1Z0-1104-22 Online Practice Questions and Answers
Which volume type contains the image used to boot a compute instance?
A. Init 6 volume
B. Boot volume
C. Startup volume
D. Block volume
Which Oracle Cloud Service provides restricted accessto target resources?
A. Bastion
B. Internet Gateway
C. Load balancer
D. SSL certificate
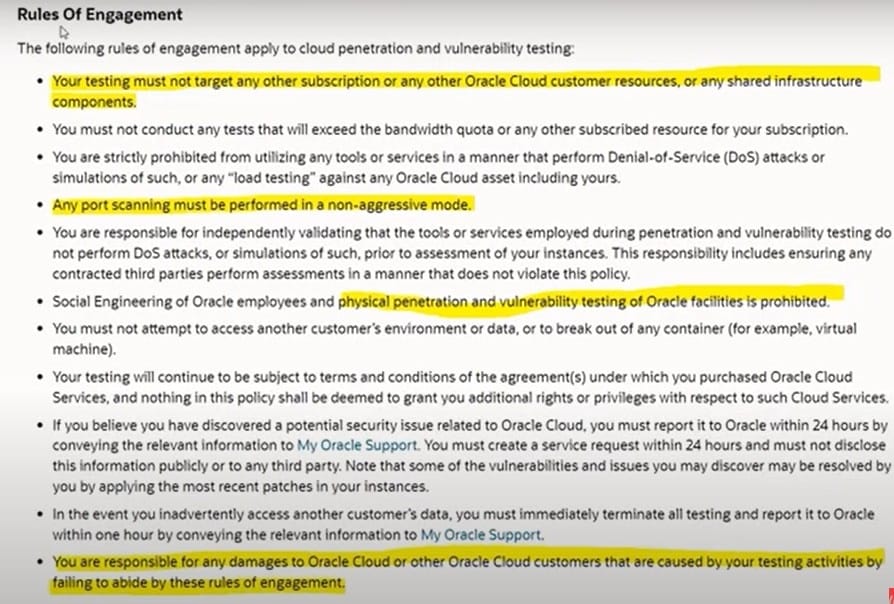
With regard to vulnerability and cloud penetration testing, which rules of engagement apply? Select TWO correct answers.
A. Any port scanning must be performed in an aggressive mode
B. Physical penetration and vulnerability testing of Oraclefacilities is prohibited
C. Testing should target any other subscription or any other Oracle Cloud customer resources
D. You are responsible for any damages to Oracle Cloud customers that are caused by your testing activities
Which type of file system does file storage use?
A. NFSv3
B. iSCSI
C. Paravirtualized
D. NVMe
E. SSD
Which VCNconfiguration is CORRECT with regard to VCN peering within a same region ?
A. 12.0.0.0/16 and 194.168.0.0/16
B. 12.0.0.0/16 and 12.0.0.0/16
C. 194.168.0.0/24 and 194.168.0.0/24
D. 194.168.0.0/24 and 194.168.0.0/16
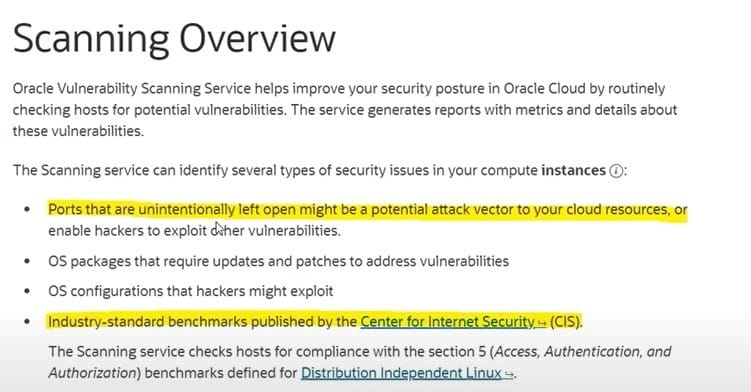
Which securityissues can be identified by Oracle Vulnerability Scanning Service? Select TWO correct answers
A. Distributed Denial of Service (DDoS)
B. Ports that are unintentionally left open can be a potential attack vector for cloud resources
C. SQL Injection
D. CISpublished Industry-standard benchmarks
Which OCI services can encrypt all data-at-rest ? Select TWO correct answers
A. File Storage
B. NAT Gateway
C. Block Volumes
D. Geolocation Steering
With regard to WAF in OCI, which of the following statements are NOT customer's responsibility? Select TWO answers.
A. Configure WAF policies for websites
B. WAF edge nodes with High Availability
C. Configure Bot Managementstrategies for a website traffic
D. Import latest OWASP Core Rule Sets
As a security administrator, you want to create cloud resources that alignwith Oracle's security principles and best practices. Which security service should you use?
A. Identity and Access Management
B. Cloud Guard
C. Security Advisor
D. Web Application Firewall (WAF)
Which statement is trueabout standards?
A. They may be audited.
B. They are result of a regulation or contractual requirement or an industry requirement.
C. They are methods and instructions on how to maintain or accomplish the directives of the policy.
D. They are the foundation of corporate governance.
Logical isolation for resources is provided by which OCI feature?
A. Tenancy
B. Availability Zone
C. Region
D. Compartments
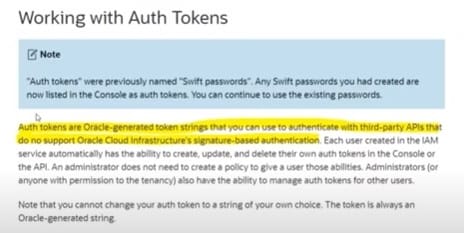
An e-commerce company needs to authenticate with third-party API that don't support OCI's signature-based authentication.
What can be the solution for the above scenario?
A. Security Token
B. API Key Authentication
C. Asymmetric keys
D. Auth Token/Swift Password
Which statement is true about using custom BYOI instances in Windows Servers that are managed by OS Management Service?
A. Windows Servers that does not have the minimum agent version does not require an agent update or installation.
B. Windows Servers that already has the minimum agent version does not require an agent update or installation.
C. Windows Servers that already has the minimum agent version requires an agent update or installation.
D. Windows Servers that does not have the minimum agent version requires an agent update or installation.
What is the use case for Oracle cloudinfrastructure logging analytics service?
A. monitors, aggregates, indexes and analyzes all log data from on-premises.
B. labels data packets that pass through the internet gateway
C. automatically create instances to collect logs analysis and send reports
D. automatically and manage any log based on a subscription model
What do the features of OS Management Service do?
A. Add complexity in using multiple tools tomanage mixed-OS environments.
B. Provide paid service and support to OCI subscribers for fixes on priority.
C. Increase security and reliability by regular bug fixes.
D. Encourage manual setup to avoid machine-induced errors.