2V0-41.23 Online Practice Questions and Answers
Which of the two following characteristics about NAT64 are true? (Choose two.)
A. NAT64 is stateless and requires gateways to be deployed in active-standby mode.
B. NAT64 is supported on Tier-1 gateways only.
C. NAT64 is supported on Tier-0 and Tier-1 gateways.
D. NAT64 requires the Tier-1 gateway to be configured in active-standby mode.
E. NAT64 requires the Tier-1 gateway to be configured in active-active mode.
What are three NSX Manager roles? (Choose three.)
A. master
B. cloud
C. zookeepet
D. manager
E. policy
F. controller
How does the Traceflow tool identify issues in a network?
A. Compares the management plane configuration states containing control plane traffic and error reporting from transport node agents.
B. Compares intended network state in the control plane with Tunnel End Point (TEP) keepalives in the data plane.
C. Injects ICMP traffic into the data plane and observes the results in the control plane.
D. Injects synthetic traffic into the data plane and observes the results in the control plane.
What are two valid options when configuring the scope of a distributed firewall rule? (Choose two.)
A. DFW
B. Tier-1 Gateway
C. Segment
D. Segment Port
E. Group
Which VPN type must be configured before enabling a L2VPN?
A. Route-based IPSec VPN
B. Policy based IPSec VPN
C. SSL-bosed IPSec VPN
D. Port-based IPSec VPN
What are two valid BGP Attributes that can be used to influence the route path traffic will take? (Choose two.)
A. AS-Path Prepend
B. BFD
C. Cost
D. MED
An NSX administrator is creating a Tier-1 Gateway configured In Active-Standby High Availability Mode. In the event of node failure, the failover policy should not allow the original tailed node to become the Active node upon recovery.
Which failover policy meets this requirement?
A. Non-Preemptive
B. Preemptive
C. Enable Preemptive
D. Disable Preemptive
Which CLI command is used for packet capture on the ESXi Node?
A. tcpdump
B. debug
C. pktcap-uw
D. set capture
A customer has a network where BGP has been enabled and the BGP neighbor is configured on the Tier-0 Gateway. An NSX administrator used the get gateways command to retrieve this Information: Which two commands must be executed to check BGP neighbor status? (Choose two.)
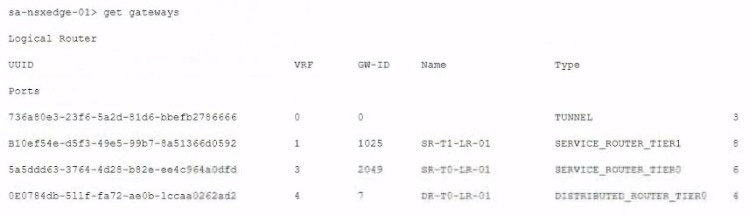
A. vrf 1
B. vrf 4
C. sa-nexedge-01(tier1_sr> get bgp neighbor
D. sa-nexedge-01(tier0_sr> get bgp neighbor
E. sa-nexedge-01(tier1_dr)> get bgp neighbor
F. vrf 3
Which three NSX Edge components are used for North-South Malware Prevention? (Choose three.)
A. Thin Agent
B. RAPID
C. Security Hub
D. IDS/IPS
E. Security Analyzer
F. Reputation Service
What needs to be configured on a Tler-0 Gateway lo make NSX Edge Services available to a VM on a VLAN-backed logical switch?
A. Downlink Interface
B. VLAN Uplink
C. Loopback Router Port
D. Service Interface
Which three security features are dependent on the NSX Application Platform? (Choose three.)
A. NSX Intelligence
B. NSX Firewall
C. NSX Network Detection and Response
D. NSX TLS Inspection
E. NSX Distributed IDS/IPS
F. NSX Malware Prevention
In which VPN type are the Virtual Tunnel interfaces (VTI) used?
A. Route and SSL based VPNs
B. Route-based VPN
C. Policy and Route based VPNs
D. SSL-based VPN
What are two supported host switch modes? (Choose two.)
A. DPDK Datapath
B. Enhanced Datapath
C. Overlay Datapath
D. Secure Datapath
E. Standard Datapath
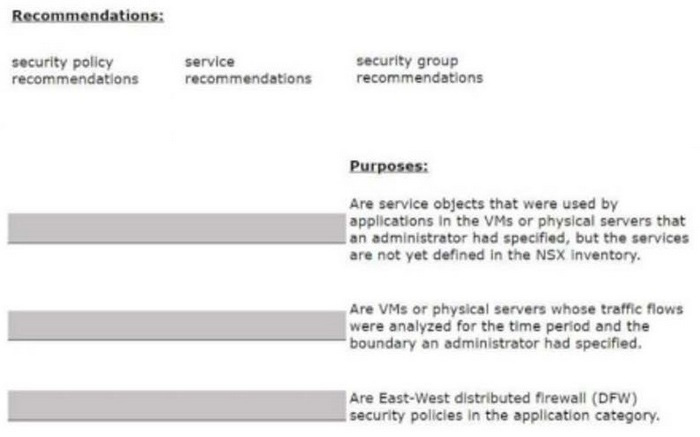
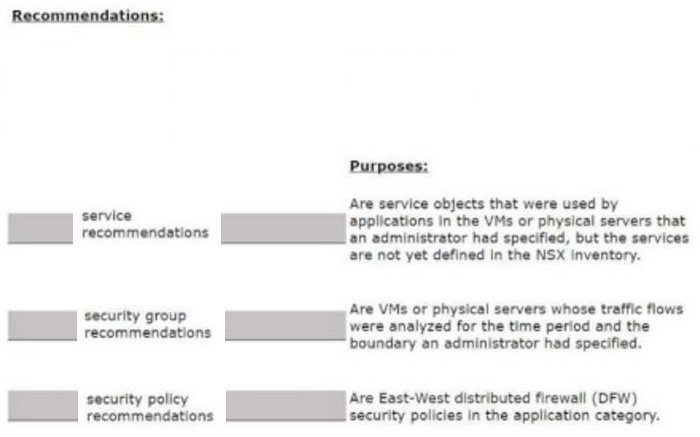
DRAG DROP
Match the NSX Intelligence recommendations with their correct purpose.
Select and Place: