HP2-Z33 Online Practice Questions and Answers
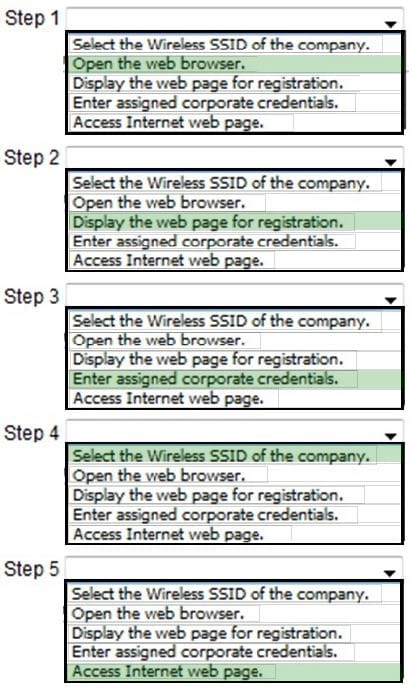
An employee wants to register an endpoint using wireless and the HP BYOD portal of a company with credentials of the corporate account. What is the correct order of steps to register the endpoint? (Place the steps in the correct order.)
Hot Area:
A research company wants to deploy a high throughput 802.11n only wireless network. The network administrator selects the "client dot11n-only" option. Which other configuration option must the network administrator configure?
A. maximum MCS index
B. basic rate 6Mb/s
C. mandatory rates MCS0-MCS15
D. MCS15 data rate
Where can a network administrator check for successful authentication in User Access Manager?
A. User Access Log > Auth Failure Log
B. User Access > LDAP Users
C. User Access Log > Access Details
D. User Access > Access Device Log
An organization's security policy mandates the use of 802.1X port based authentication. The organization's security policy also mandates that before an employee's personal device can connect to the wireless network, it must download anti-virus, security patch, and other essential software. What should be configured on the access point to support these requirements?
A. EAP-TLS
B. dynamic WEP
C. portal authentication
D. 802.1X guest VLAN
An administrator wants to configure authentication on the HP 830 switch ports that connect to wireless access points. The company policy requires all wireless users to be authenticated using 802.1X authentication. Each port should also allow multiple wireless users to pass 802.1X authentication.
Which port security mode meets these requirements?
A. macAddressWithRadius
B. userLoginSecure
C. userLoginSecureExt
D. macAddressElseUserLoginSecureExt
Refer to the exhibit.
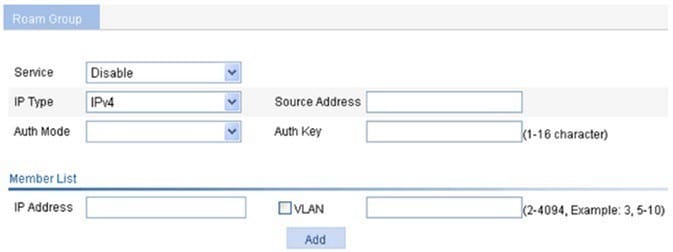
What does the Auth Mode enable?
A. sets the authentication mechanism(s) that must be used by clients if they wish to roam between access controllers
B. adds message integrity checks to messages sent between access controllers in the roaming group
C. ensures that all traffic between access controllers is encrypted
D. ensures access controllers are authenticated before they join the roaming group
Refer to the exhibit.
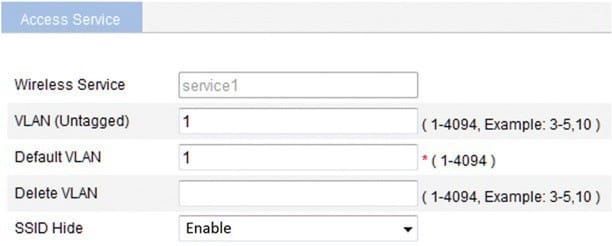
What is the primary advantage of enabling SSID Hide?
A. to connect to the access point without configuring clients
B. to make it easier for the client to connect to the access point
C. to prevent people from inadvertently connecting to the access point
D. to improve security
Which statement is correct about passwords when a network administrator synchronizes User Access Manager (UAM) with an Active Directory server?
A. Passwords are set but with a different salt value.
B. Passwords set in the Active Directory must be reset to different values when synchronized with UAM.
C. Passwords are stored in clear text in UAM.
D. Passwords are checked against the Active Directory during authentication.
A network administrator sets up the DHCP relay on an HP Comware Layer 3 device that forwards IP traffic between the VLANs associated with the wireless SSID with these commands.
