1Z0-820 Online Practice Questions and Answers
Which modification needs to be made to the Service Management Facility before you publish a new package to the IPS repository?
A. The pkg.depotd must be disabled.
B. The pkg/readonly property for the application/pkg/server service must be set to false
C. The pkg/writable_root property for the application/pkg/server service must be set to true.
D. The pkg/image_root property for the application/pkg/server service must be set to the location of the repository.
The current ZFS configuration on serverA is: Pool1 c3t2d0 c3t3d0 Pool2 c3t4d0 c3t5d0 The ZFS configuration on serverB is:
Pool1 mirror-0 c3t2d0 c3t3d0 mirror-1 c3t4d0 c3t5d0 You need to change serverA's ZFS configuration to match serverB's configuration. Which option should you choose to modify the configuration on serverA so that it matches serverB's
configuration?
A. zpool destroy pool2 zpool attach pool1 c3t4d0 ct3t5d0
B. zpool destroy pool2 zpool attach pool1 c3t2d0 c3t2d0 c3t4d0 c3t5d
C. zpool destroy pool2 zpool add pool1 c3t4d0 c3t5d0
D. zpool destroy pool2 zpool mirror pool1 pool2
E. zpool destroy pool2 zpool attach pool1 c3t2d0 c3t4d0 zpool attach pool1 c3t3d0 c3t5d0
F. zpool destroy pool1 zpool destroy pool2 zpool create pool1 mirror c3t2d0 c3t3d0 c3t4d0 c3t5d0
You upgraded your server to Oracle Solaris 11 and you imported zpool (pool1) that was created in Solaris
10. You need to create an encrypted ZFS file system in pool1, but first you need to make sure that your server supports ZFS encryption.
Which four statements are true for support of ZFS encryption?
A. The encrypted file system must have been created in Oracle Solaris11. To encrypt a ZFS file system from a previous version of Solaris, upgrade the zpool and create a new encrypted ZFS file system into the encrypted ZFS file system.
B. If you plan to create an encrypted file system in an existing zpool, the zpool must be upgraded to ZFS version 30.
C. ZFS encryption is integrated with the ZFS command set and no additional packages need to be installed.
D. ZFS encryption requires that the ZFS Dataset Encryption package be installed.
E. If you plan to create an encrypted file system in an existing zpool, the pool must be upgraded to ZFS version 21, minimum.
F. Encryption is supported at the pool or dataset (file system) level.
G. Encryption is supported at the pool level only for every file system in the pool will be encrypted.
H. You cannot create an encrypted file system in a zpool that was created prior to oracle Solaris11. Create a new zpool in Solaris11, create an encrypted ZFS file system in the new zpool, and move or copy the data from the existing file system into the new encrypted file system.
You are troubleshooting the failure of a computer to mount an NFS file system hosted by a server (hostname mars) in the local area network.
Select the three commands that will enable you to identify the problem.
A. ping - s mars
B. cat /etc/vfstab
C. cat /etc/dfs/dfstab
D. sharemgr show -v
E. showmount -e mars
F. rpcinfo -s mars | egrep `nfs|mountd'
The core dump configuration for your system is:
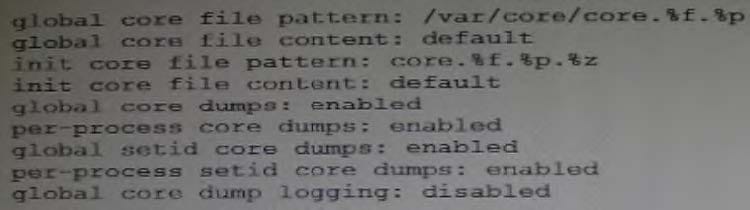
A user is running a process in the global zone and the process crashes. The process information is:
User1 2663 2618 0 17:46:42 pts/2 0:00 /usr/bin/bash
The server host name is: zeus
What will the per-process core file be named?
A. core.bash.2663.global
B. core.bash.2663.zeus
C. /var/core/core.bash.2663
D. /var/core/core.bash.2663.global
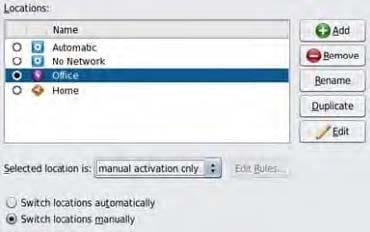
Select the two statements that correctly describe the operation of NWAM.
A. If a location is explicitly enabled, it remains active until explicitly changed.
B. Wireless security keys can be configured by using the nwammgr command.
C. NWAM stores profile information in /etc/ipadm/ipadm.conf and /etc/dladm/datalink.conf.
D. Multiple locations may be automatically activated in systems with multiple network interface cards.
E. Interface NCU Properties "float" and are automatically attached to the highest priority Link NCU Property.
F. If the DefaultFixed NCP is enabled, persistent configuration, stored in /etc/ipadm.conf and /etc/dladm/ datalink.conf is used.
