NS0-504 Online Practice Questions and Answers
How can you "throttle" SnapValue updates and baseline transfers so that the primary or secondary is not transmitting data as it can?
A. Use the k option in the snapvault start or snapshot modify commands.
B. SnapVault does not support throttling of network throughout.
C. Use the snapvault throttle command.
D. Use the k option in the snapvault initialize command.
The root admin on the UNIX box receives an "Access Denied" message when he attempts to access a newly mounted qtree. What's the most likely cause of this error?
A. The qtree is missing from the /etc/hosts file.
B. NFS is turned off on the storage system.
C. The qtree is set to ntfs security style.
D. The qtree has not been exported.
Host multi-pathing describes a ____________ solution that has at least two distinct ______________ paths to a LUN.
A. Token ring, physical
B. FC SAN, virtual
C. FC or IP SAN, virtual
D. FC or IP SAN, Physical
When will a Volume SnapMirror (VSM) from a 64-bit source to a 32-bit destination volume fail?
A. When the 64-bit volumes has Volume Guarantee disabled
B. When the 64-bit volume has compression enabled
C. When the 64-bit volume has FlexShare enabled
D. When the 64-bit volume has ASIS enabled
For automatic user name mapping to occur for a CIFS and UNIX user name that are the same, you must do what?
A. Enter the CIFS user in the NIS database.
B. Enter the user names in the /etc/hosts.equiv file.
C. Use both a NIS server and a Domain Controller in the network.
D. Nothing: mapping will occur if user name authentication is available.
Which command would you use to verify that the iSCSI service is running?
A. iscsi protocol
B. iscsi service
C. iscsi show
D. iscsi status
SnapMirror will automatically try to restart a transfer after ___________.
A. an initial transfer is interrupted
B. a manual update is interrupted
C. a transfer interrupted by reboot
D. a scheduled incremental update is interrupted
The snapvault restore command is run on the _________.
A. secondary system to push data to the primary system
B. primary system to pull data from the secondary system
C. secondary system to pull data from the primary system
D. secondary system to push data to the primary storage system
In an active/active configuration in takeover mode, the surviving controller interfaces will reflect the identity of the ________.
A. local interfaces only
B. failed partner interfaces only
C. local and failed partner interfaces
D. interfaces as defined in the /etc/rc file
Which two statements are true of the cf forcetakeover -d command? (Choose two.)
A. Mirrored volumes are implicitly split.
B. Partner mailboxes must be available.
C. The failed cluster node is powered off automatically.
D. The surviving cluster node takes over the functions of the failed partner.
In Data ONTAP, the root user is exempt from these two quotas: _______. (Choose two.)
A. file quotas
B. group quotas
C. root quotas
D. tree quotas
E. user quotas
Which configuration for primary block (FC and iSCSI) data does NetApp best practices recommend? (Choose two.)
A. single controller single shelf
B. single controller multiple shelves
C. dual controller single shelf
D. dual controller multiple shelves
Which storage system combination is supported in Cluster-Mode?
A. a pair of FAS3270s and a pair of FAS3020s
B. a pair of FAS3270s with a FAS3240 and a FAS6240
C. a pair of FAS6280s and a pair of E7900s
D. a pair of FAS6280s and a pair of FAS3240s
An administrator for a virtual server named abc17 mounts a new volume named vola at junction named / accounting/teama and creates two directories at the root of the new volume named 2011 and 2011/june. He also copies a file called report.doc into the directory named june. An NFS client mounts to the root of the namespace. What is the fully qualified path to report.doc?
A. /abc17/accounting/teama/2011/june/report.doc
B. /accounting/teama/2011/june/report.doc
C. /accounting/vola/teama/2011/june/report.doc
D. /vol/vola/2011/june/report.doc
E. Z:\vola\2011\june\report.doc
Given the information shown in the diagram,
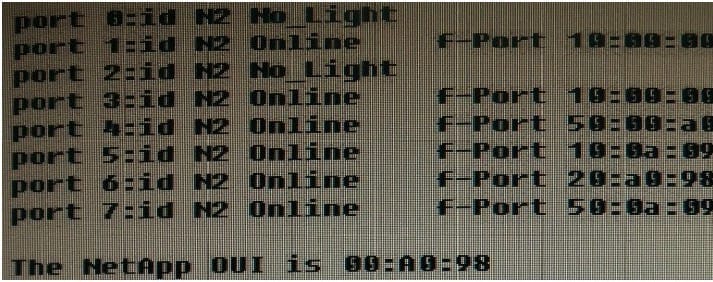
Which port has a NetApp device attached to it?
A. port 7
B. port 6
C. port 5
D. port 3
