1D0-571 Online Practice Questions and Answers
A distributed denial-of-service (DDOS) attack has occurred where both ICMP and TCP packets have crashed the company's Web server. Which of the following techniques will best help reduce the severity of this attack?
A. Filtering traffic at the firewall
B. Changing your ISP
C. Installing Apache Server rather than Microsoft IIS
D. Placing the database and the Web server on separate systems
Which of the following is considered to be the most secure default firewall policy, yet usually causes the most work from an administrative perspective?
A. Configuring the firewall to respond automatically to threats
B. Blocking all access by default, then allowing only necessary connections
C. Configuring the firewall to coordinate with the intrusion-detection system
D. Allowing all access by default, then blocking only suspect network connections
Which of the following is the most likely first step to enable a server to recover from a denial-of- service attack in which all hard disk data is lost?
A. Enable virtualization
B. Contact the backup service
C. Contact a disk recovery service
D. Rebuild your RAID 0 array
Which of the following standards is used for digital certificates?
A. DES
B. Diffie-Hellman
C. X.509
D. RC5
At the beginning of an IPsec session, which activity occurs during the Internet Key Exchange (IKE)?
A. Determining the number of security associations
B. Negotiating the authentication method
C. Determining the network identification number
D. Negotiating the version of IP to be used
A security breach has occurred in which a third party was able to obtain and misuse legitimate authentication information. After investigation, you determined that the specific cause for the breach was that end users have been placing their passwords underneath their keyboards. Which step will best help you resolve this problem?
A. Discipline specific end users as object lessons to the rest of the staff and reset passwords on all systems immediately.
B. Change all passwords on the company servers immediately and inform end users that their passwords will be changing on a regular basis.
C. Set passwords to expire at specific intervals and establish mandatory continual training sessions.
D. Inform end users that their passwords will be changing on a regular basis and require more complex passwords.
A new server has been placed on the network. You have been assigned to protect this server using a packet-filtering firewall. To comply with this request, you have enabled the following ruleset:
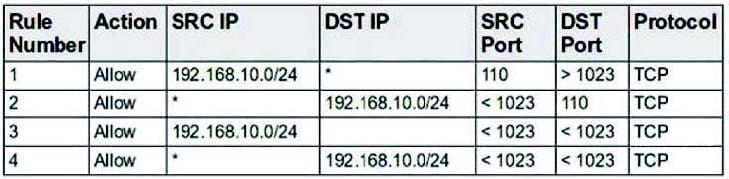
Which choice describes the next step to take now that this ruleset has been enabled?
A. From the internal network, use your Web browser to determine whether all internal users can access the Web server.
B. From the internal network, use your e-mail client to determine whether all internal users can access the e-mail server.
C. From the external network, use your Web browser to determine whether all external users can access the Web server.
D. From the external network, use your e-mail client to determine whether all external users can access the e-mail server.
What is the primary drawback of using symmetric-key encryption?
A. Key transport across a network
B. Speed of encryption
C. Denial-of-service attacks
D. Inability to support convergence traffic
You want to create a quick solution that allows you to obtain real-time login information for the administrative account on an LDAP server that you feel may become a target. Which of the following will accomplish this goal?
A. Reinstall the LDAP service on the server so that it is updated and more secure.
B. Install an application that creates checksums of the contents on the hard disk.
C. Create a login script for the administrative account that records logins to a separate server.
D. Create a dummy administrator account on the system so that a potential hacker is distracted from the
real login account.
The best way to thwart a dictionary attack is by enforcing a:
A. strong password policy.
B. restricted access policy.
C. firewall configuration policy.
D. proxy server policy.
Which of the following is the primary weakness of symmetric-key encryption?
A. Data encrypted using symmetric-key encryption is subject to corruption during transport.
B. Symmetric-key encryption operates slower than asymmetric-key encryption.
C. Symmetric-key encryption does not provide the service of data confidentiality.
D. Keys created using symmetric-key encryption are difficult to distribute securely.
Consider the following image of a packet capture: This packet capture has recorded two types of attacks. Which choice lists both attack types?
