B. Granting permission to human resources staff to mark terminated employees' accounts as disabled
C. Configuring allowed login times for all staff to only work during business hours
D. Automating a process to disable the accounts by integrating Active Directory and human resources information systems
Which of the following security features do email signatures provide?
A. Non-repudiation
B. Body encryption
C. Code signing
D. Sender authentication
E. Chain of custody
A Chief Information Security Officer is concerned about the condition of the code security being used for web applications. It is important to get the review right the first time, and the company is willing to use a tool that will allow developers to validate code as it is written. Which of the following methods should the company use?
A. SAST
B. DAST
C. Fuzz testing
D. Intercepting proxy