View the Exhibit.
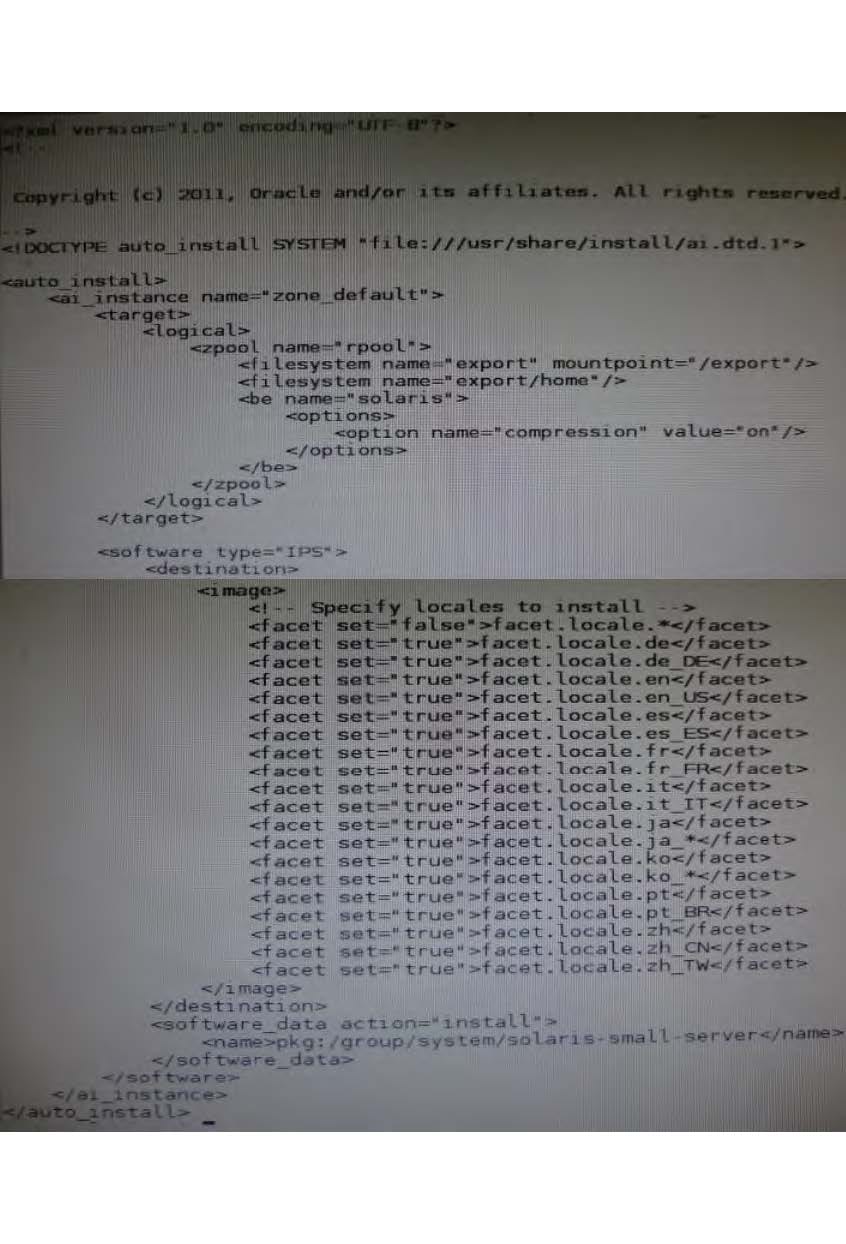
The file came from your Automated Installer (AI) install server. The file is ____________.
A. an AI SC profile for non-global zones
B. the default AI config file for non-global zones
C. the default AI manifest for non-global zones
D. a custom AI manifest
Review the zonestat command
zonestat -q -r physical-memory -R high -z dbzone -p -p "zones" 10 24h 60m
Select the option that correctly describes the information that is displayed by this command
A. It is a sample of dbzone's physical memory usage taken every hour over a 24-hour period Only the top 10 samplings of peak memory usage are displayed. All other utilization data is eliminated
B. It is a sample of dbzone's CPU, virtual memory, and networking utilization Physical memory is excluded from the report The sampling is taken every 10 minutes over a 24 hour period and peak utilization is displayed each hour.
C. ft is a sample of dbzone's CPU, virtual memory, and networking utilization Physical memory is excluded from the report. The sampling is taken every 10 seconds over a 24- hour period and displayed each hour.
D. It is a sample of dbzone's memory and CPU utilization every 10 seconds over a 24-hour period Only peak virtual memory usage and CPU utilization are displayed each hour All other utilization data is eliminated.
E. it is a sample of dbzone's physical memory usage taken every 10 seconds over a 24- hour period. Only peak memory usage is displayed each hour All other utilization data is eliminated.