1Z0-997-20 Online Practice Questions and Answers
You are working with a social media company as a solution architect. The media company wants to collect and analyze large amounts of data being generated from their websites and social media feeds to gain insights and continuously improve the user experience. In order to meet this requirement, you have developed a microservices application hosted on Oracle Container Engine for Kubernetes. The application will process the data and store the result to an Autonomous Data Warehouse (ADW) instance.
Which Oracle Cloud Infrastructure (OCI) service can you use to collect and process a large volume of unstructured data in real time?
A. OCI Events
B. OCI Streaming
C. OCI Resource Manager
D. OCI Notifications
You are building a highly available and fault tolerant web application deployment for your company. Similar application delayed by competitors experienced web site attack including DDoS which resulted in web server failing.
You have decided to use Oracle Web Application Firewall (WAF) to implement an architecture which will provide protection against such attacks and ensure additional configuration will you need to implement to make sure WAF is protecting my web application 24?.
Which additional configuration will you need to Implement to make sure WAF Is protecting my web application 24??
A. Configure auto scaling policy and it to WAF instance.
B. Configure Control Rules to send traffic to multiple web servers
C. Configure multiple origin servers
D. Configure new rules based on now vulnerabilities and mitigations
Your team is conducting a root analysis (RCA) following a recent, unplanned outage. One of the block volumes attached to your production WebLogic server was deleted and you have tasked with identifying the source of the action. You search the Audit logs and find several Delete actions that occurred in the previous 24 hours. Given the sample of this event.
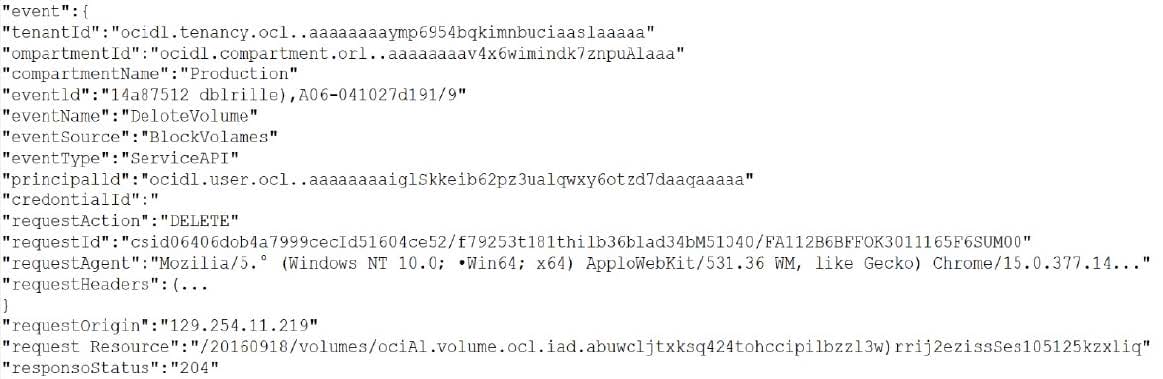
Which item from the event log helps you identify the individual or service that initiated the DeleteVolume API call?
A. requestAgent
B. eventource
C. principalld
D. requestOrigin
E. eventId
You are part of a project team working in the development environment created in Oracle Cloud Infrastructure (OCI). You realize that the CIDR block specified for one of the subnets in a Virtual Cloud Network (VCN) is not correct and want to delete the subnet. While deleting you get an error indicating that there are still resources that you must delete first. The error includes the OCID of the VNIC that is in the subnet.
Which of the following action you will take to troubleshoot this issue?
A. Use OCI CLI to call "network vnic" and "compute vnic-attachment" operations to find out the parent resource of the VNIC.
B. Use OCI CLI to delete the VNIC first and then delete the subnet.
C. Use OCI CLI to delete the subnet using -force option.
D. Copy and paste OCID of the VNIC in the search box of the OCI Console to find out the parent resource of the VNIC.
You are working for a Travel company and your travel portal application is a collection of microservices that run on Oracle Cloud Infrastructure Container Engine for Kubernetes. As per the recent security overview, you have noticed that Oracle has published a newer image of the Operating System used by the worker nodes. You want to make sure that your application doesn't face any downtime but at the same time the worker nodes gets upgraded to the latest version of the Operating System.
What should you do to get this upgrade done without application downtime? (Choose the best answer.)
A. 1. Shutdown the worker nodes 2. Create a new node pool 3. Manually schedule the pods on the newly built node pool
B. 1. Create a new node pool using the latest available Operating System image. 2. Run kubectl cordon
C. 1. Create a new node pool using the latest available Operating System image 2. Run kubectl taint nodes """"all node""role.kubernetes.io/master"" 3. Delete the old node pool
D. 1. Run kubectl cordon
A new international hacktivist group, based in London, launched wide scale cyber attacks including SQL Injection and Cross-Site Scripting (XSS) across multiple websites which are hosted in Oracle Cloud Infrastructure (OCI). As an IT consultant, you must configure a Web Application Firewall (WAF) to protect these websites against the attacks.
How should you configure your WAF to protect the website against those attacks? (Choose the best answer.)
A. Enable an Access Rule that contains XSS Filters Categories and SQL Filters Categories.
B. Enable a Protection Rule to block the attacks based on HTTP Headers that contain XSS and SQL strings.
C. Enable a Protection Rule that contains XSS Filters Categories and SQL Filters Categories.
D. Enable an Access Rule to block the IP Address range from London.
E. Enable a Protection Rule to block requests that came from London.
Your company has recently deployed a new web application that uses Oracle functions Your manager Instructed you to Implement major manage your systems more effectively. You know that Oracle functions automatically monitors functions on your behalf reports metrics through Service Metrics.
Which two metrics are collected and made available by this feature?
A. length of time a function runs
B. number of times a function is removed
C. number of times a function is invoked
D. amount of CPU used by a function
E. number of concurrent connections
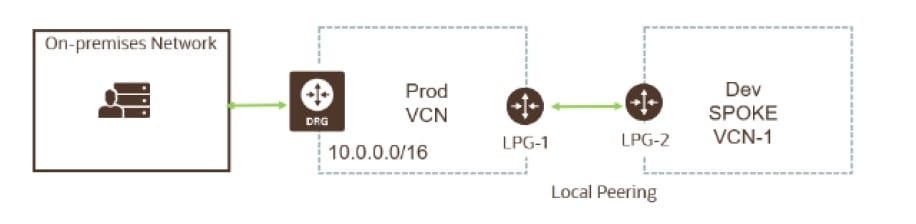
Your customer recently ordered for a 1-Gbps Fast Connect connection In ap-tokyo-1 region of Oracle Cloud Infrastructure (OCI). They will us this to one Virtual cloud Network (VCN) in their production (OC1) tenancy and VCN In their development OC1 tenancy
As a Solution Architect, how should yon configure and architect the connectivity between on premises and VCNs In OCI?
A. Create two private virtual circuits on the FastConnect link. Create two Dynamic Routing Gateways, one for each VCNs. Attach the virtual circuits to the dynamic routing gateways.
B. You cannot achieve connectivity using single FastConnect link as the production and the development VCNs-are in separate tenancies. Request one more FastConnect connection.
C. Create a single private virtual circuit over FastConnect and attach fastConnect to either of the VCN's Dynamic Routing Gateway. Use Remote Peering to peer production and development VCNs.
D. Create a hub-VCN that uses Dynamic Routing Gateway (DRG) to communicate with on- premises network over FastConnect. Connect the hub-VCN to the production VCN spoke and with development VCN spoke, each peered via their respective local Peering Gateway (LPG)