1V0-81.20 Online Practice Questions and Answers
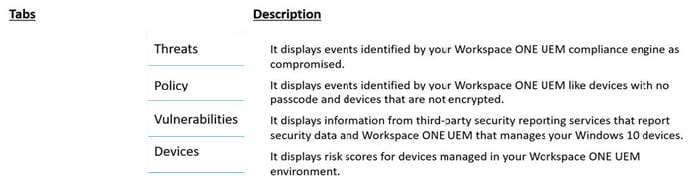
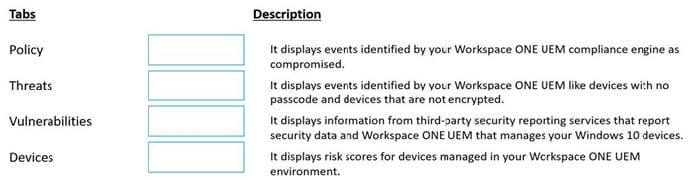
DRAG DROP
Match each Workspace ONE Intelligence Security Risk Module tab on the left with its description on the right by dragging the tab's name into the correct box.
Select and Place:
Which VMware product allows you to query an endpoint like a database?
A. VMware NSX-T Data Center
B. VMware Carbon Black Audit and Remediation
C. VMware Workspace ONE UEM
D. VMware Carbon Black Endpoint Standard
Which three default connectors are available in Workspace ONE Intelligence to execute automation actions? (Choose three.)
A. ServiceNow
B. vRealize Operations Manager
C. Slack
D. Log Insight
E. Workspace ONE UEM
Which is a common solution to implement for inbound network attacks?
A. Load Balancer
B. Firewall
C. Proxy
D. Reverse Proxy
A technician has been asked to confirm a specific browser extension does not exist on any endpoint in their environment. Which is the VMware Carbon Black tool to use for this task?
A. Enterprise EDR
B. EDR
C. Audit and Remediation
D. Endpoint Standard
Which three are key features of VMware Carbon Black Cloud Enterprise EDR? (Choose three.)
A. self-service security remediation
B. continuous and centralized recording
C. attack chain visualization and search
D. live response for remote remediation
E. frequent Antivirus pattern updates
When considering the Device Details page in Workspace ONE UEM, what three sub menus can you check for changes in compliance? (Choose three.)
A. Profiles
B. Troubleshooting
C. Updates
D. Status History
E. Compliance
Micro segmentation is under which pillar of trust in VMware's 5 pillars of Zero Trust?
A. User
B. Session/Transport
C. Application
D. Device
Which two choices are advantages for using baselines in Workspace ONE UEM? (Choose two.)
A. ability to apply a network security standard to a device
B. ability to use industry standard settings to a device
C. ability to apply drive updates to a device
D. ability to apply Windows Update patches to a device
E. ability to audit network security compliance to a device
What is the term used to describe a type of social engineering attack aimed at a specific person or specific type of person?
A. Phishing
B. Whaling
C. Tailgating
D. Spear Phishing
In VMware Carbon Black Cloud Endpoint Standard, which items are available in the Event view?
A. Hashes, Reputations
B. Emails, Policies, OS, Locations
C. Connection, IP/Port
D. IDs, Indicators/TTPs
Which VMware application enrolls an endpoint into Workspace ONE?
A. Workspace ONE Web
B. CB Defense Sensor
C. VMware Horizon Client
D. Workspace ONE Intelligent Hub
Least Privilege is a common method for minimizing the risk of what kind of threat?
A. Insider Threats
B. Spear Phishing
C. Distributed Denial of Service
D. Man in the Middle
In a Workspace ONE deployment, Per App Tunnel uses the Native Platform API for which platforms?
A. iOS and Android only
B. iOS, Android, MacOS and Windows
C. iOS and MacOS only
D. Android and Windows only
When filtering firewall rules after selecting an object to filter by, which four columns does the filter search? (Choose four.)
A. Services
B. Action
C. Protocol
D. Log
E. Applied To
F. Source
G. Destinations