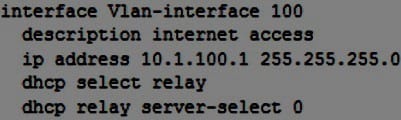
What must the administrator configure prior to enabling the DHCP relay to the DHCP server on 10.0.0.200 in the interface vlan-interface 100?
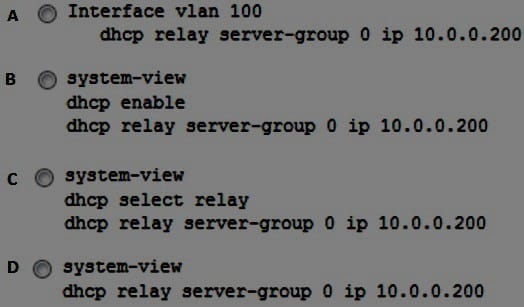
A. Option A
B. Option B
C. Option C
D. Option D
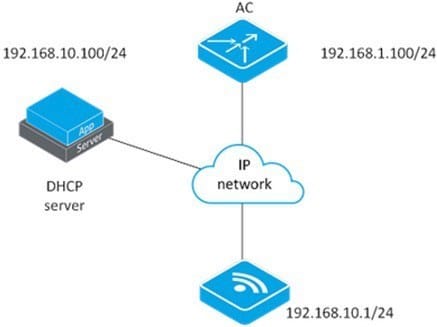
Refer to the exhibit.
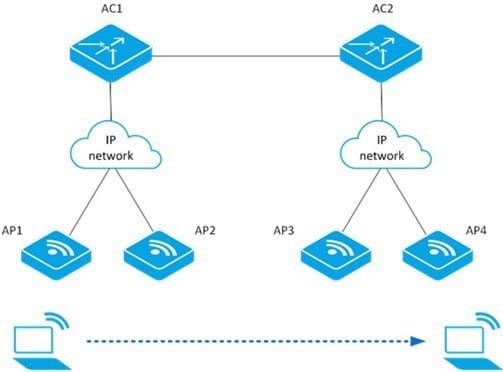
A client can roam successfully between AP1 and AP2. However, the client is unable to roam between AP2 and AP3. What could be the problem?
A. The client is not using RSN+802.1X authentication mode.
B. The AP2 and AP3 are not in the same mobility group.
C. The network is using IPv6.
D. The IACTP service has been disabled on AC1.
Refer to the exhibit.

A company wants to connect a mid-size branch office to their corporate location. An HP 10500/7500 Unified Wired-Wireless module is deployed at the corporate location. A maximum of six HP MSM access points will be deployed at the branch location.
Which HP device meets these customer requirements and is the most cost effective solution for the branch location?
A. HP 830
B. HP 870
C. HP 2920
D. HP 7500
Which command allows an administrator to access the HP 830 switch CLI from the controller?
A. oap management-ip 192.168.0.101 module 1
B. oap connect slot 0
C. oap management-ip 192.168.0.101 slot 1
D. oap connect module 0
How can a network administrator set up User Manager (UAM) redundancy?
A. By installing a UAM server with two wireless controllers
B. By setting an Active and a Standby server sharing a common IP address
C. By setting an Active and Standby server sharing common storage
D. By installing two servers in a cluster where each is defined with a separate IP address and a shared virtual IP
A network administrator is setting up a wireless network secured by 802.1X authentication in EAP mode with an HP BYOD solution. What is an important concept to remember when configuring a Windows laptop to access the wireless network?
A. Root certificates from a Certificate Authority are not needed. The laptop will validate the RADIUS certificate using its client certificate.
B. Do not validate any certificates sent by the RADIUS server. This may cause security issues.
C. User Access Manager can self-generate its own certificate, and this kind of certificate does not need any validation.
D. To automatically validate a certificate sent by User Access Manager (UAM), a client must have a root certificate from the Certificate Authority that issued the UAM certificate
Refer to the exhibit.
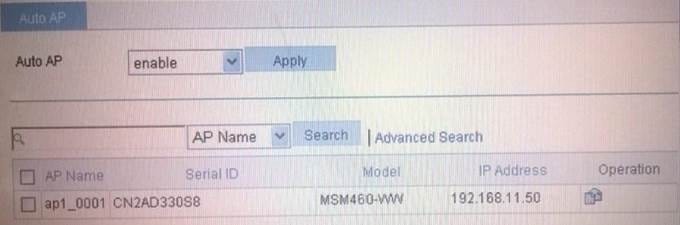
Based on the access controller configuration shown in the exhibit, when can newly discovered access points (AP) join this AC?
A. An AP can automatically join if the controller recognizes the AP serial number
B. An AP can automatically join if the controller recognizes the AP IP subnet address
C. An AP can automatically join if the controller recognizes the AP name
D. An AP can automatically join if the controller recognizes the AP model type