1Z0-1072-21 Online Practice Questions and Answers
You have compartments C and D under the root compartment in your Oracle Cloud Infrastructure (OCI) tenancy; compartment C contains a sub-compartment also named D. You are trying to move this sub-compartment D to the parent compartment D like shown in the picture, but the move fails.
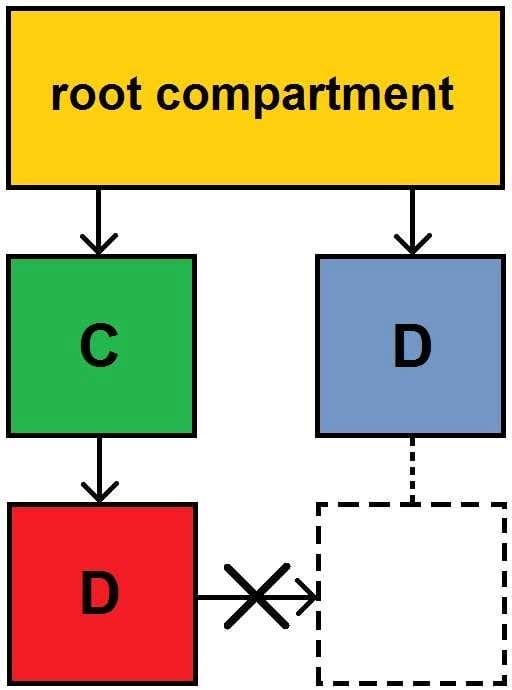
What is the reason for this error?
A. You need to move all the compartments in the hierarchy to the new parent compartment.
B. You cannot move a subcompartment to another parent compartment.
C. Both parent and child compartments cannot have the same name.
D. Sub-compartment D needs to be empty before it can be moved.
Which two configuration formats does Terraform support? (Choose two.)
A. YAML
B. JSON
C. HCL
D. XML
Your application front end consists of several Oracle Cloud Infrastructure compute instances behind a public load balancer. You have configured the load balancer to perform health checks on these instances. What will happen if an instance fails to pass the configured health checks?
A. The instance is replaced automatically by the load balancer.
B. The instance is terminated automatically by the load balancer.
C. The instance is taken out of the back end set by the load balancer.
D. The load balancer stops sending traffic to that instance.
You have one database-style application that frequently makes many random reads and writes across the
dataset.
Which storage offering supports this application?
A. Object Storage Service
B. Archive Storage Service
C. File Storage Service
D. Block Storage Service
Which tool can automatically install Oracle Cloud Infrastructure CLI?
A. Python
B. RPM
C. APT
D. PIP
What does Terraform use to create, manage, and manipulate infrastructure resources?
A. resources
B. provisioner
C. instances
D. provider
Which three methods can you use to manage Oracle Cloud Infrastructure services? (Choose three.)
A. Oracle Cloud Infrastructure Desktop Client
B. Oracle Cloud Infrastructure Console
C. SSH or RDP
D. Command-line Interface
E. REST API
What is a valid option when exporting a custom image?
A. object storage URL
B. archive storage URL
C. file storage service
D. block volume
Which two statements are true about restoring a block volume from a manual or policy-based block volume backup? (Choose two.)
A. It can be restored as new volumes with different sizes from the backups
B. It can be restored as a new volume to any AD across different regions
C. It must be restored as a new volume to the same availability domain (AD) on which the original block volume backup resides
D. It can be restored as a new volume to any AD in the same region
Which two are a valid image source when launching a new compute instance? (Choose two.)
A. bare metal instance
B. object storage
C. custom image
D. boot volume
You have five different company locations spread across the US. For a proof-of-concept (POC) you need
to setup secure and encrypted connectivity to your workloads running in a single virtual cloud network
(VCN) in the Oracle Cloud Infrastructure Ashburn region from all company locations.
What would meet this requirement?
A. Create five internet gateways in your VCN and have separate route table for each internet gateway.
B. Create five virtual circuits using FastConnect for each company location and terminate those connections on a single dynamic routing gateway (DRG). Attach that DRG to your VCN.
C. Create five IPsec connections with each company location and terminate those connections on a single DRG. Attach that DRG to your VCN.
D. Create five IPsec VPN connections with each company location and terminate those connections on five separate DRGs. Attach those DRGs to your VCN.
