201-01 Online Practice Questions and Answers
From Cascade Pilot, reports may include:
A. One or all views from the main workspace.
B. Notes entered associated with a view.
C. Analyst and Client information entered.
D. A and B.
E. A, B and C.
When Cascade Pilot is connected to Cascade Shark:
A. Cascade Shark interfaces and captures job traces appear under the devices tab within the sources panel.
B. Cascade Shark interfaces appear under the devices tab of the sources panel AND Cascade Shark capture job traces appear under the files tab of the sources panel.
C. Cascade Shark interfaces and captures job traces appear in the views panel.
D. Cascade Shark interfaces must be selected from the home menu to begin a capture.
How does Cascade obtain information about Retransmissions in the network?
A. It obtains L2 retransmissions from switches and routers via SNMP.
B. It obtains TCP retransmissions by tracking TCP segments via the Sensor.
C. Both A and B.
D. Cascade does not track retransmissions.
E. Cascade obtains retransmissions from Netflow (retransmissions are sent as a flag as part of standard netflow).
User Interface Preferences give users the ability to: (Select 3)
A. change the Navigation Bar Position.
B. change were reports are saved on Profiler.
C. change data unit from Bytes to Bits.
D. change user Time Zone.
E. search for lost templates.
Which of the following devices could be the data source for Cascade Profiler? (Select 3)
A. Cascade gateway
B. Cascade Pilot software
C. Wireshark software
D. Cascade Sensor
E. Cascade Shark
How does Cascade performance analytics assist with Performance Monitoring?
A. By setting static thresholds for Application metrics and Interface metrics, tolerance can be determined. Cascade will use these thresholds and tolerances to report on deviations indicative of Performance problems.
B. The Customer only needs to identify their critical interfaces and applications, and Cascade will automatically baseline their behavior and report on deviations indicative of Performance problems.
C. The Performance Analytics are able to detect security threats such as host scans and worms.
D. After base-lining, Cascade can re-route congested traffic to avoid congested application delivery paths.
Using the Cascade Active Directory Connector, a Cascade Profiler will be able to see:
A. Attempted Logins only
B. Successful Logins only
C. Failed and Successful Logins
D. Administrator Logins only
Beginning with version 9.0.5 what is the maximum number of flows per minute that the Cascade Gateway can be licensed for?
A. 800,000
B. 1,000,000
C. 1,200,000
D. 1,400,000
E. 1,600,000
What is a benefit that Cascade might provide to Network Engineering? (Select 3)
A. Ability to view link usage over the last few months for capacity planning purposes.
B. Ability to consolidate and view all Steelhead and Router configurations across the network.
C. Ability to view applications and protocols used across the enterprise.
D. Ability to view WAN use by top hosts, top servers, top application, top ports, top protocols, and QOS markings.
What is one way Cascade can assist with Application Performance problems?
A. Cascade will send synthetic transactions to measure response time.
B. Cascade has a software agent that can be loaded on a Windows Server to provide response time metrics with most major applications
C. Cascade tracks Response Time metrics by observing live traffic. These metrics are used with other indicators to build baselines and analyze deviations that may be indicators to issues.
D. All the above.
What is an initiative with which Cascade can help? (Select 3)
A. WAN Optimization
B. Data Center Consolidation
C. Router Configuration Management
D. Firewall Audit
Packet de-duplication in Cascade Shark appliance applies to:
A. Packets across all the ports of an appliance.
B. Packets on a single physical capture port.
C. Packets on an aggregating capture port.
D. Packets across different Cascade Shark appliances.
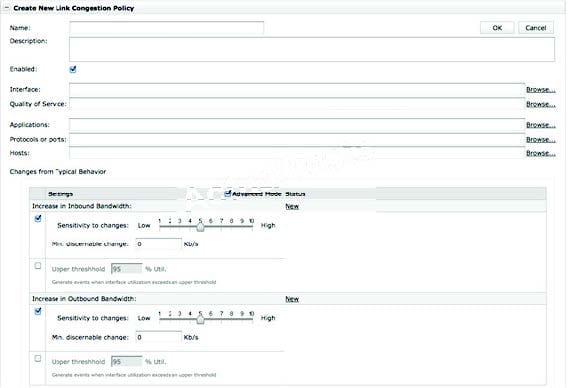
Refer to the exhibit.
From the Quick report in the Cascade Profiler GUI, which choice should be used if you want to create a report based on a subnet address (e.g. 192.168.1.0/24)?
A. Host/Group
B. IP Address/Subnet
C. Interface/Device
D. Network
Which component of Cascade can be used with a Cascade Express Profiler?
A. Standard or Enterprise Profiler
B. Gateways
C. Sensor
D. Shark
E. Sensor-VE
F. All of the above
Some common protocols, which may be observed on a network with visibility tools, include:
A. HTTP over TCP/80 and HTTPS over TCP/445
B. HTTP over TCP/80 and HTTPS over TCP/443
C. HTTP over TCP/443 and HTTPS over TCP/80
D. HTTP over TCP/445 and HTTPS over TCP/80
E. HTTP over TCP/88 and HTTP over TCP/444
