GSEC Online Practice Questions and Answers
Your system has been infected by malware. Upon investigation, you discover that the malware propagated primarily via email. The malware attacked known vulnerabilities for which patches are available, but due to problems with your configuration management system you have no way to know which systems have been patched and which haven't, slowing your progress in patching your network. Of the following, which solution would you use to protect against this propagation vector?
A. Encrypt the emails on the server
B. Scan and block suspect email attachments at the email server
C. Install a firewall between the email server and the Internet
D. Separate the email server from the trusted portions of the network
When are Group Policy Objects (GPOs) NOT applied automatically to workstations?
A. At 90-minute intervals
B. At logon
C. Every time Windows Explorer is launched
D. At boot-up
What advantage would an attacker have in attacking a web server using the SSL protocol?
A. The web server trusts the client because they are using the same secret key.
B. The attacker needs to generate just one encryption key for all his requests.
C. The Client can cause the ssl web server to use a weak encryption algorithm.
D. The encrypted session makes It harder for an Intrusion Detection System to detect.
What improvement could a company that is rated at a NIST Implementation Tier of 2:
Risk Informed do to Increase their rating to a Tier 3: Repeatable?
A. Establish risk management processes as organization-wide policy
B. Increase awareness of cybersecurity risk at the organizational level
C. Formalize organizational risk management processes
D. Focus on internal participation in security programs and risk management
When considering ingress filtering, why should all inbound packets be dropped if they contain a source address from within the protected network address space?
A. The packets are probably corrupted.
B. The packets may have been accidentally routed onto the Internet.
C. The packets may be deliberately spoofed by an attacker.
D. The packets are a sign of excess fragmentation.
E. A and B
F. B and C
G. B and D
H. A and D
Which of the following is more commonly used for establishing high-speed backbones that interconnect smaller networks and can carry signals over significant distances?
A. Bluetooth
B. Ethernet
C. Token ring
D. Asynchronous Transfer Mode (ATM)
Jonny Is an IT Project Manager. He cannot access the folder called "IT Projects" but can access a folder called "Sales Data" even though he's not on the sales team. Which information security principle has failed?
A. Authentication
B. Authorization
C. Identification
D. Accountability
What is the process of simultaneously installing an operating system and a Service Pack called?
A. Synchronous Update
B. Slipstreaming
C. Simultaneous Update
D. Synchronizing
Based on the iptables output below, which type of endpoint security protection has host 192.168.1.17 implemented for incoming traffic on TCP port 22 (SSH) and TCP port 23 (telnet)?
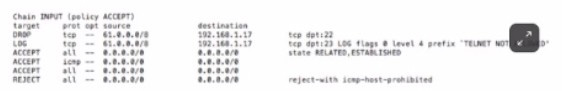
A. Operating System Control Firewall
B. Application Control Firewall
C. Exclusive Logging Analysis
D. Packet Filtering Firewall
E. Application Execution Control
Which of the following files contains the shadowed password entries in Linux?
A. /etc/passwd
B. /etc/shadow
C. /etc/profile
D. /etc/shdpwd
The following three steps belong to the chain of custody for federal rules of evidence. What additional step is recommended between steps 2 and 3?
STEP 1 - Take notes: who, what, where, when and record serial numbers of machine(s) in question.
STEP 2 - Do a binary backup if data is being collected.
STEP 3 - Deliver collected evidence to law enforcement officials.
A. Rebuild the original hard drive from scratch, and sign and seal the good backup in a plastic bag.
B. Conduct a forensic analysis of all evidence collected BEFORE starting the chain of custody.
C. Take photographs of all persons who have had access to the computer.
D. Check the backup integrity using a checksum utility like MD5, and sign and seal each piece of collected evidence in a plastic bag.
When an IIS filename extension is mapped, what does this mean?
A. Files with the mapped extensions cannot be interpreted by the web server.
B. The file and all the data from the browser's request are handed off to the mapped interpreter.
C. The files with the mapped extensions are interpreted by CMD.EXE.
D. The files with the mapped extensions are interpreted by the web browser.
When no anomaly is present in an Intrusion Detection, but an alarm is generated, the response is known as:
A. False negative
B. False positive
C. True positive
D. True negative
Which of the following tools is used to configure, control, and query the TCP/IP network interface parameters?
A. NSLOOKUP
B. IPCONFIG
C. ARP
D. IFCONFIG
What cryptographic technique does file Integrity monitoring employ?
A. Public-key cryptography
B. One-way hashes
C. Elliptical curve algorithms
D. Shared key cryptography