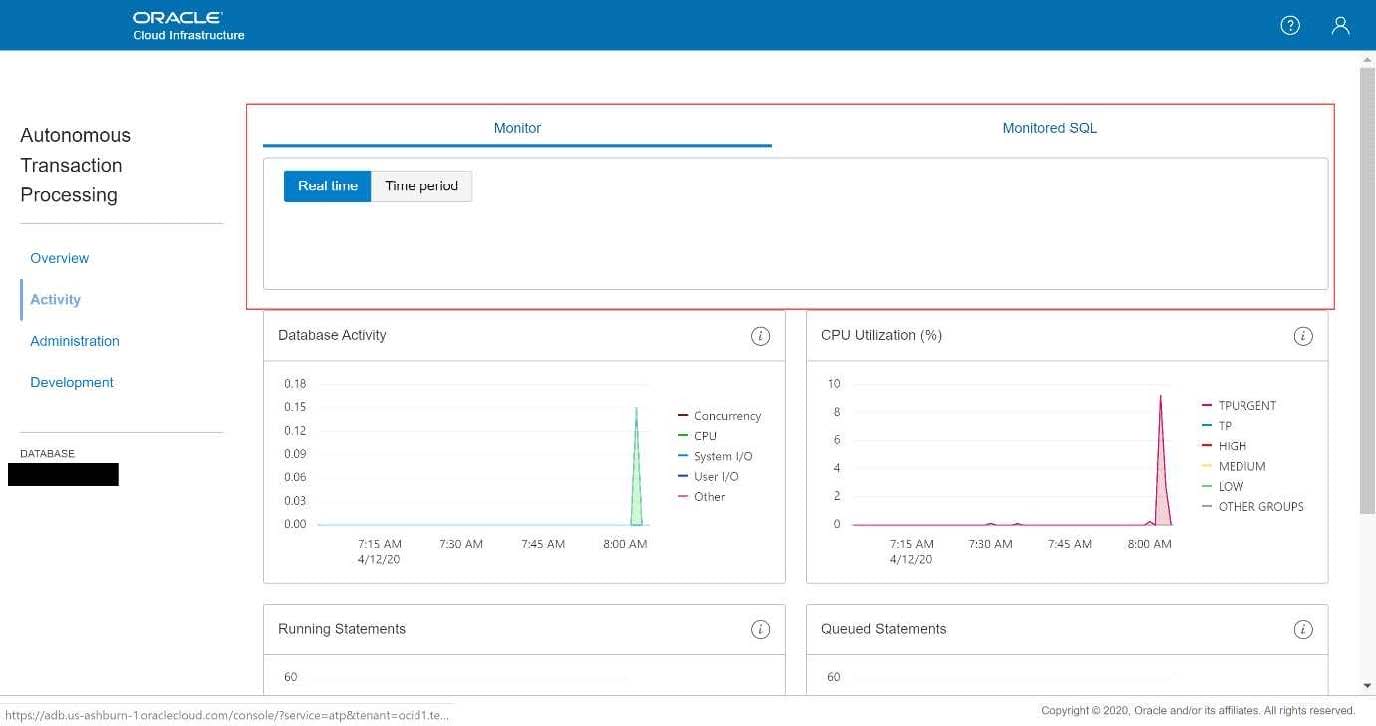
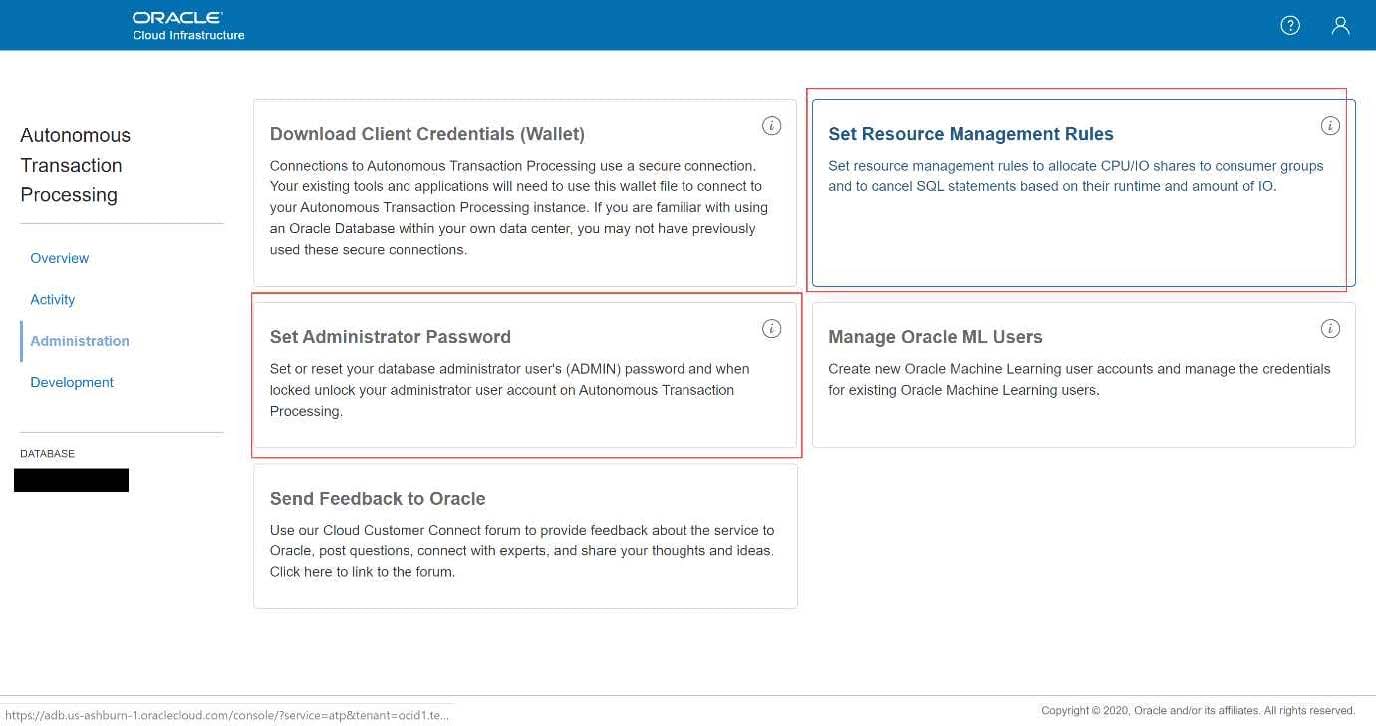
You have provisioned an Autonomous Transaction Processing (ATP) database and logged into the ATP
service console.
What are three abilities that can be performed from this service console? (Choose three.)
A. scale up/down the CPUs
B. create ATP database users
C. reset the admin password
D. set resource management rules
E. monitor database activity and SQL queries
Your application consists of three Oracle Cloud Infrastructure compute instances running behind a public load balancer. You have configured the load balancer to perform health checks on these instances, but one of the three instances fails to pass the configured health check. Which of the following action will the load balancer perform?
A. Stop sending traffic to the instance that failed health check
B. Terminate the instance that failed health check
C. Stop the instances that failed health check
D. Remove the instance that failed the health check from the backend set
Your IT department wants to cut down storage costs, but also meet compliance requirements as set up by the central audit group. You have a legacy bucket with both Word does (*.docx) and Excel files (*.xlsx). Your auditors want to retain only Excel files for compliance purposes. Your IT departments wants to keep all other files for 365 days only. What two steps can you take to meet this requirement?
A. Create Object Storage Lifecycle rules to archive objects from the legacy bucket after 365 days without any pattern matching
B. Create Object Storage Lifecycle rules to delete objects from the legacy bucket after 365 days with a filter type - include by pattern: ''.docx
C. It is not possible to meet this requirement
D. Create Object Storage Lifecycle rules to delete objects from the legacy bucket after 365 days with a filter type - exclude by pattern: ''.xlsx"
E. Create Object Storage Lifecycle rules to delete objects from the legacy bucket after 365 days without any pattern matching
You have two NFS clients running in two different subnets within the same Oracle Cloud Infrastructure (OCI) Virtual Cloud Network (VCN). You have created a shared file system for the two NFS clients who want to connect to the same file system, but you want to restrict one of the clients to have READ access while the other has READ/Write access. Which OCr feature would you leverage to meet this requirement?
A. Use VCN security rules to control access for the NFS clients
B. Use OCI Identity Access Management to control access for the NFS clients
C. Use File Storage NFS Export Options to control access for the NFS clients
D. Use NFS security to control access for the NES clients