312-50V7 Online Practice Questions and Answers
In Trojan terminology, what is a covert channel?
A. A channel that transfers information within a computer system or network in a way that violates the security policy
B. A legitimate communication path within a computer system or network for transfer of data
C. It is a kernel operation that hides boot processes and services to mask detection
D. It is Reverse tunneling technique that uses HTTPS protocol instead of HTTP protocol to establish connections
Which method can provide a better return on IT security investment and provide a thorough and comprehensive assessment of organizational security covering policy, procedure design, and implementation?
A. Penetration testing
B. Social engineering
C. Vulnerability scanning
D. Access control list reviews
A security administrator notices that the log file of the company`s webserver contains suspicious entries:
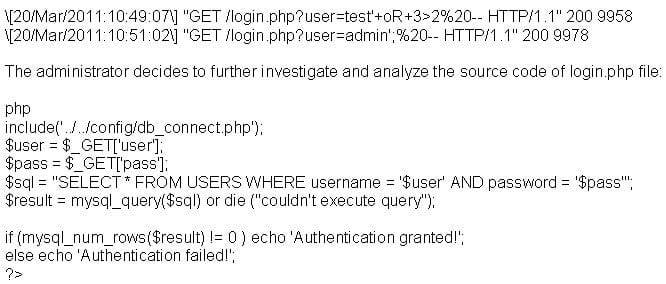
Based on source code analysis, the analyst concludes that the login.php script is vulnerable to
A. command injection.
B. SQL injection.
C. directory traversal.
D. LDAP injection.
Which of the following items is unique to the N-tier architecture method of designing software applications?
A. Application layers can be separated, allowing each layer to be upgraded independently from other layers.
B. It is compatible with various databases including Access, Oracle, and SQL.
C. Data security is tied into each layer and must be updated for all layers when any upgrade is performed.
D. Application layers can be written in C, ASP.NET, or Delphi without any performance loss.
What is the best defense against privilege escalation vulnerability?
A. Patch systems regularly and upgrade interactive login privileges at the system administrator level.
B. Run administrator and applications on least privileges and use a content registry for tracking.
C. Run services with least privileged accounts and implement multi-factor authentication and authorization.
D. Review user roles and administrator privileges for maximum utilization of automation services.
When analyzing the IDS logs, the system administrator notices connections from outside of the LAN have been sending packets where the Source IP address and Destination IP address are the same. There have been no alerts sent via email or logged in the IDS. Which type of an alert is this?
A. False positive
B. False negative
C. True positive
D. True negative
A hacker is attempting to see which IP addresses are currently active on a network. Which NMAP switch would the hacker use?
A. -sO
B. -sP
C. -sS
D. -sU
At a Windows Server command prompt, which command could be used to list the running services?
A. Sc query type= running
B. Sc query \\servername
C. Sc query
D. Sc config
