HP2-T16 Online Practice Questions and Answers
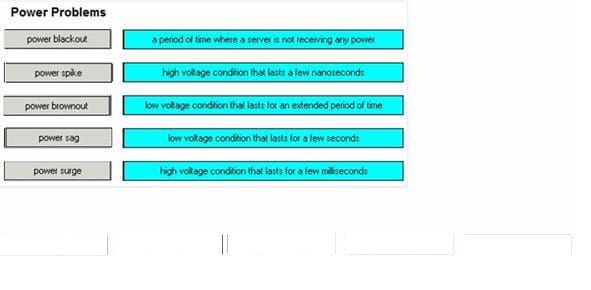
Match each power problem with its description.
Select and Place:
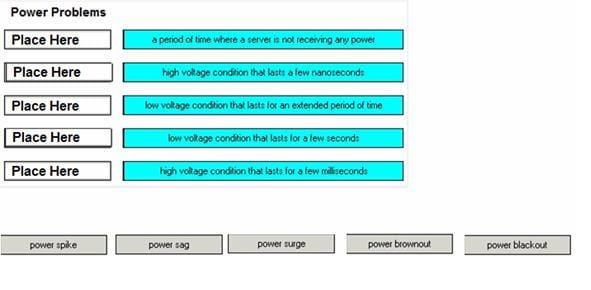
Select and Place:
What must you check prior to adding another processor to an existing system. (Select three)
A. amount of memory in the system
B. compatibility of the new process with existing processors
C. firmware requirements for the new processor
D. number of users currently logged into the system
E. number of processors the operating system supports
F. weight of the new processor
What are two types of backbone SAN topologies? (Select two)
A. fat tree
B. meshed
C. skinny tree
D. cascaded
E. ring
What should a successful Disaster Recovery Plan contain? (Selecte three)
A. offsite media storage location
B. regular bakcup rotation
C. proven restore process
D. cost-effective tape formats
E. change management procedures
F. effective performance alternatives
A customer has a single-threaded application running on a dual-core base ProLiant server. Processor utilization is consistently between 80 - 100%. Which step should you take to reduce system load on the processors?
A. Replace with slower quad-core processors.
B. Replace with faster single core processors.
C. Change the application to use a single thread.
D. Add more memory.
Which tool does Windows provide to monitor and trend system performance?
A. Component Service
B. Windows Analyzer
C. Service Manager
D. System Monitor
Which Linux utility helps you obtain information about I/O and processor statistics?
A. iostat
B. ioutil
C. vmstat
D. cpuinfo
Which Linux utility allows you to configure a NIC card?
A. netstat
B. ifconfig
C. sar
D. ipconfig
How does single-mode fiber compare with multimode fiber?
A. Single mode fiber has a higher bandwidth and lower loss.
B. Multimode fiber has a higher bandwidth and lower loss.
C. Multimode fiber is more often used for long-distance telecommunications.
D. Single-mode fiber has higher loss and lower bandwidth.
Which Network Operating System (NOS) security practices are commonly used when planning server management? (Select three)
A. disable FTP and SSH
B. install hardware and software firewalls
C. disable unused TCP/IP service ports
D. use easy to remember password
E. enforce regular password changes
What factors are important to sustain the I/O rates of the application within an array? (Select two)
A. capacity of the disks within the array
B. speed of the disks within the array
C. number of disks within the array
D. location of the disks within an enclosure
What devices off the highest and most sophisticated level of security when restricting access to a server rom? (Select two)
A. retinal scanner
B. proximity card reader
C. mechanical lock
D. fingerprint scanner
E. reinforced steel door
F. bulletproof window
When should a performance baseline be captured?
A. after updating the server ROM
B. during the peak server usage
C. after any hardware or software additions to the system
D. after replacing a failed component
What is the most efficient way to use external DVD-ROM for ten servers in one rack?
A. Use seperate USB DVD-ROMs for each server.
B. Connect servers to the KVM switch with attached DVD-ROM.
C. Use one DVD-ROM and connect to a single server when needed.
D. Connect servers to a SAN switch with attached DVD-ROM.
What happens during a copy backup? (Select two)
A. The archive bit is set to 1.
B. The archive bit is left alone.
C. The archive bit is reset to 0.
D. The transaction log is cleared.
E. The transaction log is left alone.