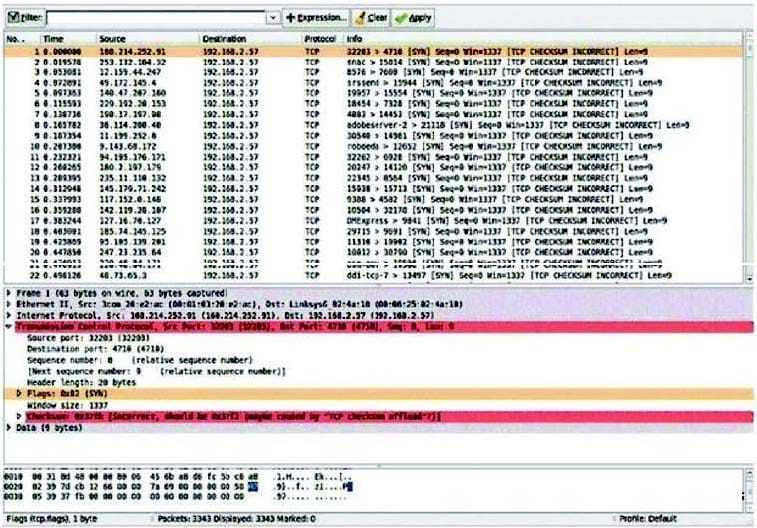
A. A dictionary attack and a worm-basedattackA.A dictionary attack and a worm-based attack
B. Asyn flood attack and a spoofing attackB.A syn flood attack and a spoofing attack
C. A worm attack and abotnet attack C.A worm attack and a botnet attack
D. A SQL injection attack and a virusattackD.A SQL injection attack and a virus attack
You have been assigned to provide security measures for your office's reception area. Although the company needs to provide security measures, costs must be kept to a minimum. Which of the following tools is the most appropriate choice?
A. Firewall
B. Intrusion-detection system
C. Camera
D. Security guard
Consider the following image of a packet capture:
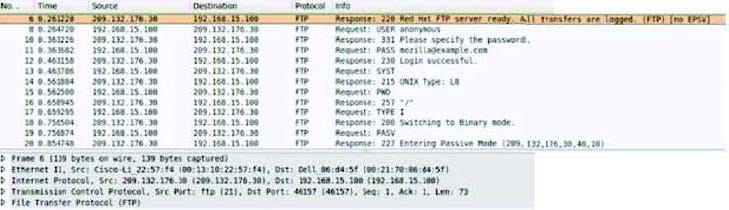

Which of the following best describes the protocol used, along with its primary benefit?
A. It is a passive FTP session, which is easier for firewalls to process.
B. It is an active FTP session, which is necessary in order to support IPv6.
C. It is an extended passive FTP session, which is necessary to support IPv6.
D. It is an active FTP session, which is supported by all FTP clients.
Consider the following diagram:
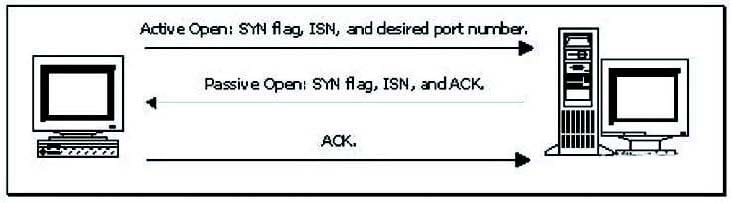
Which of the following best describes the protocol activity shown in the diagram, along with the most likely potential threat that accompanies this protocol?
A. The ICMP Time Exceeded message, with the threat of a denial-of-service attack
B. The SIP three-way handshake, with the threat of a buffer overflow
C. The TCP three-way handshake, with the threat of a man-in-the-middle attack
D. The DNS name query, with the threat of cache poisoning
